Facebook Shows Why SMS Isn’t Ideal for Two-Factor Authentication
If you follow recommended security practices, you use two-factor authentication on every online service that allows it. For those who aren’t familiar with two-factor authentication, it makes it so a username and password is no longer sufficient to log into your account — you must also provide a six-digit time-based one-time password that is either sent to your phone via SMS text message or generated by an app.
(Then there’s Apple’s two-factor authentication for Apple ID-protected logins, which relies on Apple-proprietary communication channels and devices and thus breaks the usual conventions, see “Apple Implements Two-Factor Authentication for Apple IDs,” 21 March 2013.)
SMS is the most popular method of receiving two-factor authentication codes, because it’s nearly universal and easy to understand. You give your phone number to an online service, and it sends you a code to enter when you try to login. Easy. But SMS is less than ideal, as a recent Facebook issue has (once again) demonstrated.
In theory, the phone number you provide to Facebook for two-factor authentication should be used only for that. However, many Facebook users are receiving unwanted text-message notifications from Facebook — 9to5Mac gathered a number of those stories together. Even worse, if the user replies, that text get posted on their walls in Facebook! So if you were to text STOP — an entirely reasonable thing to try — it would be posted on your wall for the world to see.
Facebook was quick to respond, and Alex Stamos, Facebook’s chief security officer, said that the SMS behavior was a bug and that Facebook is fixing it. He added that Facebook is deprecating the feature that lets users post to Facebook via text message.
This is the first time we’ve heard of this sort of problem, but SMS is notoriously awful for two-factor authentication. Here’s a list of headlines demonstrating that:
- CNET: “Why you are at risk if you use SMS for two-step verification”
- Forbes: “All That’s Needed To Hack Gmail And Rob Bitcoin: A Name And A Phone Number”
- Macworld: “Your cell phone number could be hijacked unless you add a PIN to your carrier account” (Hi, Glenn!)
- TechCrunch: “Coinbase vulnerability is a good reminder that SMS-based 2FA can wreak havoc”
- The Hacker News: “End of SMS-based 2-Factor Authentication; Yes, It’s Insecure!”
- The Register: “Standards body warned SMS 2FA is insecure and nobody listened”
- The Verge: “This is why you shouldn’t use texts for two-factor authentication”
- Wired: “So Hey You Should Stop Using Texts for Two-Factor Authentication”
In short, using SMS for your two-factor authentication codes is a bad idea! Unfortunately, some Web sites force you to do just that — PayPal comes to mind. Thankfully, most online services that support two-factor authentication let you use an authentication app that can generate those time-based one-time passwords for you automatically, starting from a seed provided by the company.
In fact, Facebook supports both independent authentication apps like 1Password, Authy, Google Authenticator, and LastPass Authenticator, and provides its own code-generation capability within the Facebook app for iOS.
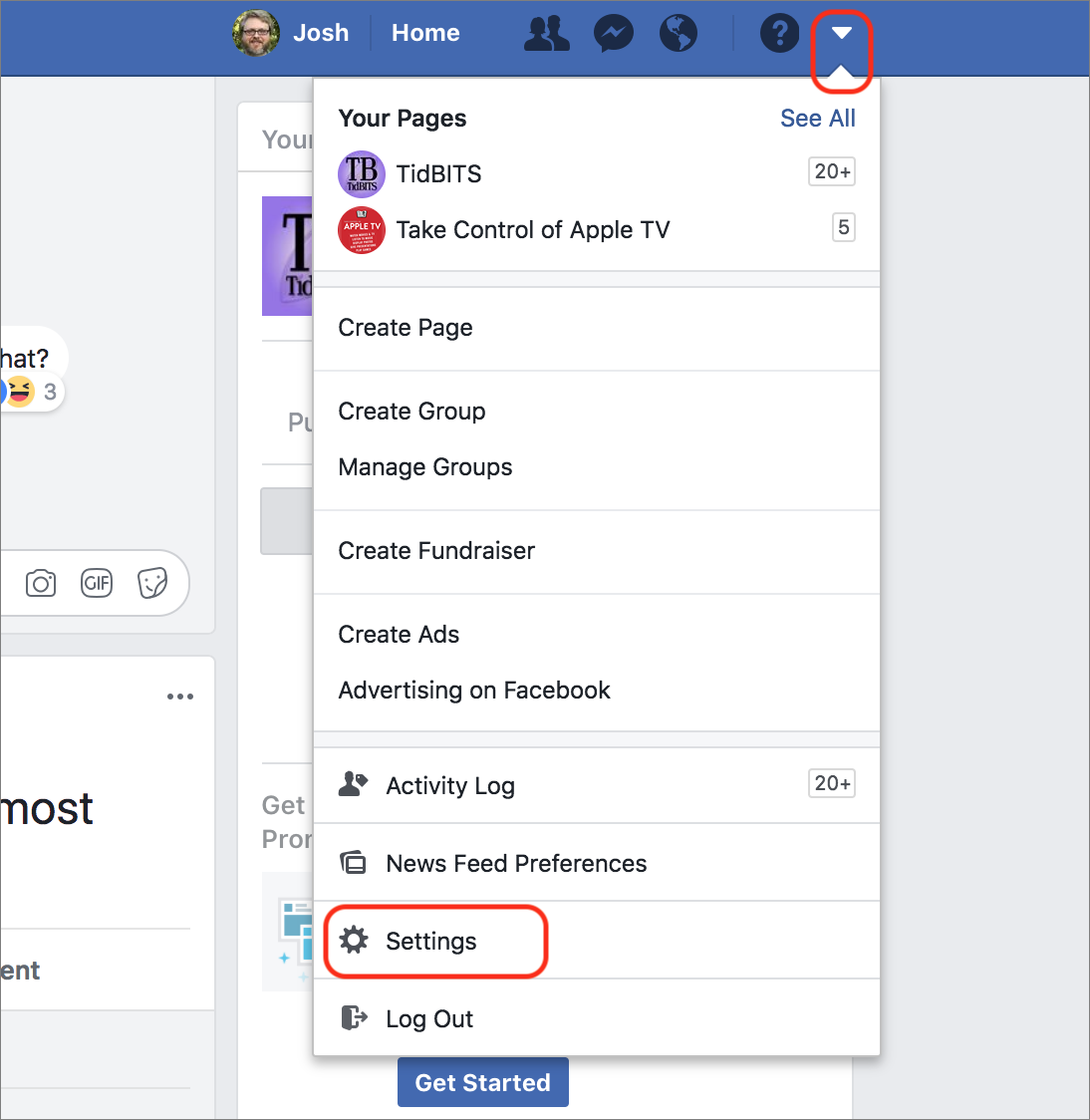
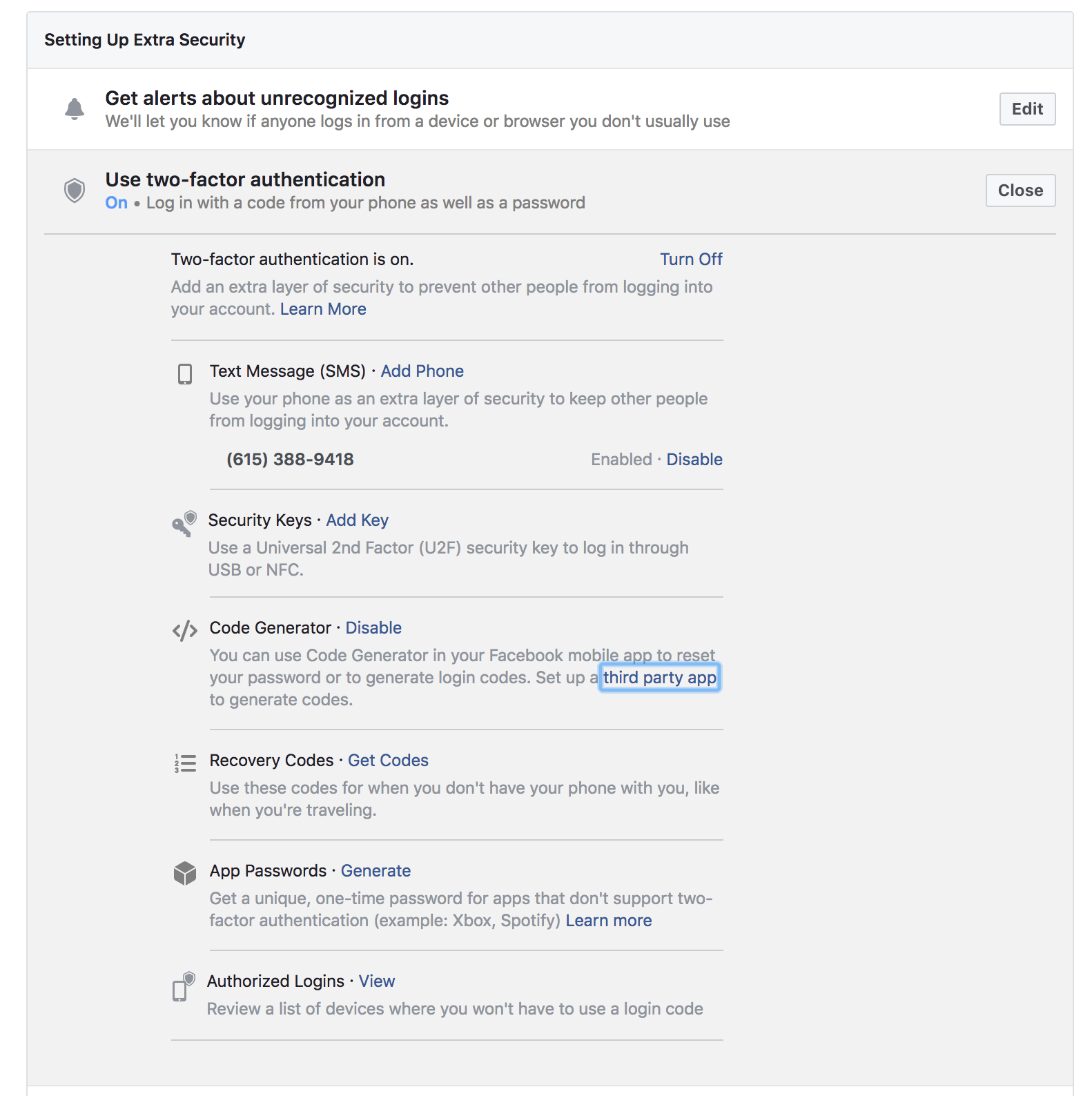
To set this up, start on the Facebook desktop Web site. Click the down-pointing arrow in the upper-right corner and choose Settings. Click Security and Login. Under Setting Up Extra Security, look for Use Two-Factor Authentication. Click the adjacent Edit button.
Look for Code Generator and click Enable. Then you can click the “third party app” link to reveal a QR code and secret key you can use to set up your preferred authentication app.
Unfortunately, you cannot disable the text message option entirely unless you also set up a USB or NFC security key for authentication, like this FIDO U2F security key. Keep that in mind if you’re worried about SMS two-factor authentication or if Facebook starts sending unwanted text messages.
While you’re in Facebook’s settings, you can also make sure you’re not set to receive text messages. Click Mobile in the sidebar. When I checked, text messaging was not activated, as in the screenshot below.
So which app should you use for two-factor authentication? I was a big fan of Authy (see “Authy Protects Your Two-Factor Authentication Tokens,” 6 November 2014) until 1Password rolled out support for two-factor authentication. I prefer 1Password’s implementation because on the Mac it copies the code to my clipboard after auto-filling my username and password. Regardless, we
strongly advise choosing a solution that offers backups or cloud sync, lest you get locked out of your accounts when you upgrade phones, as once happened to Glenn Fleishman (see “Dancing the Two-Step: Coping with the Loss of a Second Factor,” 28 August 2013).

Facebook's CSO did acknowledge it was a bug, apologized to users for the issue and said a fix is coming on both the spam and posting to walls.
https://www.facebook.com/notes/facebook-security/fixing-sms-notifications-for-those-using-two-factor-authentication/10155124741945766/
Not excusing it, but just wanted to point out that they did acknowledge it as your article alludes they were avoiding owning up to it.
Thanks, I've updated the article.
I think it’s pretty terrible that you can’t solely use TOTP with Facebook. The requirement to also use SMS or U2F seems unnecessary. So to prevent the annoying SMS notifications when I log in, I had iOS block 32665 (FBOOK) and I just use my TOTP from now on. I know it doesn’t remove the attack vector of someone intercepting my SMS, but at least it cuts back on the notifications.
Very useful reminder - I'm already using 2fa wherever I can find it, but this article prompted me to check (and improve) a few things. Many thanks. -jcb