Apple Extends Privacy Protections to Traffic Leaving Its Walled Garden
Privacy ranked highly among the messages underlying Apple’s Worldwide Developer Conference keynote, meriting top-level billing from software chief Craig Federighi. Apple doubled down on previous efforts to ensure your personal, financial, and confidential information would remain private. The company also extended its offerings to block tracking in email, offer more anonymous Web browsing, and push back even harder against advertisers, marketers, and others trying to track your behavior without your knowledge or permission.
With iOS 15, iPadOS 15, and macOS 12 Monterey, Apple has further limited tracking data fed to third parties within Safari and added a blocking mechanism for invisible tracking images embedded in email messages. With iCloud+, the new name for the paid tiers of the iCloud service, you can also send email from anonymous addresses managed by Apple’s servers and use a proxy service for Safari that defeats tracking through a combination of encryption and redirection.
Conceptually, anonymity, privacy, and security have a complicated relationship:
- Anonymity refers to situations in which you can act without your identity becoming known to others. While it’s not synonymous with privacy, you can think of anonymity as one technique for realizing privacy. It may also prevent you from carrying out everyday tasks like making a purchase or participating in discussion forums or social networks.
- Privacy refers to the ability to control the level to which you’re willing to share information about yourself in any interaction, on a scale from entirely anonymous to fully and verifiably identified. That includes being free from surveillance as you browse the Web, open email messages, and communicate with others.
- Security refers to protection against potential harm caused by others, whether that’s accessing information about you without your permission or attacking your system via malware. It can be used as a catchall term for anything that lets you control your personal data, allowing for both the specific state of anonymity and the general notion of retaining privacy.
Apple has striven for several years to ratchet up its protection of personal data across all its platforms, particularly in Safari. While some advertising systems respect our requests, settings, and technological measures to prevent tracking and observation, other ad tech plays a ceaseless game of cat and mouse with Apple, bypassing the company’s protections and causing Apple to expand those protections repeatedly. Ad tech firms aggressively engage in this antisocial behavior to assemble and sell electronic dossiers of marketing information and for targeted advertising, which can be sold at higher prices than more general ads.
This constant pressure to subvert user intentions led to the death of the Do Not Track consensual setting. It also pushed Apple into making roughly annual changes to Safari that limit what information a third party (an ad network or other tracking company) can deduce or extract by having its code, cookies, or embedded media on a website displaying an ad or by trying to obtain visitor statistics. (Confusingly, and perhaps for historical reasons, the website is considered the first party and you the second party in that interaction.)
The specifics added in the operating system updates slated for the third quarter of 2021 tie up many loose ends. But they also blur the lines between anonymity and privacy. As TidBITS writer and security expert Rich Mogull of Securosis said, “Due to the insane intrusiveness of online tracking, the only way to maintain privacy is to use anonymity. It’s the advertisers and their supporting infrastructure that have forced this. They took away choice, so the only response is anonymity.”
Here’s the rundown of what you can expect to see later this year:
- Safari extends Intelligent Tracking Prevention: Apple first added this technology to Safari on the Mac in 2017 to prevent cross-site tracking, which allows cookies from one site to track you across unrelated other sites. Apple continually toils to block new workarounds that ad tech companies come up with. In Safari 15, Intelligent Tracking Protection will also prevent trackers from obtaining a user’s IP address for guessing a location or trying to track them across pages or sites.
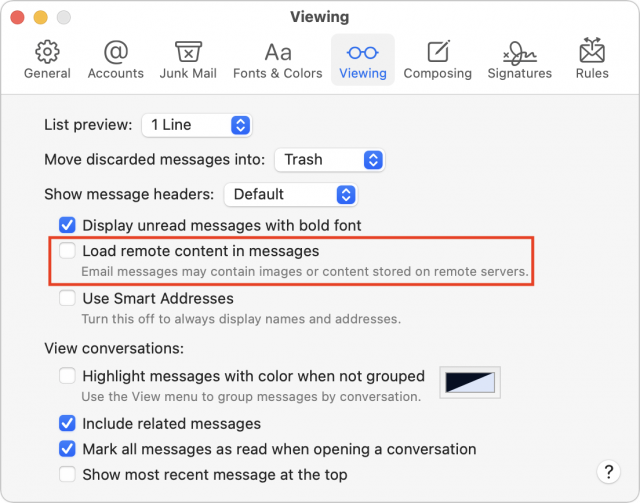
- Mail blocks one-pixel and similar trackers: A lot of commercial and some personal email embed invisible images, often just a 1-by-1 pixel graphic, that essentially “phones home” when loaded. A tracking service can infer various details about the email recipient, including that the message was read, when it was read, and where the user is located, among other details. Mail currently offers a switch that controls image loading in a message. When enabled, everything loads; when disabled, you have to click Load Remote Content selectively for messages that have graphic content you want to view—and thus load invisible tracking images! In the next update of Mail, you will be able to allow remote content to load while blocking invisible trackers. Mail will also mask IP addresses to prevent tracking and geolocation.
- Embedded location sharing: To reduce the availability of unwanted location tracking in apps, iOS 15 and iPadOS 15 gives developers a way to request that the user provide their current location through an affirmative action. Each time the app wants the location, it can make this query again. The current options only allow a developer to obtain continuous access during a session with an app (Allow Once), continuously while the app is in the foreground (Allow While Using the App), or both in the foreground and background (by going to Settings > Privacy > Location Services > AppName and selecting Always Allow). (Always Allow is useful for apps like those that track exercise, children’s whereabouts, or navigate by GPS.)
- iCloud Private Relay: New to iCloud+, this feature offers something like the Tor routing network, a combination of VPN (encrypted data transit over the Internet) combined with quasi-anonymity. When you turn on iCloud Private Relay, all your Safari browsing is encrypted and associated with an anonymous IP address. The request goes first to an Apple-controlled “ingress proxy” (which knows who you are but not what site you’re visiting) and then to a third-party “egress proxy” (which knows what site you’re visiting but not who you are) before being delivered to the ultimate destination. For non-logged-in sessions, this approach prevents effective user tracking or even knowing much about them at all. As with other secure services Apple offers, the company designed the system so it can’t decrypt your browsing session. Private Relay also protects two other leaky types of traffic outside Safari: DNS queries, which reveal the domains accessed by any Internet-connected software on your devices, and most insecure (non-HTTPS) Web queries from any app. For more details, see Dave Hamilton’s MacObserver article.
- Hide My Email: An extension of the Sign in with Apple offering for developers to use for account-based access, Hide My Email is also included with iCloud+. It lets you create a unique, random email address that forwards to your iCloud address, so you can send and receive email without sharing your actual email address. As with Sign in with Apple, you can disable or delete these addresses and never receive any email from that source again.
Apple didn’t decide to develop these additional privacy protections and anonymity enhancements in a void. They stem from a desire to protect users against unceasing attempts to monetize your every moment online by firms ranging from Facebook, one of the world’s largest corporations, to shadowy ad-tech shops.
By adding both free and paid features—iCloud+ starts at $0.99 per month for 50 GB of storage and other benefits—Apple ups the pressure on companies like Amazon, Google, and Microsoft to step up their privacy protections, too. Because Apple continues to focus on services as a pathway to maintaining its high margins and increasing its revenue outside of the vagaries of hardware sales, these privacy-first moves may also attract customers who make purchases on Apple platforms rather than others. It’s simultaneously user-friendly and good for Apple’s bottom line, and it forces other companies to try to meet Apple’s bar—or lie about their intentions with regard to your data.

Glenn,
I’ve been using MailTrackerBlocker for a couple of months now in Mail on 10.14 to get similar results, at least for tracking pixels.
The next-to-most recent update added a report so you can see how many trackers have been blocked and an icon in the message window to see if any where blocked in that message.
I don’t now if the forthcoming macOS 12 feature will have any reporting available, but I’m often amazed at what is shoehorned into email and would hope that I can continue monitoring what evil intentions are thwarted.
Cheers,
Jon
First, it would be nice to be able to see when tracking pixels are blocked. Maybe put an icon in the email where the tracking pixel would have been, had it downloaded.
Second, if you block tracking pixels, then they will just escalate to something larger. Of course, the images require unique URL’s in order to be useful for tracking, and a mail server can scan a broadcast email across multiple recipients to find the image that looks like a tracker, and then block it wholesale. Finding the tracking image in a single recipient email (non broadcast) might not always be so easy.
Most tracking pixels are 1 pixel by 1 pixel, so an icon would be hard to see anyway and might change the rendering of the HTML if it was larger than 1x1.
Apple I believe has altered the way that they retrieve all remote content from email now. The downloads now get done through a proxying IP address, so the senders get no information about what our IP address is. They will still form unique URLs per messages, so they will see that this particular message was opened, but they won’t be able to correlate the IP address of the recipient anymore. It’s true that senders will perhaps try other methods to track, but Apple moving to a like-VPN to download all remote content will help at least prevent getting information about your IP address, the mail client or browser that you use to download the remote content, etc.
There’s a big difference between tracking pixels and cookies. Tracking pixels send info directly to a tracker’s server. Cookies live on an individual’s browser. Both methods are based on still images. And Google has pretty much admitted defeat in the cookie war, especially because of pressure from the EU. But Google is moving forward with new, even more effective initiatives. And they are also refining data collection from live and prerecorded video, which are becoming increasing popular with users. Google, and other companies, are taking tracking to a whole new level:
https://support.google.com/google-ads/answer/2456138?hl=en
Object Detection and Tracking | ML Kit | Google Developers the eu
MMTalker, Cookies are based on still images? Please elaborate.
Doug. Ok, so no icon. But some kind of notification that tracking was blocked would be nice.
It’s not just pixels, but any kind of invisible or tracking image that Apple identifies. Apple said “pixels,” but I think that’s a shorthand (as it is in most anti-tracking software) for images designed not to be displayed but to provide a retrieval from a Web server that provides a tracking beacon.
What Doug said!
If you enable the feature. Without it enabled, retrieval happens from your machine as I understand their explanation. Apple’s explanation: “If you choose to turn it on, Mail Privacy Protection helps protect your privacy by preventing email senders, including Apple, from learning information about your Mail activity.”
Anything retrieved via a Web connection can have a cookie attached, but in a mail message, I don’t think cookies are sent by Apple’s Mail or third-party mail apps? On a Web page, however, an invisible image or JavaScript or what have you all allows a remote server from which the item is retrieved to obtain any information the browser sends on requesting the item, and the server can send a cookie in reply that will be accepted or ignored by the browser based on the rules the browser’s maker has set (Apple automatically blocks a lot of behavior now) and any settings in the browser you’ve changed that modify cookie acceptance.
A cookie is a single pixel that sends information to a server. There are cookies that permanently reside on a site, or those that hang around until they are removed. And there are tracking cookies that are often placed by third parties. A tracking cookie, aka tracking pixel, has code written in to it that will track paths of action across sites. Tracking cookies are used primarily by advertising analytics, e-commerce and content servers.
To clarify, a cookie may be attached to any item retrieved from a server, including a Web page, JavaScript, etc. It’s just part of an HTTP transaction. It’s unrelated to whether it’s an image (or a single pixel) or not. A cookie provided in a standard form as part of the header information sent back by a Web server in response to a retrieval of any item. The browser then uses rules to determine whether to store the cookie.
Likewise, when a browser connects with a Web server to retrieve a page, image, script, etc., it uses rules to determine whether there’s a stored cookie (really, a bit of text) that matches the domain, path to the file, and other parameters, and transmit that as part of the request.
Cookies are used to establish “state” or a continuous session on the Web, which is inherently a stateless medium when used without an HTTP-based login (common in the early days; rare now). A cookie is most often used to store a session token that lets you stay logged in for email, e-commerce, or when posting to TidBITS Talk!
Invisible pixels (often either 1-by-1 or displayed that size or merely set to be transparent) are often used in email, which doesn’t retrieve cookies as far as I can tell, so that the image is retrieved from a third-party ad-tech server that tracks email being opened and where (by IP address and anything else it might extract from the HTTP retrieval).
I think we’re confusing two different things.
A tracking image is an ordinary image sent in a mail message for the purpose of determining whether or not you read the message. An HTML mail message containing images may have the image(s) attached to the mail message, or the image(s) may be remote - fetched from a web server when you read the message.
Like all web content, the web server hosting a remote image may log every request to download it. That log typically includes the IP address where it was sent, the date/time and the URL that was requested.
The idea of using images for tracking is that you generate a unique URL for each person you send the mail to. This way, the operator of the web server can look at the log file and know which URLs were retrieved and by extension which mail messages were read and therefore which mailboxes belong to a person that read the mail message.
The technique can be used for any image, but since the company performing the tracking is often not the author of the mail message (e.g. it could be an advertising service or the company hosting the mailing list), it is typically done with an image that exists for the sole purpose of tracking. In order to not mess up the message’s content, it is typically something you won’t notice - like a 1x1 pixel image where that pixel is transparent.
This is completely different from tracking cookies. Cookies are a fundamental part of how the web operates.
Whenever you request any web content, whether it’s a page, an image, a script, or anything else, the reply contains many lines of header information in addition to the data you requested. The headers may contain one or more
Set-Cookie:header lines. These are key/value pairs and may contain any information the server wants to send you along with the requested data. Web browsers typically store this data in a local database, associated with the web page/site that sent you the cookie.Later on, when you request another piece of content from the same web site, your browser sends all of the cookies that came from that site along with the request using one or more
Cookie:headers.This is how, for example, web sites like TidBITS lets you log in once and remain logged in over time. When you log in, the server sends back a cookie representing your login (typically a cryptographic hash that can identify your login in a way that is difficult for someone else to forge). On all subsequent requests for content, your browser sends that cookie so the server knows that it is your account.
Advertisers use this mechanism for tracking you.
An advertiser (like Amazon, Facebook or Google) runs its own set of web servers that serve up ad content. Any web page that displays the ads includes content (typically a script) that downloads and displays an ad. The advertising server will generate a random ID representing you and will send it back attached to the ad content. Your web browser stores this cookie associated with the advertising server.
When your load another page that pulls content from the same advertising server (which could be from a completely different site), your browser sends the ad server’s cookie back. So the ad server knows that it is you that viewed both pages. And it knows what pages you were viewing because browsers typically include HTTP referer headers in requests, indicating where the request came from (or in the case of images, the URL of the page where the image will be displayed).
Note that this is an oversimplification. There is a lot more to how cookies operate and how they are used and abused, but this should at least help you to understand the basics. For more information, see Wikipedia.
Note that there are many other ways to track people on web pages and mail messages. This is just a quick summary of some of the most common ways.
A pixel is not a cookie. It is the act of retrieving a pixel for a web page that allows the browser to create or send back the contents of a stored cookie to the server sending the pixel (or any piece of web content on a page). Since page content can be made up of pieces from multiple servers, every one of them can store/retrieve identifying information identifying you on your machine.
Plus any server can retrieve information about your environment (screen sizes, color density, memory, available fonts, etc) that can usually identify your machine uniquely (your “fingerprint”).
And then cooperating sites share personal information about you with other sites, and soon everything is known about you, thanks to data aggregation and internal sharing.
Actually, third party cookies will become history sometime next year. Under pressure from the EU, other governments, and bad press, Google is planning to stop to cookie tracking and has been pushing Federated Learning Of Cohorts (FLOC) and Privacy Sandbox APIs as an alternative. Instead of tracking each and every individual as an entity, your data will be lumped into distinct special interest groups based on searching activity. Google is currently beta testing FLOC around the globe, but not in any EU countries or the US where they are under anti trust pressure. Summaries of what’s going on are here:
IMHO, FLOC and Privacy Sandbox sounds to me like it could be just as intrusive to individuals as cookies. But hopefully, smaller special interest publications like TidBits will benefit from cookies crumbling.
It’s a terrible technology and I hope to FLOCing heck it won’t be adopted. The EU probably won’t ultimately allow it, and the US under the Biden administration may prevent its adoption, too. Then there’s the browser side—Apple, Mozilla, Brave, and Microsoft won’t support it.
Yes!
I just stumbled across a couple of articles talking about significant issues with FLOC.
Ok, a cookie is not a single pixel. I was beginning to think that I had missed an entire section of web development. And it would seem that “tracking cookie” is a misnomer and “tracking pixel” is more appropriate. As I understand it, a tracking pixel just has a uniquely generated URL that allows the server to connect the download request to your IP address, browser, and OS. Any ‘code’ would reside on the server. Please correct me if I am wrong.
“tracking cookies” and “tracking pixels” are terms used to describe the use of cookies and images for the purpose of tracking users. But cookies and images have many other uses as well and the mail/web standards don’t distinguish between them.
The “tracking pixel” is simply an image reference in an HTML-formatted mail message with a unique URL designed to let the server associate requests for the image with the mail message in order to determine if and when the message is read.
In theory, it will let the server operator know when the mailbox owner reads the message, but like all things, it’s not perfect. The reader might have his mail app configured to not display images (false negative - the message was read but the server doesn’t know), and the reader might have forwarded the message to someone else (false positive if the message was read and the image downloaded by the forward-recipient).
And, of course, the operator of the server can get whatever metadata the reader’s mail app sends along with the HTML request. The operator will always get the IP address, URL and timestamp. Anything else will depend on the mail app used - some expose more data than others.
And yes, all the code used for this tracking resides on the server. Your mail app doesn’t do anything beyond loading the image from the server.
A cookie is saved on the browser that it was downloaded to; web servers can use them to identify individuals. A tracking pixel is sent directly to a server. They both collect information about what you see and do on websites. There are also retargeting pixels, which follow you around the web to gather information to serve you ads or content. And there are conversion pixels; after you make a purchase or complete a request, they will send follow up information to sign up for a service, offer bargains, or to make related purchases.
Cookies and pixels are usually used together by sophisticated marketers, as they kind of function sequentially with one another. But cookies often have expiration dates; pixels can’t do this.
The terminology here is very confusing and is being massively abused by the advertisers/spammers that use it.
For instance, I just did quite a bit of searching into what a “retargeting pixel” is. And it has absolutely nothing to do with the one-pixel images attached to mail messages. No pixel data (by any normal definition of the word) is uploaded to any server.
Instead, a JavaScript application is embedded in web pages by advertising networks. This script computes a URL that is used to request a single-pixel image when the page is loaded. The remote web server uses the requested URL to extract data collected by the JavaScript program.
The spamming community is calling this URL or the script that generates it a “pixel”, but that is simply an abuse of the English language. Pixels are dots of color that belong to images. They don’t exist independently of images and they are definitely not sent around the Internet like ID cards.
Unfortunately, the spammers creating this terminology either don’t understand the tech they’re using or they are deliberately inventing misleading terms in order to make it hard for technically savvy people to have an intelligent conversation on the subject.
If I decide to invent a user-tracking script and call its data a “Porsche”, few people would think I’m actually transmitting automobiles around the Internet, but that’s pretty much the same thing that’s going on here. Lots of deliberately confusing terminology designed to prevent people outside of the spamming industry from being able to intelligently discuss the subject.
“ A rose by any other name would smell as sweet.” William Shakespeare
Maybe we should move this to the”Champing with bated breath” thread?