New Apple Guide Offers Personal Safety Advice
Apple’s new Personal Safety User Guide, a website and downloadable PDF, provides detailed recommendations and advice for Apple users that span numerous Apple services, apps, hardware, and websites. As the author of multiple books about staying safe, private, and secure in iOS, iPadOS, and macOS, you can imagine I had feelings about it—and they’re largely positive!
It’s a great move for Apple to offer a single comprehensive, readable, and searchable place for settings and advice surrounding personal safety. (The version I examined was dated January 2022.)
Apple makes the purpose of the guide very clear—there’s no deflection of the potential for risk here:
Offering quick checklists and in-depth feature tasks, this resource is designed to help customers experiencing technology-enabled abuse, stalking, or harassment understand the options available across the Apple ecosystem that can help you protect your personal safety
The Personal Safety User Guide doesn’t entirely meet that target, but it does provide more readily available and centralized information on the topic than the company has previously released. Primarily, it offers help in finding all the places across operating systems and apps you might be sharing media, location, personal information, or other data.
A Summary of the Personal Safety User Guide
The first section of the Personal Safety User Guide helps you review how your devices and software are set up. The guide walks you through modifying sharing settings and removing people or stopping sharing, as well as determining if you’re sharing things about yourself you didn’t intend to.
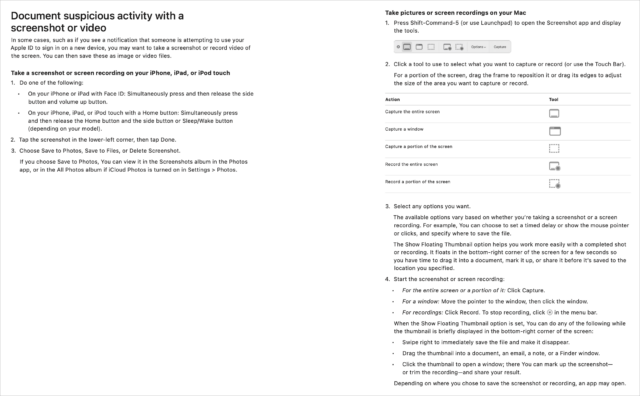
Several excellent pages provide in-depth advice on documenting suspicious behavior or settings. “Document suspicious activity with a screenshot or video” could be useful if you don’t know the ins and outs of capturing screenshots and videos on an iPhone, iPad, or Mac.
Apple even admits that someone might have installed third-party apps for malicious or unknown purposes:
If you’re concerned someone you once trusted installed an app on your device without permission, you can review a list of all apps installed on the device and review or change how each app accesses information.
The guide also highlights identifying and removing profiles, which enable one of the few ways people can be fooled into installing something on an iPhone or iPad that could easily monitor them. (Profiles can affect network traffic and other settings, and they make it possible for users to install developer-produced, non-App Store apps.)
You might also find useful “Manage Family Sharing settings,” a solid chunk of good advice on managing members, removing members, and getting yourself removed from a Family Sharing group.
Apple shirks the Personal Safety User Guide’s main duty by not digging more deeply into stalking and other unwanted tracking with “Stay safe with AirTag and other Find My accessories.” It’s a quick overview that doesn’t even address even all the features Apple offers, much less add additional insight. It also links to an Apple support note instead of providing that detail directly.
Likewise, the section “Avoid fraudulent requests to share info” is both somewhat off-topic and frustratingly brief at just two paragraphs and a one-line note. Apple could have provided much deeper and more useful information.
The second section, “Safety and privacy tools,” feels much more generic than the first. It offers instructions on updating your devices regularly, configuring your devices for secure access (with passwords, Face ID, and Touch ID), setting up your Apple ID safely and with two-factor authentication, and enabling iCloud Data Recovery Service. (That awkward name is what it’s called, but Apple doesn’t use it in this guide, referring to it only indirectly in the “account recovery contact” section.) This “Safety and privacy tools” section ends by walking readers through the new App Privacy Report feature that is more about apps invading your privacy than other people.
Apple ends the Personal Safety User Guide with three checklists:
- See who has access to your device or accounts
- Stop sharing with someone you previously shared with
- Control how someone else can see your location
The guide should instead start with these checklists, which could act as a verbose table of contents to everything in the document, much like the Quick Start section in a Take Control book. Instead, they’re relegated to the end, and only the first of them offers many links within the guide.
Room for Improvement
As a whole, the Personal Safety User Guide doesn’t hew as closely to its mission statement as I hoped it would. It offers useful advice on safety related to data access and physical tracking, but then it somewhat wanders into the weeds with much broader advice related to remote hacking attempts and other efforts associated with criminals and identity thieves. Apple could make this latter information more directly relevant to those concerned about personal safety issues.
Nonetheless, this version of the Personal Safety User Guide is a first edition, and there’s room for it to grow and mature into something that holds together better as a complete work. It doesn’t have to be literature, but having stated its thesis, it should follow through more completely.
Glenn’s current books covering safety, privacy, and security are Take Control of iOS & iPadOS Privacy and Security, Take Control of Find My and AirTags, Take Control of Securing Your Mac, and Take Control of Wi-Fi Networking and Security.
I seem to recall that for the Mac, the Guide merely directs the reader to look in the Applications folder, while applications can be in other places. (It’s possible that I’m thinking of some other Apple document or that I didn’t read carefully enough.)
You can pull up a list of applications using the System Information app (open-click the Apple menu, then select System Information…). Go to the Software/Applications category. You’ll get a list of every app (including internal ones like the Finder and Asian language input-method handlers). Click on one to get details about it, including its location in the file system:
Thanks. I just did that, and I somewhat understand why Apple would have omitted this method from the Guide (if, in fact, Apple did omit it; I might not have read carefully enough). There are many applications in my system, enough that it’s somewhat overwhelming. But I do appreciate you teaching me how to get the list.
Great article even it it has some room for improvement. (Sorry, I couldn’t resist quoting the article). Seriously well done, thank you