Google Halts Massive Phishing Attack: Check Your Account
Last week, a huge phishing campaign targeted email users with a message that appeared to be an invitation from a known correspondent to join a Google Doc. However, the linked Web page requested that you grant access to an app that looked like Google Docs, but was instead an app that sent spam to people in your contact list.
The attack was well-engineered, so although there were giveaways, such as the original message being sent to [email protected] and BCC’d to you, it suckered lots of people.
Google reacted quickly, disabling the phishing campaign within an hour and releasing this statement:
We have taken action to protect users against an email impersonating Google Docs, and have disabled offending accounts. We’ve removed the fake pages, pushed updates through Safe Browsing, and our abuse team is working to prevent this kind of spoofing from happening again. We encourage users to report phishing emails in Gmail.
Later, Google followed up with another statement:
We realize people are concerned about their Google accounts, and we’re now able to give a fuller explanation after further investigation. We have taken action to protect users against an email spam campaign impersonating Google Docs, which affected fewer than 0.1 percent of Gmail users. We protected users from this attack through a combination of automatic and manual actions, including removing the fake pages and applications, and pushing updates through Safe Browsing, Gmail, and other anti-abuse systems. We were able to stop the campaign within approximately one hour. While contact information was accessed and used by the campaign, our investigations show that no other data was exposed. There’s no further action users need to
take regarding this event; users who want to review third party apps connected to their account can visit Google Security Checkup.
Although 0.1 percent of Gmail users sounds small, it’s likely well over 1 million people, since Google reported that Gmail had 1 billion users as of February 2016.
At this point, as Google says, there’s nothing you need to do to protect yourself from this attack. But it’s a good excuse to check your Google account to verify everything connected to it.
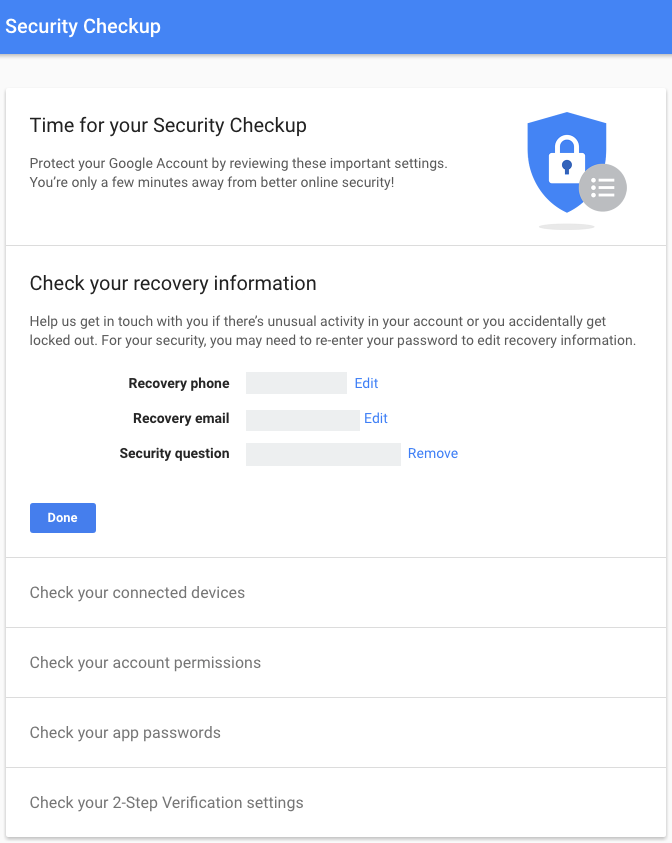
Start at the Google Security Checkup page, which walks you through checking your account recovery information, connected devices, account permissions, app passwords, and two-step verification settings.
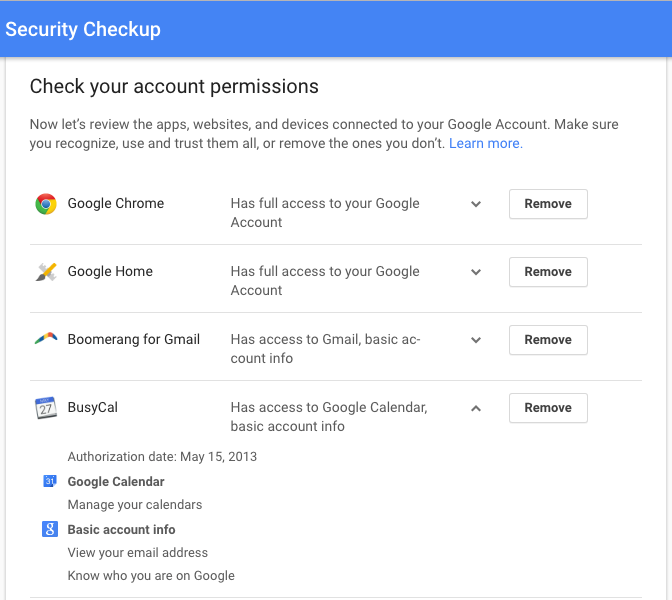
In particular, in Check Your Account Permissions, make sure to remove access for any app that you don’t recognize. Click an app to see more details about when you authorized it to access your Google account and what information it can access.
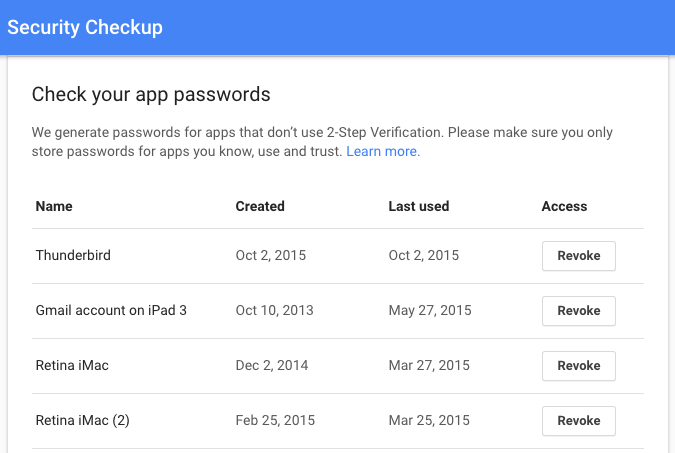
When you get to Check Your App Passwords, you may be able to revoke most or even all of them. Google lets you generate passwords for apps that don’t support its two-step verification system, but there’s no need for them in any Google-branded apps in iOS 8.3 or later, and OS X 10.10.3 Yosemite or later. Similarly, setting up Gmail in Mail in iOS doesn’t require an app-specific password, and most independent apps have been updated in the last few years. I apparently haven’t used any of the app-specific
passwords I created since 2015, so I can probably delete them all.
I’m not sure there’s much of a moral to this story, apart from encouraging you to evaluate what you read carefully, both in email and on Web pages that you might click through to from an email message, particularly if they’re asking you for a password or other personal information. Phishing messages almost always have spelling errors, grammatical flubs, or oddities with the To and From lines — no large company will make those kinds of mistakes. If an email message ever feels wrong, navigate to a linked Web page manually
rather than clicking through from the message.
But don’t get too paranoid. The vast majority of email that lands in your Inbox is entirely innocuous, and worrying about a phishing attack every time you open a message is no way to live.