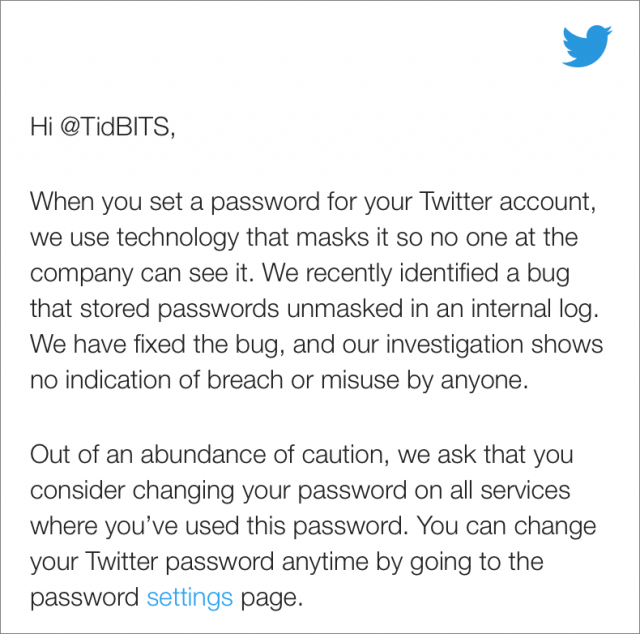
Twitter is urging users to change their passwords after a bug caused passwords to be written unencrypted to an internal log before being masked through bcrypt hashing. The company didn’t release details about how many of the 330 million active Twitter accounts were affected.
Although Twitter said that it found the error on its own and that its investigation failed to turn up any indication of a breach or misuse, the company suggests that you should still change your password. If you used that password on any other Web sites, change it there too. Situations like this show why reusing passwords is a bad idea—rely on a password manager so every site can have a unique strong password.
Enabling two-factor authentication would also protect your account even if your password was compromised. Given the trouble that someone could cause for you if they had access to your Twitter account, we recommend two-factor authentication for Twitter more than for many other Internet services.
Hi Adam. Why do you recommend 2-factor authentication for Twitter “more than many other” online accounts? What could a bad guy do if they got hold of my Twitter login?
The fact that Twitter had cleartext passwords is very concerning. I am glad I don’t use Twitter for anything having to do with my job or making money in any way. This revelation is simply horrible and shows a stunning level of idiocy in a multi=,billion dollar company. I mean, it’s been more than 15 years since I thought, “Hey, this mail software is storing clear text passwords in a password-protected database. That’s bad. I should never have someone’s password, and I trust me.”
A bad guy could send tweets making you seem like a bad person or expose private DMs (though presumably some of the same Twitter staff that had access to these logs can read those DMs anyway). I suppose if you authenticate on other sites using your Twitter account, that’s another risk but I don’t know how common that is, I would assume a lot less than using Google or Facebook instead.
If you’re not a public figure or on Twitter as part of your profession, I wouldn’t think it would be that big a deal, not compared to your primary email, a financial institution, or even Facebook.
Hardly any site requires JavaScript to do client-side hashing of passwords so almost all will have the cleartext password at the server. Logging something that shouldn’t have been (every POST to an API perhaps?) is a bone-headed mistake but to me it’s more understandable than, say, not renewing SSL certificates, something even more prominent companies have done. BTW, with 3,372 employees and 2.4 billion in revenue, I think Twitter is almost in the top 10 for revenue per employee; I’m a very light Twitter user, I’m amazed they have that much revenue.
Thank you, Curtis and kreme for your explanations. Happily I don’t use Twitter for any business-related activity. And I do use difficult and unique passwords everywhere. I am a frequent Twitter user, but only to watch and contribute to discussions of national and international politics and news.