Apple Updates Numerous Operating Systems for Exploited Security Vulnerabilities
Alongside the features and bug fixes in its non-Mac operating systems (see “Apple Releases iOS 14.2, iPadOS 14.2, watchOS 7.1, HomePod Software 14.2, and tvOS 14.2,” 5 November 2020), Apple has released macOS Catalina 10.15.7 Supplemental Update (with a re-release of macOS Catalina 10.15.7 Update for those who haven’t yet installed it), iOS 12.4.9 (for the iPhone 5s, iPhone 6 and 6 Plus, iPad Air, iPad mini 2 and 3, and the sixth-generation iPod touch), watchOS 5.3.9 (for the Apple Watch Series 1 and later), and watchOS 6.2.9 (for the Apple Watch Series 1 and Series 2).
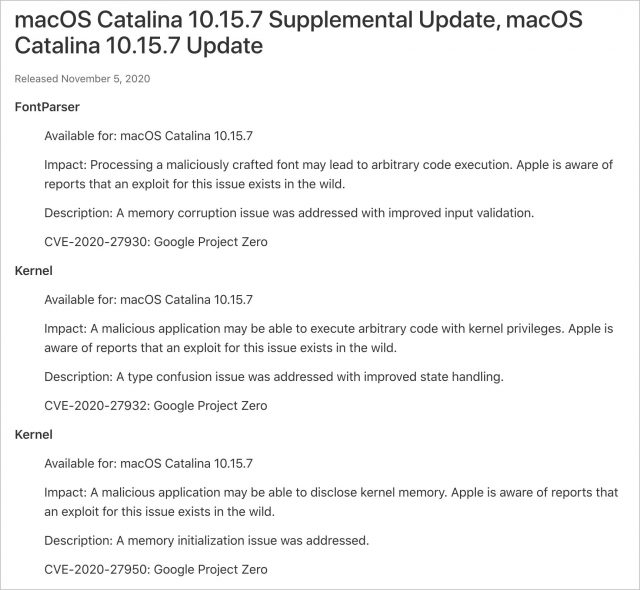
These updates all address the same three serious security vulnerabilities, which could lead to arbitrary code execution or kernel memory being disclosed. That’s bad, but the real problem is that Apple says it is aware of reports that exploits for these vulnerabilities exist in the wild. In other words, the bad guys are already using these bugs to attack Apple devices.
The updates for iOS 14.2, iPadOS 14.2, and watchOS 7.1 also close these vulnerabilities; tvOS 14.2 has security fixes but apparently isn’t vulnerable to these particular bugs. Needless to say, whatever operating system version you’re using, if there’s an update to address these vulnerabilities, we encourage you to install it sooner rather than later.
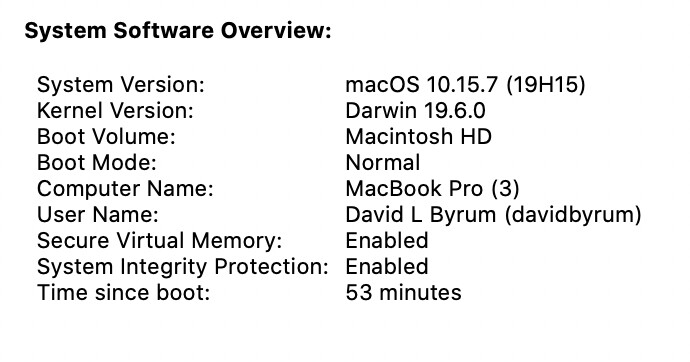
Once you install the macOS Catalina 10.15.7 Supplemental Update, macOS will have the build number 19H15, which you can verify by choosing About This Mac from the Apple menu and clicking the version number.
Note that iOS 13 and iPadOS 13 did not receive any updates for these vulnerabilities, presumably because Apple expects those users to upgrade to iOS 14.2 and iPadOS 14.2. Given the lack of updates for them, we also presume that 10.14 Mojave and older versions of macOS aren’t affected by these vulnerabilities.

I wonder if Mojave users will need or get an update?
Not sure of the need and details have not yet been submitted to Mitre’s Vulnerability Database, but there is no sign of an update and based on past experience, I would not expect one.
If there’s a need, that’s a shame, considering how many of us are still afraid to risk a move to Catalina.
Perhaps I just wasn’t clear. There is no information yet as to whether the vulnerabilities even exists in Mojave, hence may be no need to update.
I wouldn’t be surprised if the vulnerability was confined to Catalina, given the sloppy quality control at Apple in recent times. Maybe it involves a new emoji?
There are three vulnerabilities, one in FontParser and two in the kernel, and they affect all of Apple’s current operating systems, along with older versions of iOS and watchOS going back to iOS 12 and watchOS 5.
All indications are that these are deep vulnerabilities that evaded all of Apple’s internal checks and investigations by external security researchers. So I don’t think there’s any evidence of these particular problems being emblematic of the quality control issues that plagued the 2019 releases of iOS 13 and Catalina.
So we can expect a Mojave update soon. That makes it all the more irritating that I have a constant reminder to upgrade to Catalina (i.e. the badge on the Sys Prefs icon) that I am unable to disable (e.g. via the SoftwareUpdate Terminal command). I could easily miss a Mojave security update due to this pestering by Apple.
Just an FYI, after doing the Catalina Supplemental Update yesterday, my “About this Mac” does not have the number in parentheses that yours shows in the article, only the standard “Version 10.15.7”. MacBook Pro 16", 2019.
I am confused. According to the writeup, the update for iPhone 6S is 12.4.9.
However, my 6S currently shows Software Version 13.5.1 and Software Update wants me to go to 14.2, but I see no mention of 12.4.9.
I’m not an expert in these matters and would truly appreciate some advice. Thanks!
On my MBP 13" 2020 with macOS 10.15.7 after updating with the 10.15.7 Supplemental Update the (19H15) information does not show up where your graphic shows it. For my computer, it shows up in the Systems Report after slecting About this Mac -> Sytsem Report -> Software.
If by current you are referring to other than Catalina, can you please source that? Certainly Apple did not acknowledge that in their announcement nor has Google Project Zero updated the two CVE’s they reserved for the kernel vulnerabilities.
You must click on “10.15.7” in About this Mac in order for the build number to show up.
12.4.9 is for the 6 and 6 Plus. (Which is what the article says.) The 6s is a different phone from the 6.
The 6s can run iOS 14.x so it will continue to receive those updates.
No, I don’t think there’s any reason to believe that. It makes no sense that Apple would have updated things like watchOS 5 but not Mojave if Mojave needed the update.
Nope, when I say “current” I mean macOS 10.15, iOS 14, iPadOS 14, and watchOS 7, all of which received fixes for those three vulnerabilities.
Mojave security update 2020-006 10.14.6 is now available (1.44Gb)
Thanks! I’m not seeing it here on Tonya’s iMac, which is still running Mojave, nor is it on Apple Support Downloads yet. But I do see the security update note, which shows exactly the same three bugs.
So I was wrong about Mojave not being susceptible—my apologies for unwarranted confidence. I wonder why Apple waited over a week to release this security update (assuming it’s actually available to anyone now).
Something unusual happened with the release of Big Sur, which was that Apple revealed a lot of additional security fixes in earlier updates. If you do a search on “November 12, 2020,” you find a bunch of additional notes in security update documents.
Check out all the entries labeled “Entry added November 12, 2020.”
I can’t see why Apple would have revealed this information only after Big Sur was out.
My iMac running Mojave is showing Security Update 2020-006 10.14.6, macOS Supplemental Update, and Safari 14.0.1. They only showed up yesterday so presumably they’ll be available on Tonya’s iMac shortly.
I haven’t installed any yet, Apple’s recent track record makes me loath to install anything they produce until they’ve been out for a while.
Strange, I was able to see and get it a little over 24 hours ago.
I can’t explain it either, except that possibly they had most of the staff focused on getting Big Sur out the door.
The release of Big Sur does explains why these additional revelations about many earlier Security Updates were only released today:
My wife’s 2010 MBP running HS (last version that her MBP will run) showed the security update today, along with one other update. As usual, the security update had to be installed twice until it registered as all up-to-date.
She did the upgrades last night and it turned out that she hadn’t installed Security Update 2020-005 yet, so 006 wasn’t appearing because of that.
I try to avoid making suggestions or comments about this sort of thing to her.