Authy Protects Your Two-Factor Authentication Tokens
Digital security has been a hot topic this year. Between the theft of private celebrity photos (see “iCloud Flaw Not Source of Celebrity Photo Theft,” 2 September 2014) and multiple credit card leaks, it’s hard not to feel a little paranoid.
One of the best ways to improve your online security game is two-factor authentication. In short, two-factor authentication adds an extra layer of security to your password (something you know) in the form of a number that’s regenerated every few seconds, either by a dedicated device or a mobile app (something you have).
The free Google Authenticator has become the de facto industry standard in two-factor authentication. You can use it with your Google account, but it’s also compatible with Dropbox, Evernote, Facebook, Tumblr, and many other online services.
While Google Authenticator gets the job done, it has a number of potentially significant limitations. It offers no backup or sync, so if you lose the device it’s installed on, or wipe the data off that device, you’re in for a world of hurt (for an example, see “Dancing the Two-Step: Coping with the Loss of a Second Factor,” 28 August 2013). One Google Authenticator update accidentally wiped everyone’s two-factor tokens, preventing users from logging into their accounts.
Thankfully, there’s an alternative: Authy, which is free for iPhone and iPad in the App Store.
Authy has numerous features that Google Authenticator lacks. Authy can back up your two-factor tokens to the cloud, so if you wipe your phone or get a new one, you can restore those tokens and not be locked out of your accounts. Authy can also use the cloud to sync to your other devices, and the app is universal, so it works equally well on your iPhone or iPad. And if you own a newer Mac with Bluetooth 4.0 LE (I sadly don’t), you can take advantage of the complementary Authy Bluetooth app to insert your two-factor tokens on the Mac automatically, with no additional typing required.
Authy’s Tradeoffs — Hearing that Authy uploads your two-factor tokens into the cloud might make you nervous. But keep two things in mind. First, cloud-based backups are entirely optional and are off by default. Second, Authy encrypts your backups on your device before uploading them.
Regardless, as with all security decisions, Authy’s cloud features come with a tradeoff. Whenever you store sensitive information on someone else’s server, you increase the risk that it will be stolen, even if only infinitesimally. But also consider the benefits. With Google Authenticator, if you lose your iPhone, you lose access to your accounts, at least temporarily. Which scenario is more likely and/or more frightening: a single account being hacked, or losing access to all accounts due to a software glitch or a broken phone?
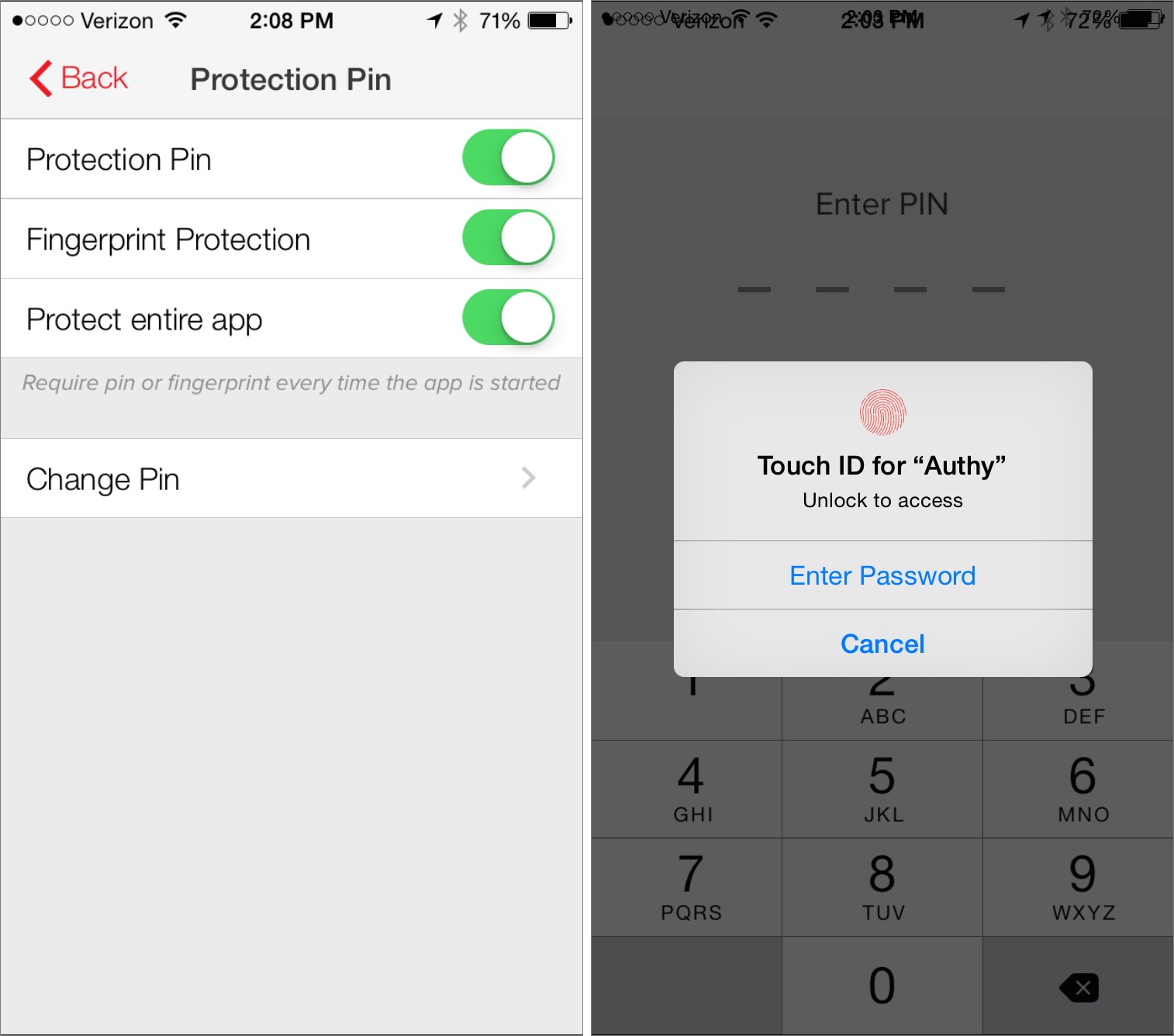
Authy also adds a critical security feature that Google Authenticator lacks: the option to lock the app with a PIN or Touch ID, so a thief who got past the device’s overall passcode can’t view your tokens.
Even if Authy were found to be vulnerable, online accounts protected by two-factor authentication would still be more secure than those that rely solely on a password. In addition to cracking the account password, an attacker would also have to crack your Authy password. Conversely, even if an attacker were to infiltrate your Authy account, the tokens would be useless without account passwords. Such accounts are still twice as hard to hack as those that have only a password.
For me, the decision to use Authy is simple. It lets me protect my accounts with two-factor authentication, and it reduces the likelihood of the problems from which Google Authenticator suffers.
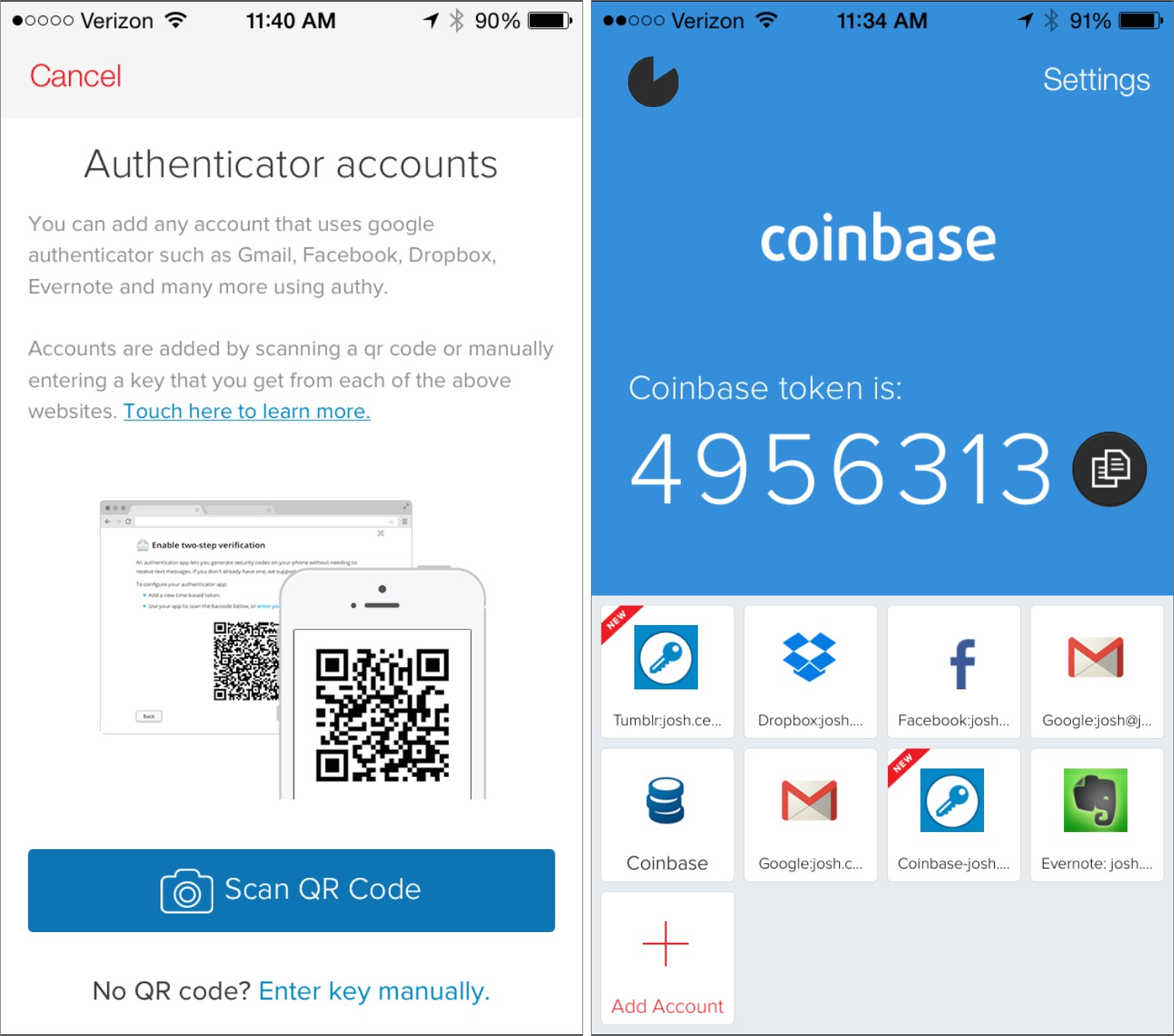
Using Authy — Authy is pretty easy to use, as two-factor authentication goes. First, you need to set up an account token. Tap Add Account at the bottom of the screen, and then either scan the QR code provided by the online service, or enter a provided code. The specifics of how you obtain either will be different with each service.
Once you’ve added one or more accounts, they appear at the bottom of the screen. If you have more than four, the row of buttons at the bottom of the screen turns into a drawer that you can expand to see additional accounts and the Add Account button. To display the necessary time-limited token that you need to enter to log in to a two-factor-protected site, simply tap an account. Be mindful of the timer — a token typically lasts only 30 seconds before it expires. If there are only a few seconds left in a token’s life, it’s easier to wait for the next one. If you’re logging in from the iOS device itself, you can also tap the blue copy button next to the token to put it on the clipboard.
If you want to manage accounts or set up additional security protections, tap Settings in the upper right. In the Settings screen, the My Account pane lets you set what phone number and email address are tied to your Authy account. These are important: when you move to a new iPhone, Authy will ask you to use one of these contact methods to prove your identity. You can also set a Protection PIN and/or Fingerprint Protection here, which I recommend. If your device supports Touch ID, I think it’s silly not to enable
Fingerprint Protection, because it adds that much more security with little hassle.
The Accounts pane lets you manage your tokens and set better names, but perhaps more important to new users, it’s also where you set up cloud backups and change your backup password.
The Bluetooth pane merely lets you allow Authy to use Bluetooth to talk to the Authy Bluetooth app, if that option is available to you.
Finally, the Devices pane lets you set up and manage multi-device support. Activating other devices works by what Authy calls Inherited Trust. In other words, when you try to use the same Authy account on another device, you must approve it from an already authorized device. In practice, this seems like a good balance between security and convenience.
Boarding Up the Windows — These days, digital security is kind of like a zombie apocalypse movie. You can stock up on supplies and board up the windows, but sooner or later, probably through simple human error, a zombie will break in.
But just because your efforts may be futile in the end doesn’t mean you stop nailing boards. At the same time, you don’t want to put up so many that you can’t get out when you need food.
That’s roughly how I see Authy. While, by the developers’ own admission, its cloud features can potentially make you less secure, they also make it harder to lock yourself out of your digital house.
Also keep in mind that Authy does only one thing — it’s not a silver bullet for online security. It won’t prevent your credit card number from being stolen from a retailer, nor, thanks to Apple’s weird two-factor authentication implementation, could it have prevented Jennifer Lawrence’s pictures from being stolen.
Authy is just another tool in your security kit, but a useful one that makes two-factor authentication less intimidating.
Thanks. I heard Casey Liss mention Authy on ATP recently, but I wasn't sure how much of an advantage it'd be for me. Your rundown makes me want to try it.
Saying that "it offers no sort of backup or sync" is somewhat inaccurate. While it is true that there is no built-in sync method, keeping a copy of the authenticator setup code (usually a QR code) is not difficult at all. I keep copies of all of my QR codes in my 1Password, attached to their respective logins. So if my Authenticator should ever malfunction, or if I had to replace my iPhone, I could easily rescan them. And, since my 1Password file is synced via Dropbox, my authenticator tokens are thus backed up in the cloud. Similarly, "It can only be tied to one device at a time" is also untrue. I have Google Authenticator installed on both my iPhone and iPod touch, with the same exact tokens on both devices. I just scanned the QR codes for the various services I use two-factor auth with (Dropbox, Evernote, etc.) on both devices.
I removed the part about Authenticator working with only one device at a time. However, in the past, I tried setting Authenticator up on my iPad, on for my iPhone's codes to stop working. Maybe it was a bug, or something else has changed?
That's a good tip about saving the QR codes. I hadn't thought of that.
Another Authy feature is access to tokens on OS X (or Windows) via a Chrome web app.
Does that present any security concerns?
Perhaps, since if Chrome were to be vulnerable, that might put your tokens at risk. Again, you have to weigh convenience against security. But I don't have a problem typing the code manually every now and then.
Concerning the Google Authenticator I missed a reference to the list of backup codes that you can use if you loose your mobile device. Thus I do not understand why I would need the backup to the cloud that Authy provides.
Those are great if you remember to save them. Unfortunately, a lot of people don't. (You should both print them out and save them to a secure vault like 1Password.)
One possible scenario in Authy's favor. Imagine you're traveling and your iPhone is lost or broken. You can buy a new iPhone and redownload Authy and get your tokens back from the cloud backup.
If you used Google Authenticator, you'd need those backup codes, but if you use two-factor authentication heavily, you might not be able to put them all in your wallet. Storing them in 1Password or the like might work, but only if you're not reliant on a two-factor service to restore that app's data first.
Overall, I suspect that relying on the backup codes could be made to work, but it would require a lot of effort both ahead of time and in the moment, whereas restoring codes from Authy's backup would be much faster and simpler.
That said, I'm currently putting accounts into both Google Authenticator and Authy right now - I find Google Authenticator's single-screen approach easier to use, and it's only a minute more work to scan the QR code into both apps.
The Bluetooth authentication Authy app on OS X has been end of lifed.
The only supported Authy option that works on OS X is their Chrome App version.
Where are you seeing that? Their site still talks about it as though it's a continuing product.
https://www.authy.com/thefuture
Two (Four, see post below) things. First, when you are on their site and click on the OS X logo on the "Users" page https://www.authy.com/userssit takes you to download the Chrome App version, not to the Mac App Store (where the version hasn't been updated in nearly a year).
Second, a review by mjj0929 on 9/1/14 on the Mac App Store said:
"When I wrote to Authy to ask for help with this, they told me they were discontinuing it because the Bluetooth technology isn't there to support this fully.
"They suggested downloading the Chrome App instead, which I've done and it works fine. It's not as seamless as this was (when it worked), but it's the same end effect.
"So don't bother downloading this, finding it doesn't work, and leaving a bad review. They know it's unstable and are shutting it down"
Applying Occam's Razor to the OS X link, the age of the Mac App and this review, it has been discontinued.
Given your journalistic cred, maybe you can get them to address this directly.
Third, forgot to note that on the same page the Windows and Linux icons also send you to their Chrome App.
Fourth, clicking on the Features and Benefits button in the "For your desktop" section sends you here:
https://www.authy.com/apps/two-factor-authentication-for-pcsbrs/>
where it touts the cross platform nature of its Chrome App and has icons to take you to both the iOS and Chrome App Store but none for the Mac App Store.
Interesting - on closer examination, the URL I found
https://www.authy.com/thefuture
seems to be an old page. All the links on it do go to legitimate downloads, but the page is accessible mostly (only?) via search, not via links on the main Authy site.
Josh, can you check in with them on this?
I'll try to get an official statement from them.
I heard from Daniel Palacio, the founder of Authy. The Authy Bluetooth isn't dead, but issues in the Apple CoreBluetooth driver make it unreliable. So until Apple fixes the driver, Authy is advising users to use the Chrome app instead. However, Authy Bluetooth is still being actively worked on.
Thanks for the clarification.
The interesting thing is that they redesigned the app for iOS 8, but left in Authy Bluetooth support. You would think if they were ending the Mac app, they would have cut support out of the iOS app.
What is the business model of Authy? I'd rather not trust a "free" app (except when it's Open Source, of course.).
They have a business-focused side, which charges companies for an integrated, centralized two-factor authentication system.
https://www.authy.com/businesses
Looking for a bit of help. I'm using google auth (GA) in many places. I didn't think to keep the QR codes anyplace. Some questions:
1) Can I re-generate the GA QR to store in 1Password?
2) Can anyone confirm that installing GA on different devices and then scanning the QR into each app will provide the same auth code in each app?
3) if you scan the same QR into both Authy and GA, will it generate the same auth code?
4) Any advice on how to move from GA to Authy? Do I turn off 2-factor in each spot, then re-start it. I assume that gets me a new QR code, right?
I think regenerating QR codes would require different actions on each site. I did this on Zoho recently by switching to SMS notifications and then switching back to Google Authenticator immediately - it gave me a new QR code. That should also let you move from GA to Authy.
Scanning the same QR code into both GA and Authy does indeed give you the same token. That's what I do and it works fine.
I've not used GA on multiple devices, but as long as you scan the same QR code, it should produce the same tokens.
1) Yes, but when you regenerate the QR code it creates a new key so any prior Authenticator instance for that site/app will be no longer valid. You will also need to save the new backup codes.
2) Yes, that has been my experience and as it should be. The key and associated site/app remain the same.
3) Yes. This is an open standard implementation so, by definition, the same QR code (and embedded key) must generate the same auth code.
4) I did this a few weeks ago and it was just time consuming. Google is among the easiest because it has a "new phone" option that generates a new QR code and updates it for its accounts.
Others, have schemes where you can delete the current Authentication and then create a new one at the same time. This is pretty painless and is what I believe dropbox does.
Others require you to turn off the current 2FA, turn it back on and then generate a new QR code. Pain in the butt as you have to go through a bunch of extra hoops. Evernote and maybe Stripe?
I already had Authy for my Cloudflare account and never knew it could do Google Authenticator as well.
I read this article on the train last night and when I got home I installed it on my iPad. My Cloudflare token was immediately available.
Today, I moved all my Google Authenticator tokens to Authy. All seems fine. I got home, but my iPad still only has Cloudflare. What have I missed?
Best wishes
Michael