Apple Pushes Updates to Block the Root Vulnerability Bug
[Editor’s Note: This article is a significant update to “Update Immediately to Block the Root Vulnerability Bug” (29 November 2017), since so much information changed since we first published that piece. This article supplants the previous one. -Adam]
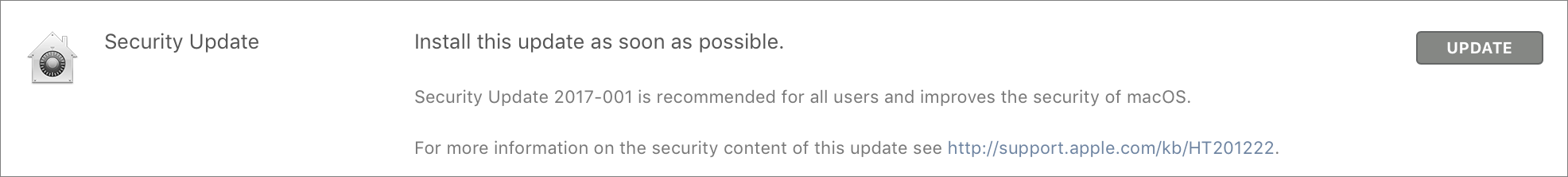
If this is the first you’re hearing about the root vulnerability bug that was discovered and patched last week, you can read “High Sierra Bug Provides Full Root Access” (28 November 2017) for details about how it allowed anyone to gain admin access to your Mac without a password. As I predicted in that article, Apple quickly released Security Update 2017-001 to fix the bug. I have installed the update and confirmed that it works as advertised.
On 29 November 2017, Apple initially made Security Update 2017-001 available as a regular download via Software Update, but later that day, the company started using the automatic update mechanism built into macOS to push the update to all Macs running High Sierra, both versions 10.13.0 and 10.13.1.
No restart is necessary, so Apple can install the update without requiring interaction from the user. We believe that a Mac must be awake for the automatic update to install since we’ve seen it appear on a MacBook Pro that was awake, but not on a MacBook Air that was sleeping all day (lazybones!).
If your Mac has been asleep since Apple released Security Update 2017-001, you’ll see it in the Updates tab in the App Store app, and you can still install it manually. We usually recommend caution when it comes to installing updates, but this vulnerability is so severe that the fix is more important than any trouble it could conceivably cause.
In fact, it did cause problems. Apple released two versions of Security Update 2017-001 last week. The first updated High Sierra to build 17B1002, and the second to build 17B1003. (To verify that number, choose > About This Mac and click the Version 10.13.1 line.) The second version was necessary because the first broke authentication for file sharing. We didn’t test file sharing after installing the first version of the update because the original bug didn’t affect file sharing.
If you installed Security Update 2017-001, and your build number is 17B1002, Software Update should offer you the update again; install it manually to fix the file sharing bug and move to build 17B1003. On my iMac with build 17B1002, no automatic update took place before I updated again manually, but other users received the automatic update after installing the first update manually.
For those who need a standalone installer for Security Update 2017-001, Apple has made downloads available for both 10.13.0 and 10.13.1.
If you have a legitimate use for the root user account on your Mac, you’ll need to re-enable it and change its password in Directory Utility after installing the update. Hardly anyone should have to do this.
Why all this fuss? Although the Mac community identified the primary attack vectors on 28 November 2017 when the vulnerability was first publicized, it’s possible that there are others that are not blocked by changing the root password or disabling remote access. We have to assume that black hat hackers are probing every possible area where this bug could provide access. That’s why it’s entirely reasonable for Apple to push the security update to all systems.
In an early statement to John Gruber of Daring Fireball, Apple said:
Security is a top priority for every Apple product, and regrettably we stumbled with this release of macOS.
When our security engineers became aware of the issue Tuesday afternoon, we immediately began working on an update that closes the security hole. This morning, as of 8:00 a.m., the update is available for download, and starting later today it will be automatically installed on all systems running the latest version (10.13.1) of macOS High Sierra.
We greatly regret this error and we apologize to all Mac users, both for releasing with this vulnerability and for the concern it has caused. Our customers deserve better. We are auditing our development processes to help prevent this from happening again.
Apple deserves credit for releasing this security update in less than 24 hours after the bug was publicized on Twitter. That quick reaction time is reassuring, much as I’m sure many developers, testers, and deployment teams at Apple had a truly awful day.
But the fact that Apple could introduce a security hole the size of a truck into High Sierra is appalling. Ensuring that unauthorized users can’t act as the root user in a Unix system is basic security, because anyone who can become root can do anything they want. That the vulnerability escaped notice in Apple’s security testing is almost worse than the bug itself, and the initial release of Security Update 2017-001 breaking file sharing authentication is also distressing.
And yes, if you’ve been waiting to upgrade to High Sierra, pat yourself on the back. 10.12 Sierra and earlier versions of OS X don’t suffer from this bug.

I received a High Sierra upgrade notification for the first time this morning. Is it safe to assume that it already contains the Security Update?
To upgrade from Sierra? I'd be a little surprised if it included the security update so soon, but it's easy to check the build number to make sure you end up at 17B1003. If not, just look in the Updates tab of the App Store app again.
There's an update - available via MAS on 11-30-17 - to the initial, SU 2017-001, which changes the 10.13.1 Build to 17B1003 as well as fixing the File Sharing issue.
A prime example of poor Apple software management and reason to always delay in upgrading OS software.
The security issue doesn't surprise me. It's obscure. The issue came up when a user accidentally made all of their users non-Admin users. Someone came up with the fix by using this security flaw, but then didn't even realize it was a security flaw. Only weeks later was it detected. Security is tough.
So if the mac is told there are no admins it says "Ho! There should be at least one! Let's create a minimal one..." Is that it?
I installed the update yesterday manually, and was automatically updated today. The build number I have now reflects the latest build and the root issue has been patched.
Twice updated. The macOS version is now 17B1003
The bug was known weeks earlier and had been published in Apple discussions fora, but had apparently not come to the attention of Apple.
I had inadvertently used this bug on 22 November to fix my daughter's laptop when all log in accounts suddenly lost their "admin" status. Google found that article in the forum about logging in as single user with root and no password which I tried and it worked.
I remember thinking at the time that it was odd that I could do that, but then let it slide as I was pleased that I could create an admin account and fix the problem.
Not sure where the article went, I started with this one:
https://discussions.apple.com/thread/7725393?start=0&tstart=0
and I feel sure that article previously made mention of using "root" no password, but that reference is gone.
What I would love to know is why the admin status of all of the accounts disappeared.
Thanks for that explanation, Rob. I'd been puzzled by the posts I've read claiming that this 'bug' has been known about for weeks and was a remnant of a HS backdoor testing protocol which wasn't removed before the software went GM.
Plenty of people have been beating up on Apple for not monitoring their own forums. It's unconscionable for a problem (not this one) to have hundreds of posts on an Apple forum thread and yet have Apple claim they've never heard of it.
Yea, the proper way is to file a formal bug report but Apple ought to have someone tasked with monitoring their own forums. When a thread breaks some threshold, it should be looked into by the appropriate engineering team. Time for Federighi to stomp out that NIH (Not Invented Here) mentality.
Really, it's time someone told Apple to slow down its release schedule and return to the standards that used to make Apple products a benchmark for quality. I don't know anyone who's agitating for more and faster feature releases; on the contrary, most of my group would like more stability and fewer new features.
Does anyone know whether Apple is working on the Intel Management Engine problem (http://www.zdnet.com/article/computer-vendors-start-disabling-intel-management-engine/)? That might make for a useful followup TidBits article.
There's by no means user demand behind the forced annual major release schedule. It's all marketing. Stability/quality be damned.