Safari Updates Add Extra Layer of Java Protection
Further locking down Mac OS X against Java security exploits, Apple recently posted updates to Safari and new versions of Java SE 6 to close up multiple vulnerabilities. Each of the Safari and Java updates is available in two versions, with one for those running Mac OS X 10.6 Snow Leopard and the other covering 10.7 Lion and 10.8 Mountain Lion.
Both versions of Safari (Safari 5.1.9 for Snow Leopard and Safari 6.0.4 for Lion and later) introduce a new scheme for enabling the Java plug-in to run on a site-specific basis. When you encounter a Java applet on a Web site, you’ll be asked whether you want to allow the applet to run or block it. If you click the Block button, the Java plug-in will always be blocked from running on that particular Web site, though you can toggle that behavior by visiting the new site-by-site Java management settings in Safari’s preferences.
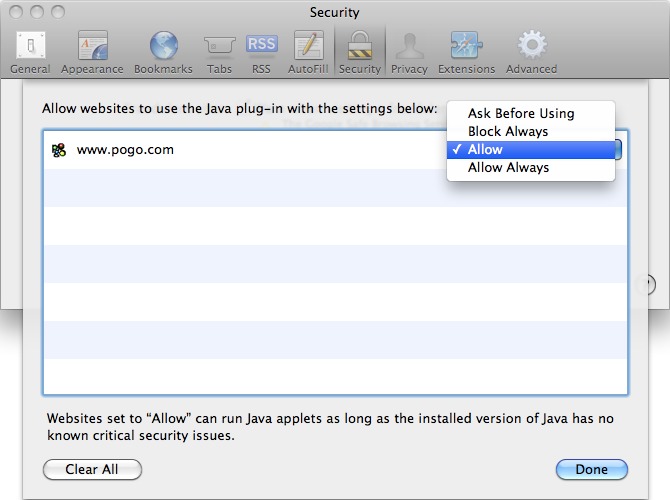
Choose Safari > Preferences and click the Security tab, then click the Manage Website Settings button to the right of the Allow Java option. A new pane appears, listing the Web sites that have encountered the Java plug-in (you cannot manually add Web sites). Click the pop-up menu to choose from four levels of Java access for that site: Ask Before Using, Block Always, Allow, and Allow Always.
The Block Always and Allow Always options are fairly straightforward in their behavior, with the Java plug-in stopped each time with the former (though the rest of the Web site will render) and always initiated with the latter. However, Apple warns that the Allow Always option should be used only for thoroughly trusted sites, such as a company intranet site (and we at TidBITS concur).
Choosing the Ask Before Using option reverts to the initial behavior of querying you whether to allow or block the Java plug-in each time it’s encountered. Note, however, that if you choose to block the Java plug-in from running when asked, the Web site will be marked as Block Always in Safari’s preferences — there’s no way to block the plug-in for a single visit (but you can always return to Safari’s preferences to allow it again).
If you choose Allow, the Java plug-in will run without bothering you as long as there are no critical security issues percolating in your currently installed version of Java. If an update is available, you’ll be directed to download that version.
In addition to the Java options, Safari 6.0.4 fixes a WebKit-related zero-day vulnerability that was uncovered by the Pwn2Own hacking competition in March 2013. According to Apple’s security notes for the update, the update closes a hole with SVG files that could lead to the standard “unexpected application termination or arbitrary code execution.”
On the Java side of things, both Java for OS X 2013-003 (63.92 MB) and Java for Mac OS X 10.6 Update 15 (63.39 MB) update Java SE 6 to version 1.6.0_45, which eliminates a large number of vulnerabilities found in the previous version of Java (version 1.6.0_43). The updates mirror the changes made to the latest version of Java SE 7, which is available only from the Oracle Web site, since Apple stopped releasing its own versions of Java with version 7 (see the release notes for 1.7.0_21).
All of these updates are available via the App Store app (Lion and Mountain Lion) or Software Update (Snow Leopard) and direct download, apart from Safari 6.0.4, which must be downloaded from the Mac App Store. For the Java updates, Apple reminds you to quit any Web browsers and Java applications before installing.
As we noted in the last round of Java updates, this might be a good time to remove Java entirely from your system if you don’t rely on Java for any critical applications. Some major apps that still use Java include CrashPlan, Adobe Creative Suite, Minecraft, and OpenOffice. To learn how to extract this increasingly troubled technology from your Mac, check out Rich Mogull’s Macworld article on disabling Java, which also includes instructions on how to isolate its use in the Safari, Chrome, and Firefox browsers.

This is getting ridiculous. So Apple quit updating Java. But Apple is still updating Java.?? I am so confused about Java versions when it comes to Apple. I'm also still pissed off at Apple for breaking my computer when it decided that I could no longer run Java whether I wanted to or not. I decided to only run java from Oracle, and no longer update via Apple. Can someone tell me if I'm in imminent danger of something dreadful if I only use updates from Oracle?
My guess is Apple decided it's customers should not wait the added delay caused by Apple implementing changes to Java AFTER they are made available by Oracle. So, as of Java 1.7 and on, it's between you and Oracle.
Apple still has responsibility for Java 1.6.x on Mac, so they continue to release updates for as long as Oracle does. Imho, you are better off installing all updates offered by Apple.
As for Apple blocking Java in OS X, they do so in their users' best interest. It's foolish to believe they wouldn't care about their customers.
Although I am also dependent of Java for some important stuff, I am actually happy that they take an active stance in protecting my use of my computer.
This mess is not caused by Apple. It is caused by criminals exploiting weaknesses in Java. It is a fact of life that some will try to take advantage of others. If you must point fingers, at least get your facts straight before picking a target...
My facts are straight. Apple failed miserably at communicating, thereby creating quite a bit of confusion when suddenly Java no longer worked on Macs. I doubt I am the only one that was unable to get critical work done and had no clear idea why or when that would change. As a 20+ year user of Macs, I think this was a serious communication error on Apple's part. I'll get over it, but I haven't forgiven them quite yet.
Maybe I misread your post. You are right about Apple not communicating this clearly.
One Google search for "Mac block Java" turns up countless useful hits describing what has been going on. So I had minimal trouble understanding the issue...
Many commenters on the Macworld article point out that some programs and services require the JAVA program to operate and that for security it is sufficient to disable the JAVA plugin in browsers. As a neophyte in this matter I'm wondering if it is possible to disable the JAVA plugin and, in browser preferences, leave Javascript enabled?
Yes, absolutely. Java and JavaScript share only four letters in their names, nothing more. :-)