iOS Mail Exploits Serious but Unlikely to Affect Normal Users
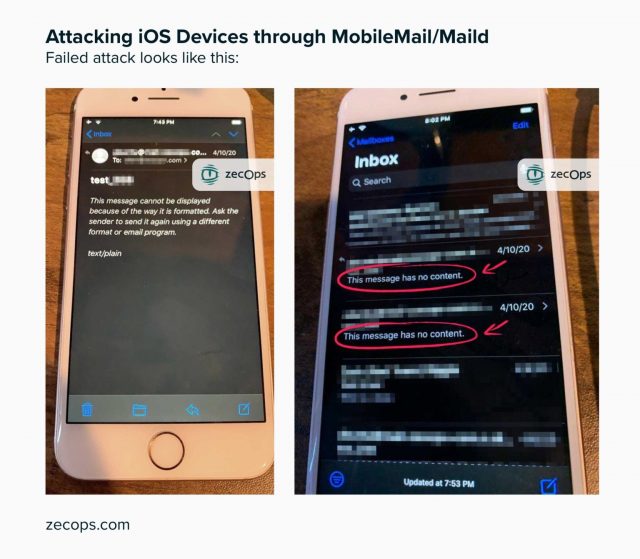
The security firm ZecOps has announced that some of its customers were hit with a pair of previously undiscovered exploits for Mail in iOS that caused the app to crash, revealing a mechanism that could be used as part of a sequence of “zero-day” attacks. In iOS 13, the vulnerabilities can be exploited merely by receiving an email message; in iOS 12, the user would have to view a malicious email message (but not open an attachment or tap a link) to trigger an exploit. ZecOps said it found the vulnerabilities as far back as it tested, which was to iOS 6, and it tracked real-world attacks back to January 2018.
However, although Apple has confirmed the vulnerabilities in Mail, they can’t be used on their own to steal information or take over devices. Any real-world attack would require additional unknown, undisclosed, high-value exploits. ZecOps did not disclose the information necessary to determine if and how its customers’ devices were compromised. Our conclusion is that the risk to average iPhone users is very low, especially with Apple already testing a fix in the latest beta version of iOS.
The two vulnerabilities are quite simple in nature. Mail fails to handle messages correctly when they use large amounts of memory. A very large attachment can cause the problem, as can a properly crafted message using Rich Text Format (RTF), multi-part attachments, or other not-yet-disclosed methods that force iOS to churn through memory. ZecOps believes attackers can delete messages after deploying them.
Apple said it has patched the flaws in the current iOS 13.4.5 beta and the next production release of iOS 13. It also affects iPadOS 13. Look for a release soon. (And no, we don’t know why it’s 13.4.5 instead of 13.4.2, as would seem logical.)
The vast majority of users don’t need to make any changes in their behavior, because the exploits have to be paired with other code to carry out malicious activities, like data exfiltration. Since a payload that can break out of Mail and perform other actions is required, the exploits are useful only to government actors or major criminal rings. Attacks would have to be extremely targeted. ZecOps listed a variety of suspected targets it had identified, which included people who work at an American Fortune 500 company, a European journalist, and a Japanese cellular carrier executive.
ZecOps has not yet released enough information on the attacks it observed in the wild to allow other security researchers to validate the company’s claim. The company said it would release proofs of concept to demonstrate how the exploits worked in practice.
ZecOps said it disclosed the vulnerabilities before the typical 90-day window had passed after reporting to a vendor because it believes these exploits pose an imminent threat. The firm said it had seen the exploits used in the wild, and that Apple’s release of a 13.4.5 beta with the fixes could provide enough information for bad actors to exploit the flaws before they were patched in a production release.
These exploits merely crack open the shell of iOS to allow other code to operate. By themselves, they don’t allow execution of arbitrary code. However, zero-day exploits of all operating systems are in constant circulation among criminals, government security agencies, and murky-hat individuals who discover and sell them.
Apple has now responded to Mark Gurman of Bloomberg about this topic, agreeing that there are vulnerabilities, but that they don’t pose an immediate risk.