Make Sure You’re Getting OS X Security Data
A few weeks ago, Josh Centers wrote about an update to OS X 10.11 El Capitan’s System Integrity Protection that broke Ethernet for many Mac users briefly, before Apple pushed out a second update to resolve the problem (see “El Capitan System Integrity Protection Update Breaks Ethernet,” 29 February 2016). Josh’s article confused me for a bit, because the problem revolved around El Capitan’s Incompatible Kernel Extension Configuration Data file, but I could find no evidence of it being installed on either my iMac or MacBook Air.
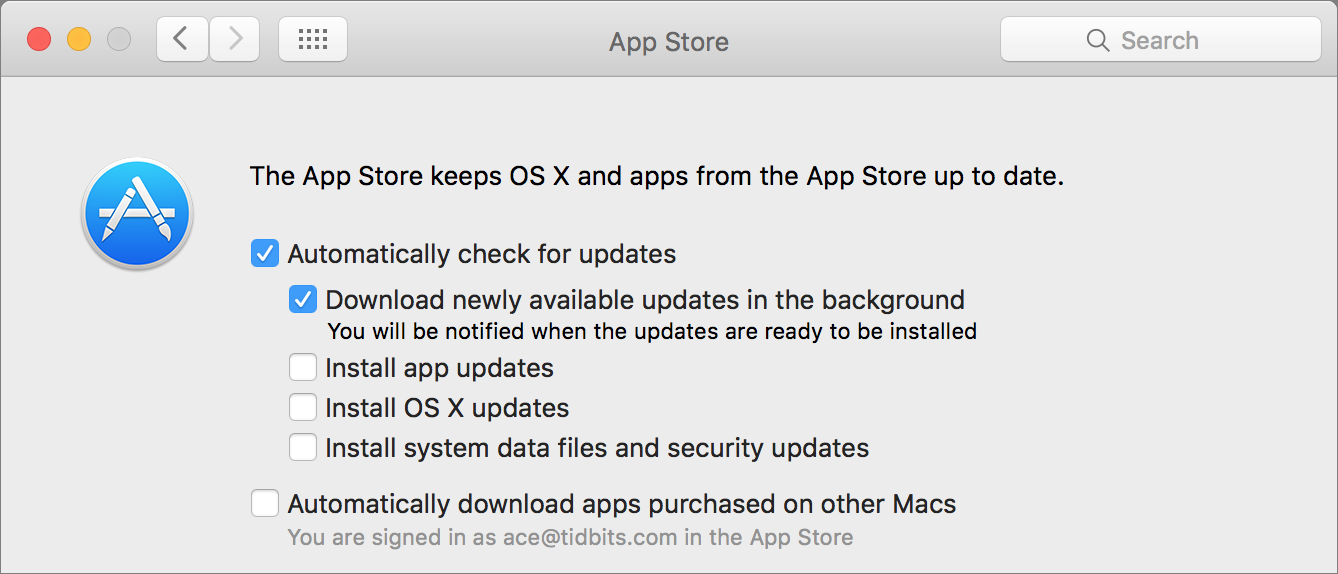
Discussion in the comments on that article and on TidBITS Talk revealed the answer: I had not selected the “Install system data files and security updates” checkbox in the App Store pane of System Preferences.
(No time to read more of this article right now? Just make sure that checkbox is selected and get on with your life. We now return the rest of you to the regularly scheduled explanation of what’s going on.)
Why had I avoided such an important-sounding checkbox? Because Apple messed up the interface here in a big way. The top enclosing checkbox is clear: “Automatically check for updates.” Everyone should have that checked. The next one isn’t as simple: “Download newly available updates in the background.” That’s fine in most cases, but if you give network-connected presentations or are in bandwidth-constrained situations where Internet use without your knowledge might be problematic, turn it off. However, note what the interface says next: “You will be notified when the updates are ready to be installed.” Great! That’s exactly what I want to have happen — updates will be downloaded in the background and then I’ll be
notified and get to choose when to install.
It would seem that the next three checkboxes are related, but that’s where Apple messed up. The next two — “Install app updates” and “Install OS X updates” — sound like “Install system data files and security updates,” but they work differently. When selected, those first two checkboxes tell the App Store app to install app and OS X updates automatically; if you leave them deselected, you’re instead notified of updates and given the opportunity install to them manually at a convenient time.
In contrast, if you fail to select “Install system data files and security updates,” you won’t be notified of these critical background security-related updates. These are not the same as Apple’s foreground updates with names like “Security Update 2016-002” — they fall into the “OS X updates” category.
So what are they? TidBITS Talk member Al Varnell, who works in the security community, shared what he knows in the discussions there, but warns that the information is incomplete because Apple has avoided documenting these systems due to the security implications. These critical background updates include at least the following:
- Core Suggestions Configuration Data
- CoreLSKD Configuration Data
- Gatekeeper Configuration Data
- Incompatible Kernel Extension Configuration Data
- MRT Configuration Data
- XProtectPlistConfigData
I assume some of these files contain information used by security processes, as outlined in this Apple support article. Gatekeeper enables OS X to avoid opening applications that aren’t signed. MRT likely stands for “Malware Removal Tool” since it appeared around the time of the MacDefender malware (see “Apple Responds to Increasingly Serious MacDefender Situation,” 25 May 2011) — Apple’s Security Update 2011-003 could detect and remove MacDefender. And XProtect is part of OS X’s File Quarantine feature, which scans downloaded files for malware and blocks Web
plug-ins with known vulnerabilities like Flash and Java. Incompatible Kernel Extension Configuration Data helps OS X disable old kernel extensions that may cause crashes, but it’s unclear what Core Suggestions Configuration Data and CoreLSKD Configuration Data contain. (You might also see Chinese Word List Update; I presume that’s not security-related.)
Apple needs to push out updates to these files based on new threats — if Apple’s engineers become aware of a new piece of malware, OS X’s security systems need to know about it as soon as possible to protect Mac users around the world. Disabling the “Install system data files and security updates” checkbox is, frankly, a terrible idea — it’s not installing code, and barring a mistake like Apple made in accidentally adding the Ethernet kernel extension to the Incompatible Kernel Extension Configuration Data file, it’s unlikely that allowing this security-related data to be updated could cause many problems.
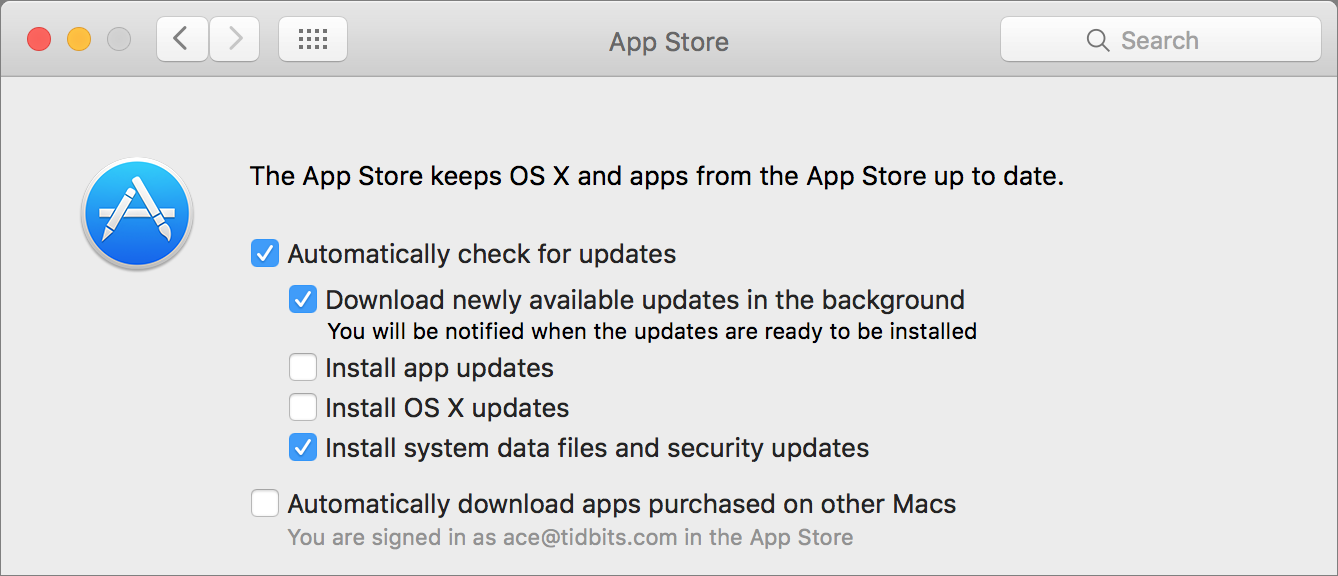
So if you’ve deselected “Install system data files and security updates,” turn it back on and wait a day or two for Software Update to notice and update everything.
If you don’t want to wait, select that checkbox and then issue this command in Terminal.
sudo softwareupdate --background-critical
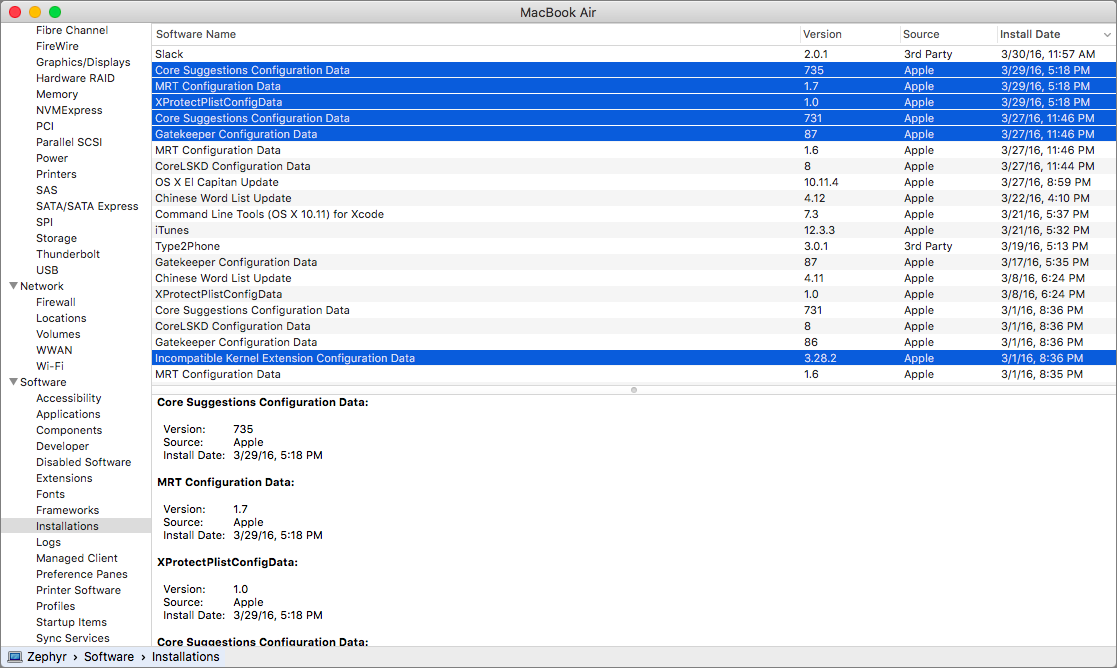
To verify that the updates have taken place, look in the Software > Installations category in System Information (as explained in “El Capitan System Integrity Protection Update Breaks Ethernet”) — click the Date Installed column header twice to sort with the newest installations at the top.
For those who are constitutionally opposed to automatic updates, this is how you can get these critical background updates manually: select the checkbox, run the softwareupdate command above, verify that the updates have taken place, and then deselect the checkbox again.
It’s worth noting that, despite Apple’s policy of releasing security updates only for the current version of OS X and two versions prior, the company continues to update these security data files all the way back to 10.6 Snow Leopard, when the File Quarantine feature made its debut.
Regardless, Apple should clarify the importance of this checkbox by rewording it to something like “Install critical anti-malware definitions and system data.” Having it selected is presumably already the default, but wording like that should prevent unwitting users from disabling it. Plus, if that checkbox is not selected, Software Update should notify the user about each individual update, just like any other OS X update.
To me the crucial question is if disabling it means I will NEVER EVER get these updates, for example as part of an OS X update or a security update.
If so, then I might turn it on once in a while. If not, I'll leave it turned off.
The reason is really quite simple. Same reason I don't allow any other auto-updates. Apple simply screws up too often. If I can't trust their updates won't cause any issues, I need to stay in control myself. That way, when things do go south I at least know where to start looking and I have an idea about how to fix things. But if I allow Apple to update all kinds of stuff all the time, how do I have any idea what it is they screwed up when my system starts misbehaving (such as in this recent totally inexcusable Ethernet snafu). Worse yet, I have no idea how stable my systems will run if I cannot control who gets to mess with what.
Nope. Until Apple gets it together and they regain their quality mojo, I will not let them auto anything on any of my systems.
I presume that all these data files are also rolled into OS X updates or more general security updates, but I haven't been able to confirm that.
I would want to think that should happen. But... When I check Software > Installations I note that neither of the ones you have highlighted in your screen shot are listed on my systems. It appears as if they were never installed. Is it possible they only get listed if they're not rolled into another (security) update?
Same on my Mac: neither of the ones highlighted in this article are listed on my system (I followed the instructions and waited 2 days, even tried the Terminal command > none of them installed). Hm?
So you're running El Capitan, you have the appropriate checkbox selected, and you tried the Terminal command, and they're still not installed?
in my case: yes, they're still not installed.
In that case, I have no idea, unfortunately. :-(
Starting in safe mode helped finally:
I tried again this time starting up in safe mode. Now it worked and the updates got installed with the sudo command. Now I wonder which Startup Item or Kernel Extension prevents Software Update from installing these security updates...
I was in the same situation. Checked the box, waited, and tried the terminal command. No luck. But after a reboot, they appeared in the installations list.
My approach has been to leave unchecked the App Store preference pane's automatic update check and to check for updates once a week when running Time Machine backups for the household. [I refuse updates to iTunes for as long as possible on the grounds that it is actually spawn of the devil rather than a useful application].
Running OS X 10.9.5, I reset the App Store checkboxes and waited some days as instructed in the article. I now, magically, have several of those 'installations' for the first time ever (i.e. no previous versions are listed in the table displayed by System Information—the earliest entry there is for the 10.8.2 update from November 2012) though perhaps they are (as you would expect) rolled into the security updates available through Software Update and so are not listed separately.
I'm about to jump to 10.11.4 and will uncheck the App Store preference for automatic update checking before I do. It will be interesting to see what default settings I'm left with afterwards.
In any event I expect to be turning on the checking regularly in order to have the latest Gatekeeper and Xprotect stuff, and to be turning it off when the iTunes nagging annoys me too much.
— — — — —
update: Having just burned a whole day failing to move to 10.11.4 I have some observations:
— reinstalling 10.9.5(13F1712) does not change the previously selected App Store system preferences and does not result in an 'installation' of the configuration files. After the reinstall I reset the App Store preferences to check automatically for security updates, and the CoreLKSD, Gatekeeper and XProtectPlist config files (with identical version numbers to the ones installed five days ago) have only just been reinstalled while I was typing these comments.
— you can no longer depend on a bootable USB installer unless you have tested it by actually installing a copy of the OS.
— I've never previously had a problem with a downloaded OS installer failing to verify or throwing fatal errors during installation. I've been using that technique without a single hitch for a number of years, but the ones I created on the 23rd of March, from OS downloads after the certificates were renewed (if that is the correct term) both failed to complete, leaving me unable to boot my working partition.
Perhaps unreasonably, I associate these difficulties with the whole sign-in-to-the-App-Store rigamarole and Apple's continuing push to tighten its grip over its users.
The updates I got after checking the Install system data files and security updates, and running the Terminal script are as follows:
Apple Displays
CoreLSKD Configuration Data
Gatekeeper Configuration Data
and XProtectPlistConfigData
By the way, I'm running OS X 10.9.5 Mavericks.
What I think I understand now, that I did not grok before or after reading Josh's article, is that the above files, among others, are installed separately from regular system and security updates. They are time sensitive, in response to particular issues, that cannot wait for a major update. Usually, but obviously not always, they are safe to install and may even be essential updates in response to specific security threats. Certainly Gatekeeper and XProtect updates are vital. I had thought that XProtect was updated routinely in the background, but it appears this may not be the case if the above mentioned App Store check box is left empty.
In any event, the Ethernet problem is the first I've heard about in connection with these "hidden" updates. So I think I will leave the box checked. Now that Apple is taking security more seriously, I think I should do so as well. I guess I lucked out in not having these updates turned on when the Ethernet problem cropped up. Or perhaps is was an El Capitan issue only.
I, too, am concerned about the reliability of Apple's quality control these days, but I figure I must draw the line on trust somewhere. YMMV.
As Adam points out, Apple's terminology in the App Store preference pane is less illuminating than it could be. For example, I deduce from this discussion that what "security updates" means in the context of the App Store preferences is these small interim updates rather than the major security updates we see in the App Store. Again, Apple could be more forthcoming on these questions. Obviously, even though they provide us some options, they would prefer we leave everything on automatic. They don't actually expect us to think about what we are doing, let alone know what we are doing.
Big Brother, ya know.
Thanks, Adam, for the clarification. I had the Install system data files and security updates box unchecked because Josh's article did indeed have me confused—as the flawed update apparently came via that route. After reading your article I checked the box and used the Terminal as you directed to download the latest updates—and then verified that some were installed with Software>Installations. Four files were downloaded and installed after I ran the Terminal command.
The problem I have with downloading updates in the background is that the notifications don't say what software is ready to be installed and, like some others, I don't like to blindly install stuff, even from the App Store. So when I see an update notification, I cancel it and go to the App Store to see what updates are listed there. I invariably download and install them, but this way I actually know what I'm getting. It may be less efficient, but it keeps me in the know. Apple could save me (and probably many others) some trouble if their notifications were less cryptic, but, hey, that would be too much to ask, right? Apple actually giving us the information we need to make an informed decision? No way. That's not how they roll. We're just dumb users. What do we need with good information? Let Big Brother Apple take care of it.
Sorry to sound so bitter, but I don't like being condescended to. And Apple is nothing if not condescending. Remind you of some other big tech company?
This is an awkward situation because the changes to these files aren't likely to be things that anyone would understand (they're signatures for malware, basically) and it's also something that Apple doesn't want to publicize heavily for fear of telling the bad guys something that would be useful to them in circumventing the protections. I think the Ethernet problem with the Incompatible Kernel Extension Configuration Data was just bad luck — XProtect has been in place since Snow Leopard with no significant issues that I'm aware of.
For more on this from the sysadmin perspective, read
https://macops.ca/os-x-admins-your-clients-are-not-getting-background-security-updates
One more data point. I followed the instructions, and everything seemed to work. The files from the article were not there before running sudo, and they were there after running sudo.
The response in Terminal was "Triggering background check with forced scan (critical and config-data updates only) ...". It sounds like running the command in Terminal makes the checkbox in the App Store preferences unnecessary, if the user remembers to check for updates using sudo regularly.
One unrelated question: where would I set the password for root? It seems like root should have a password that isn't the default password.
Edit: the macops.ca article that Adam cited says my idea to use sudo and leave the checkbox cleared will not work, because the updates will be downloaded but not installed.
Yep, that checkbox needs to be selected for the Terminal command to work. Crazy but true.
As far as the root user goes in El Capitan, I haven't looked into seriously, since there's almost never any need to enable and log in as root, but you can read more about it here. (By default, root isn't even enabled.)
http://www.macworld.com/article/2948140/os-x/private-i-el-capitans-system-integrity-protection-will-shift-utilities-functions.html
My concern was someone else being able to login as root using a default password. As long as root cannot be enabled remotely, I'll leave well enough alone.
If you haven't looked into it, I don't need to look into it.
Yep, root is not a security hole in OS X.
There is no App Store pane of System Preferences on my MacBook Pro running 10.11.3 (More exactly, when in the App Store, "Preferences" is not an option under the App Store Menu.) . I can't find a preference pane for the App Store in my /System Folder/Preferences folder, either. What do I do now?
The only way I can imagine that there wouldn't be an App Store pane in System Preferences is if you are using the Finder with some sort of parental controls enabled.
It's in the fourth row down, third icon over, if you're viewing System Preferences as organized by categories; it's often easier to switch System Preferences to alphabetical organization by using View > Organize Alphabetically, where it's the second icon from the top.
The App Store app itself has no Preferences command (which is equally bad design).
It sounds like Susan is looking for the App Store preferences pane somewhere other than in System Preferences. I apologize if I'm misreading that. To be clear, one should go to the Apple menu and select System Preferences, and then find the App Store preferences in the fourth row, third icon, as Adam said. The preferences are not available from the App Store program.
Having said that, the computer my spouse uses at work does not have an App Store in System Preferences. This could be because it is a corporate computer or because it has an old (10.6?) version of MacOS.
Ah, yes, if the computer is managed by an employer, that could account for the App Store pane not appearing in System Preferences.