An Annotated Field Guide to Identifying Phish
Do you like phish? Not the band, not tasty seafood dishes, and not the pretty tropical variety. I refer instead to the intellectual challenge of identifying phishing emails that attempt to get you to reveal personal information, often including login credentials or financial details, or entice you to call a phone number where trained operators will attempt to separate you from your money.
Phishing is a big deal, with a State of Phishing report from security firm SlashNext claiming that there were more than 255 million phishing attacks in 2022, a 61% increase from the year before. The Verizon Data Breach Investigations Report for 2022 says that only 2.9% of employees click through from phishing emails, but with billions of email addresses available to target, the raw numbers are still high.
Even before the LastPass breach (see “LastPass Shares Details of Security Breach,” 24 December 2022) and the news about a data leak containing email addresses of over 200 million Twitter users, I had been noticing more phishing attempts evading Gmail’s generally effective spam filters. I don’t entirely blame Gmail for this—in many cases, I can see how the messages would be hard to catch.
In the past, many phishing attempts were obviously fake, and intentionally so. That’s because they only had to sucker people who were sufficiently inexperienced, credulous, or easily deceived that they would continue to go along with the scam. Now, however, I’m seeing phishing attempts that are more sophisticated and harder to identify quickly.
I’ve been examining phishing attempts for so long that it’s hard for me to imagine what might fool someone else, so I wanted to share some recent attempts that slipped past Gmail’s filters. For each message, I’ve called out some of the ways I identified it as phishing. I suspect that most of you will assume that you would also easily have identified the message as fake, but remember, many people move rapidly through their email without reading carefully. Perhaps my calling out of some of the hallmarks of phishing attempts can help you or the people to whom you forward this article avoid being drawn in.
Password Reset
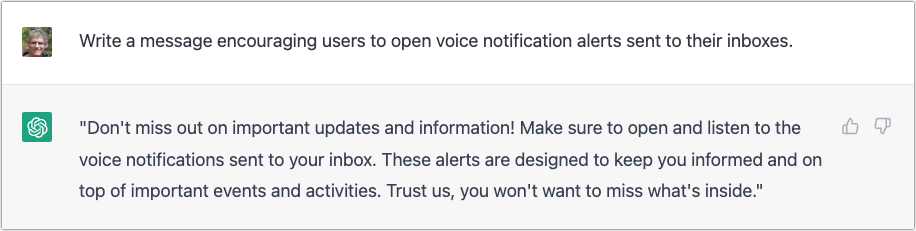
This phishing attempt purports to come from a system administrator in charge of my email domain and tries to lure me into clicking a button. The text isn’t very good, but the buttons are, and it’s easy to imagine someone who’s scanning too quickly clicking the button without even reading the text. But that would be a mistake!
- The Subject line for this message is glaring to me because I know how tidbits.com is managed—I do it! So this one wasn’t going to fool me, but I could imagine someone getting a similar message that identified their domain and thinking it was from the IT department. Putting the email address in the Subject might get some people to click because it feels personalized.
- It feels weird to me that the From line of the message is also tidbits.com. Even if an administrator had to email users about a required password reset, I would expect a name or a role to appear here.
- The body of the message is a giveaway. The phisher clearly doesn’t know my name and is thus addressing it to my username. With additional data being leaked all the time, however, there’s no guarantee that phishers won’t start personalizing messages more thoroughly. The other problem with this text is that it doesn’t sound like it was written by a native speaker of English. There’s a difference between someone who’s just a weak writer and someone who doesn’t think in English, and the phrase “please kindly reconfirm Password” screams “non-native speaker.” (I presume that phishing attempts are localized into other languages for people in other countries, so replace “English” with whatever your native language is.)
- These buttons are pretty good—they look official, they’re consistently capitalized, and one is clearly the default. But anything that contains the word “password” and tries to get you to click should set off warning bells.
- The phisher should have stopped with the buttons. I adore this small text, which tries to claim that what you’re looking at is a system notification, not an email message, and you can’t reply to it. Yeah, sure, buddy.
- Finally, we come to an even smaller line of text that sounds like an AI wrote it, in that it makes a nominally true but largely meaningless statement. I guess I could imagine a beleaguered system administrator writing something similarly banal, but to me, it grates.
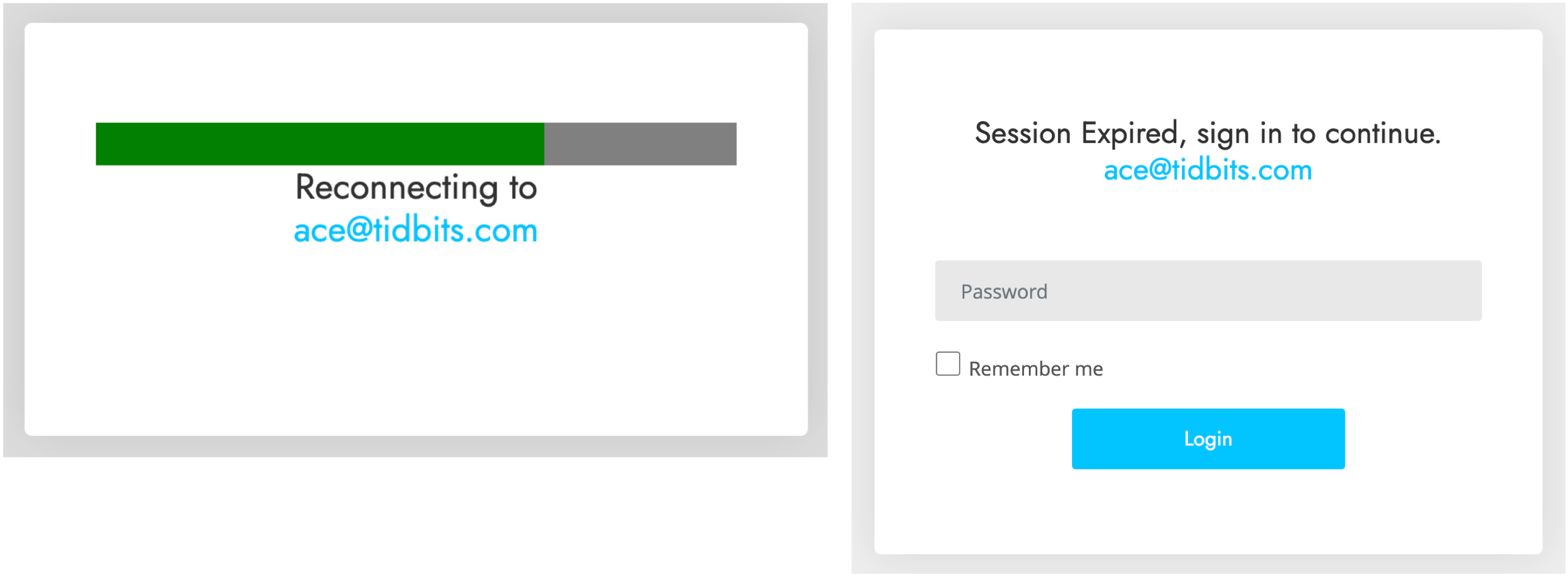
Interestingly, when I clicked either of those buttons (the risks I take for you, loyal readers!), I was directed to a Web page that showed the progress dialog on the left and then tried to get me to log in with the dialog on the right. I didn’t take it any further. It’s worth emphasizing that you shouldn’t click buttons or links in a phishing email since that might put your email address on a list of “dupes who click stuff” and invite even more phishing messages.
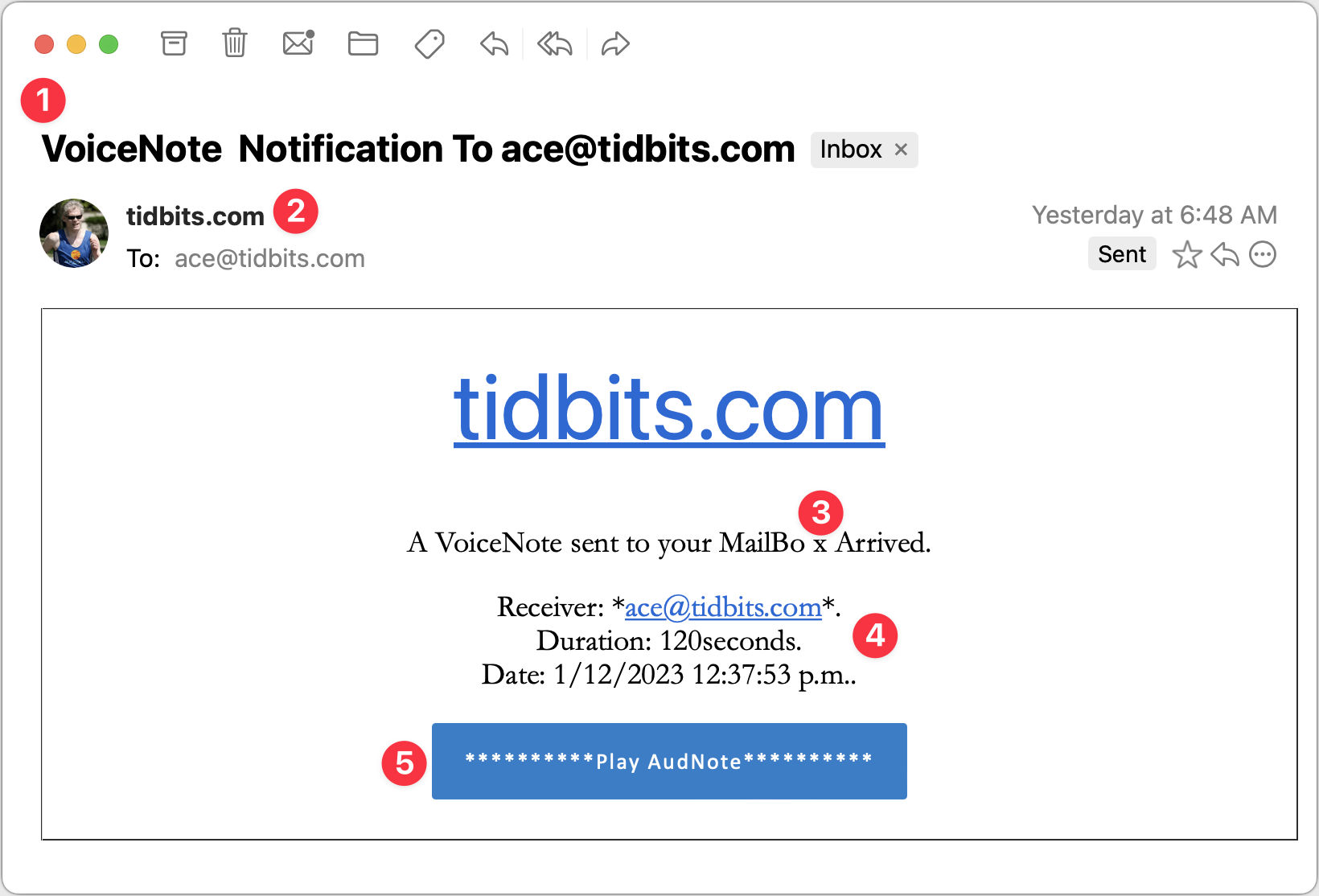
VoiceNote Notification
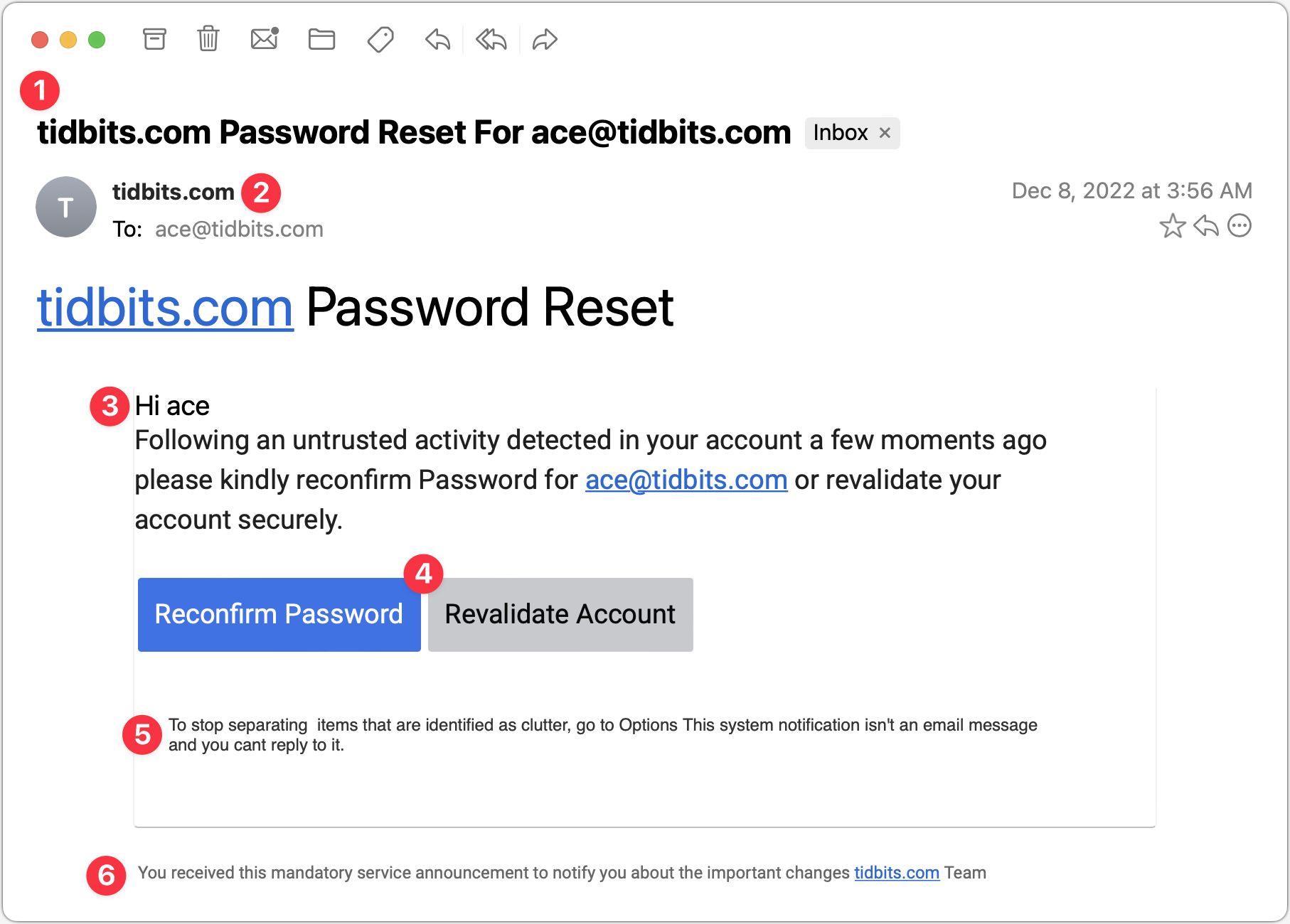
My next example pretends to be a notification of a voice note. Again, since I’m the person who would have set up any voice note system, this phishing attempt is wasted on me, but in a large organization where people don’t know what IT is up to? Not inconceivable.
- I could see someone opening this message because the Subject isn’t problematic. I tend to think that if your email address ends up in the Subject line, it’s probably spam, but I don’t know if everyone thinks that way. The copyeditor in me also takes note of the two spaces between “VoiceNote” and “Notification” and the fact that “To” is capitalized. It’s unprofessional and looks wrong, but real emails could have similar mistakes.
- I wonder if this is the same phisher as in the previous attempt since it’s again clumsily attempting to fool me into thinking the message is from a system administrator at my domain. In fact, what’s happened here is that the phisher has forged my address, which my email client, Mimestream, indicates by showing my avatar and putting a Sent tag over on the right. This message appears to be from me and to me, but many people wouldn’t pick up on those subtle cues.
- I’m not perturbed by the camel case in “VoiceNote,” which matches the Subject and could identify some product or service. But the capitalization and extra space in “MailBo x Arrived” is glaringly bad. Had it said, “You have received a VoiceNote.” more people might have believed it. I can’t believe I’m making editing suggestions for spam, but with services like ChatGPT, phishers won’t have trouble writing better text. They will have to be a little sneaky—ChatGPT tries to avoid helping miscreants.
- What’s with the asterisks, the periods, and the lack of a space in “120seconds”? I’d expect cleaner text in a notification purporting to be associated with some VoiceNote service. The timestamp is also suspiciously precise—I can’t see any real product designer allowing such detail.
- I’m so disappointed with this button! This phisher is far too enamored of asterisks, and they couldn’t even stay consistent with the product name, switching suddenly to AudNote.
And in fact, when I click the lame button…drumroll, please…it is the same phisher as the previous one! Same progress dialog, followed by the same login dialog. The first one arrived over a month ago, so it’s interesting that the phisher is continuing to probe me. I wonder if clicking the links will cause more to come.
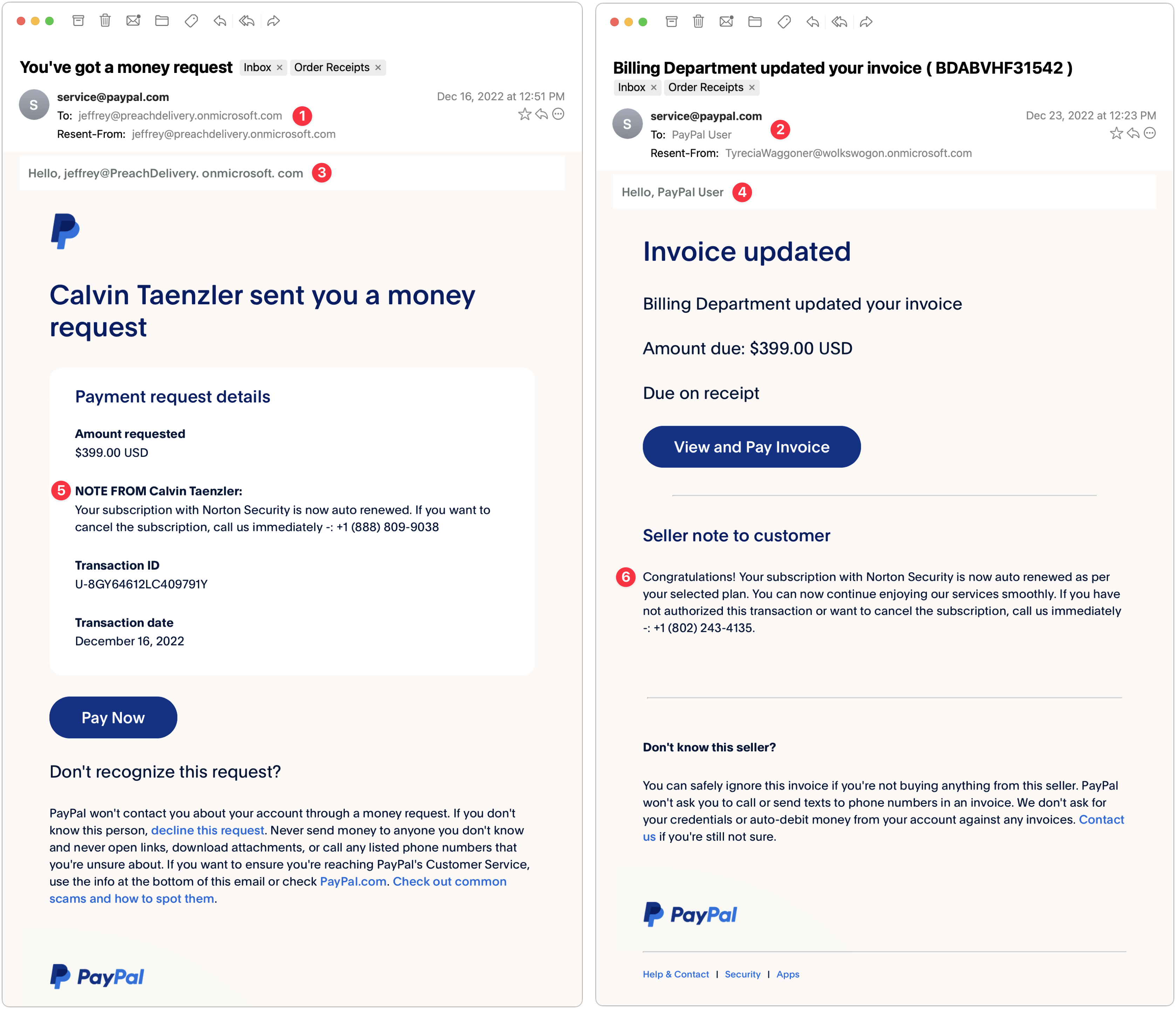
PayPal Money Request and Invoice
My next two examples are devilishly good because they use real PayPal messages, complete with multiple bits of text warning about phishing. But there are still giveaways. These arrived a week apart and are almost certainly the work of the same phisher.
- The To line in the left-hand message identifies some random person. This is a glaring but odd mistake since phishers can generally get your address in the To line. The Resent-From line is also a clue because Mimestream is calling out the fact that the message was sent to and from the same person.
- In the right-hand message, the To line merely calls out “PayPal User” and uses a different Resent-From line. That’s less of a giveaway, but you should always be suspicious of messages that don’t seem to know who you are or that are sent by people you don’t know. (And if you know Tyrecia Waggoner, you have a tougher job.)
- Another poor job of personalization on the left-hand message. Although the formatting of this line looks wrong to me, when I compared it against a legitimate PayPal money request, it’s the same, albeit with my name. If the phisher had used my name rather than the email address of the person who showed up in the To and Resent-From lines, it would have been more convincing.
- I believe these two messages are from the same phisher, who is learning how to modify the PayPal messages better, since this one is addressed to “PayPal User.” That’s not too persuasive, but it’s easy to imagine it becoming more so.
- Who is Calvin Taenzler? Unless you know, you probably won’t fall for this request, even after reading the fake message about your Norton Security subscription auto-renewing. I tried the phone number, but it wouldn’t connect—perhaps it was live back in December when I received this phishing attempt.
- The evolution of the PayPal scam continues. Instead of naming someone you won’t know, the message pretends to be an updated invoice for that fake Norton Security subscription, and if you don’t want it to auto-renew, you have to call a phone number. It’s easy to imagine someone with failing memory thinking they might have subscribed to Norton Security and calling to check. Like the other number, it wasn’t active anymore.
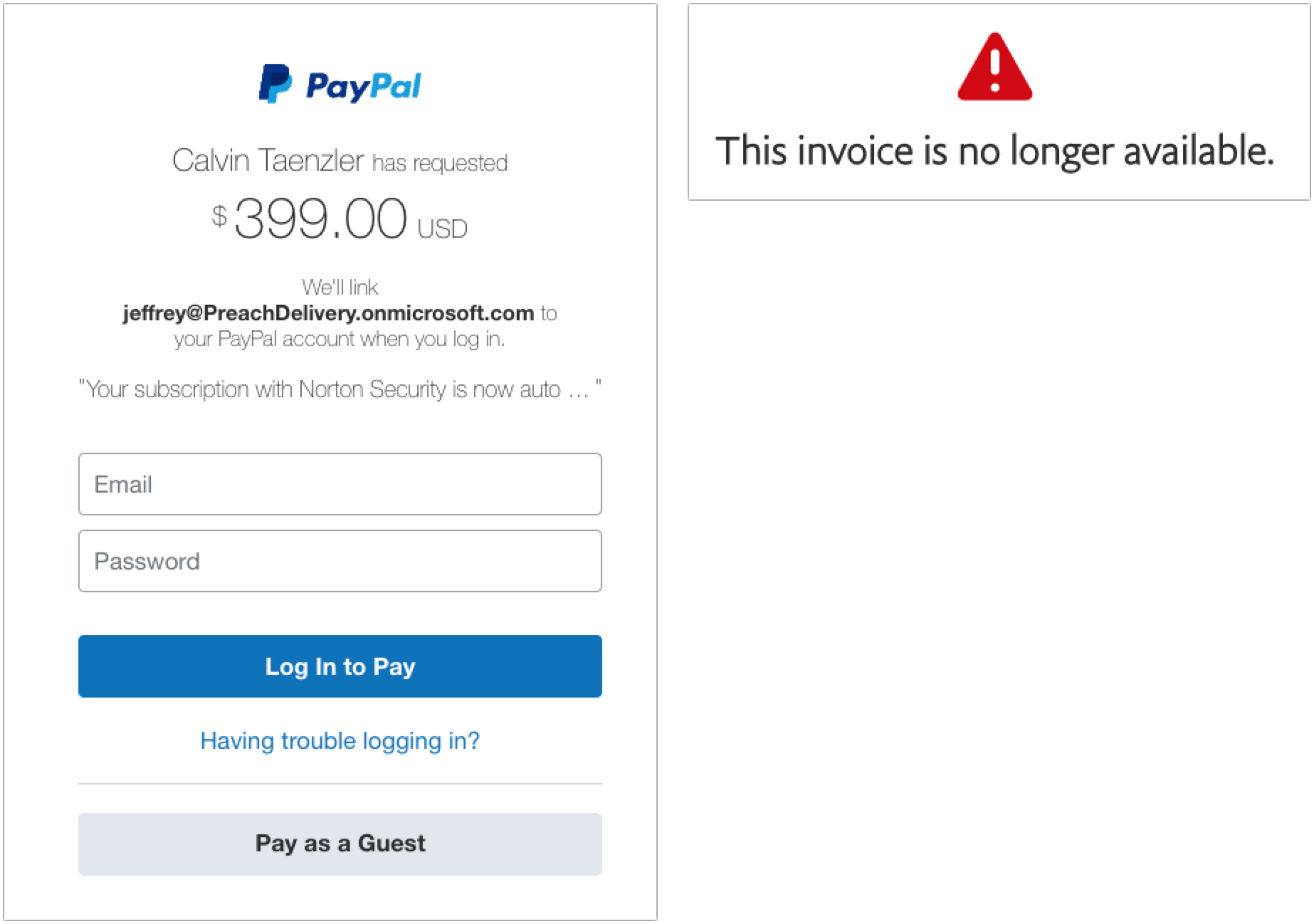
When I clicked the Pay Now button on the left-hand message, I was sent to a legitimate PayPal login screen. Needless to say, I didn’t go any farther, but unless PayPal has shut this account down, it seems like it could be collecting money. Clicking the View and Pay Invoice button on the right-hand message also went to a legitimate PayPal page, but it displayed an error about the invoice being no longer available.
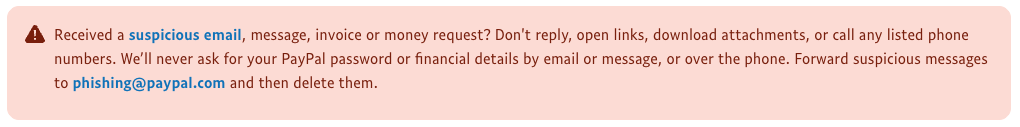
If you receive PayPal phishing attempts, PayPal asks that you report them. Forward the messages to [email protected] and then delete them. Do not mark them as spam, or you might find legitimate PayPal messages being caught by your spam filter.
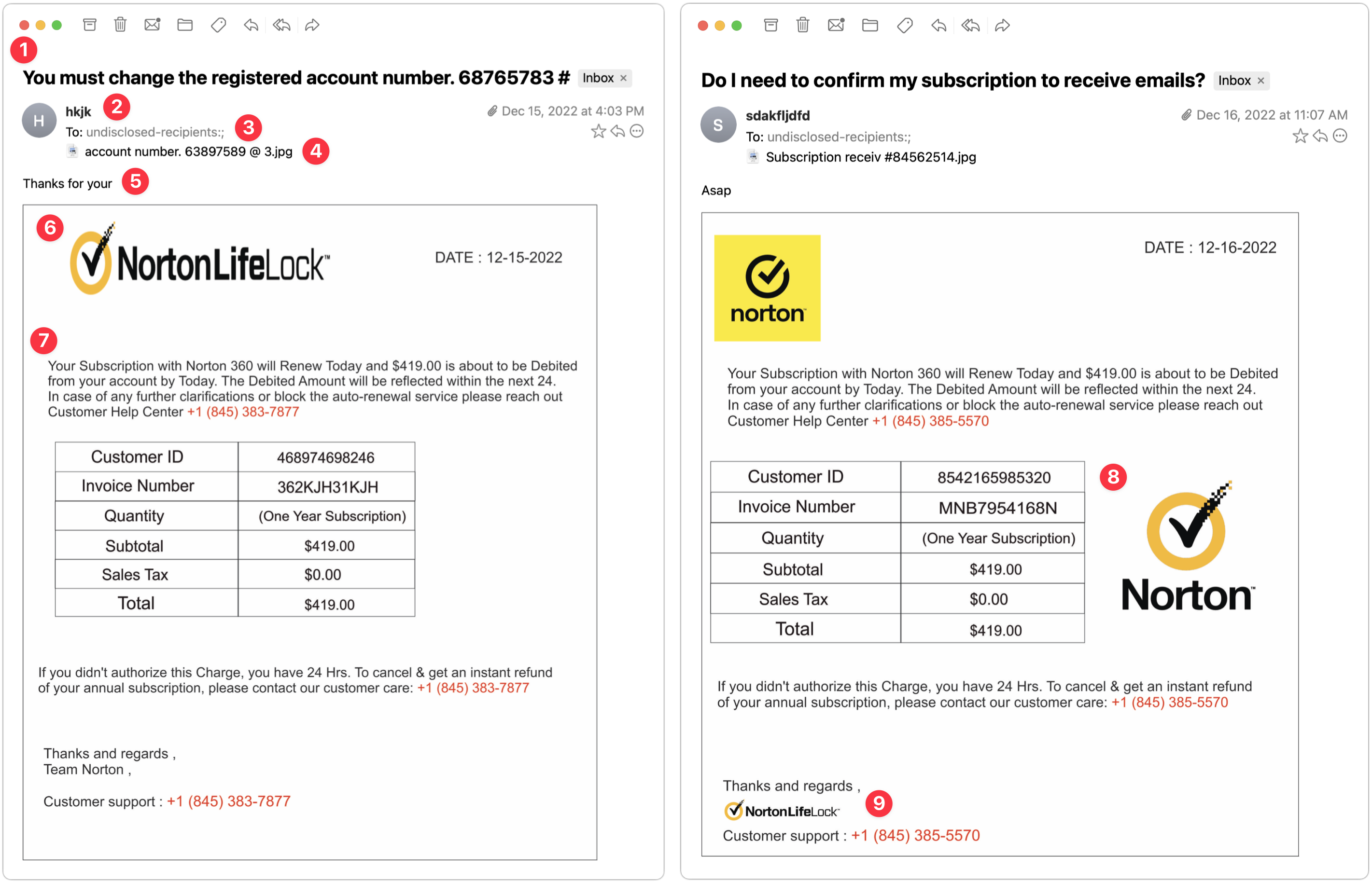
Norton 360 Invoice
The next two examples came a day apart and are very similar. Again, they seem to show a particular spammer—perhaps even the same one trying the Norton Security scam above—testing different techniques.
- The Subject lines of these messages are both fairly effective—in both cases, I’d open them to see what they’re talking about. Notably, neither has any egregious spelling, capitalization, or grammatical errors.
- This phisher was lazy and just put some random letters in the From line. That’s a dead giveaway, and had I been working normally, I would have marked these messages as spam instantly.
- Notice that the To line says “undisclosed-recipients.” On its own, that doesn’t bother me much because it’s not uncommon to receive Bcc’d messages that end up with something like this in the visible To line. However, these messages purport to be individual billing reminders, complete with customer ID numbers, and it doesn’t make sense that a business that knows my ID number wouldn’t also know my name.
- Pay attention to the attachments here—both are JPEG images with names that don’t set off any major warning bells. The invoices appear in the message windows because Mimestream displays attached images that way.
- Without Mimestream showing the attachments in the body of the message, all you’d see is this one line of text: “Thanks for your” on the left and “Asap” on the right. That’s how these phishing attacks evade Gmail’s filters—there’s too little to go on to mark the messages as spam automatically. We’ve all sent brief messages that are a line of text and an attached image.
- On the left side, the NortonLifeLock logo is horizontally compressed. That’s a tell for me—no large company with basic competence would allow email to go out with the corporate logo squished. It’s different—and better—on the right.
- The text is the same on both sides, apart from the phone number, and it’s pretty bad. What is it about the intersection of English and whatever language so many phishers speak that they capitalize words with such abandon? If it looks like a message was suffering from a spasming Shift key, it’s almost certainly not legitimate.
- The table is a clever touch that makes the message seem more legitimate. I particularly like the row indicating that no sales tax was charged. Pay closer attention when a message starts to look real—a quick glance at a table like this could get you to click something if you weren’t reading carefully. Also, note that a day after the first message on the left, the phisher figured out how to avoid squishing the Norton logo and found a nicer place for it.
- Lastly, you can see on the right side that the phisher has used the NortonLifeLock logo again, but as a signature of sorts, and with the proper aspect ratio. That looks much more real than the Team Norton text signature on the left. In short, beware of graphics. They’re easily copied and are an easy way to make a message look more real.
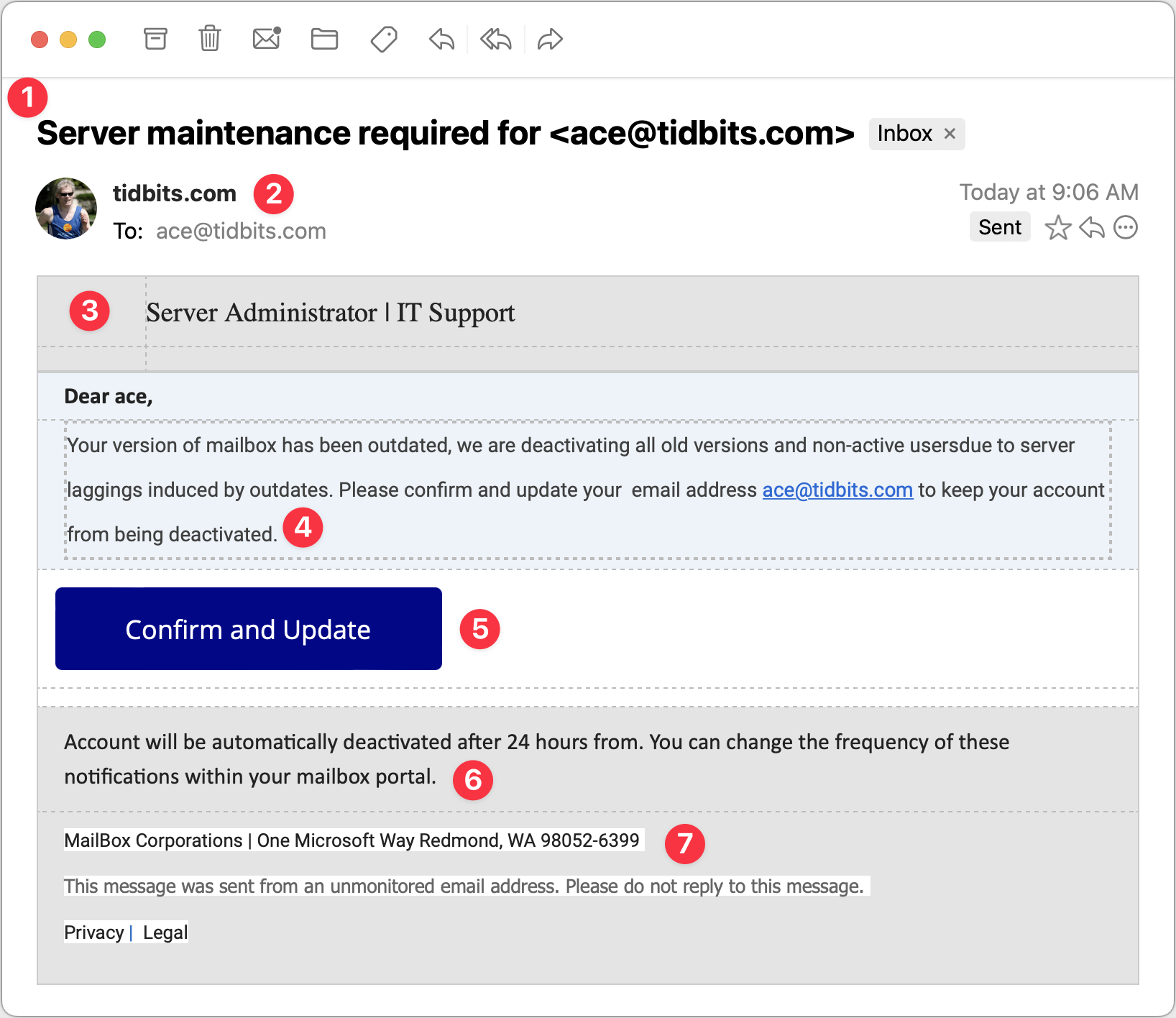
Server Maintenance
For my final example, consider this message purporting to come from my company’s IT Support department. It’s trying to steal your email password because once an attacker controls your email, they can reset your password at other sites and compromise more sensitive accounts. Protect that email password above all else!
- The Subject line in this message is once again pretty good. I’d open this message because even though I run all the TidBITS servers, they’re all hosted at companies like Arcustech and DigitalOcean. I already receive notifications from those companies about planned outages and the like, so this Subject line doesn’t set off many warning bells, apart from including my email address.
- Since the message purports to be from my IT department, having the From line be the domain isn’t seriously problematic, and the To line below is also correct. However, note the use of my avatar and the Sent tag off to the right. That’s Mimestream indicating that the phisher forged the message to look like it came from me as well as being sent to me. Not all email programs provide such an indication.
- The table formatting in this message—particularly the dashed lines—is rather odd. To me, the dashed lines scream “Fake!” although I don’t know if others would pick up on that. Pay attention to gut feelings that something isn’t right.
- Once again, the text is poor, with numerous mistakes that indicate that the message was composed by someone who doesn’t speak English natively or even bother to let auto-correct work. The claim that the IT department is deactivating accounts is designed to make you worry, but good IT departments wouldn’t just send email to see if an account was in use before deactivating it.
- This Confirm and Update button looks good and is an attractive target for someone scanning without reading carefully. Beware if you find yourself doing that!
- This second bit of text is nonsensical—I would hope that anyone reading it would get that, but perhaps that’s overly optimistic.
- I’m amused that the phisher invented “MailBox Corporations” and located it at One Microsoft Way. It’s a stylistic flourish but counterproductive if the message is supposed to emanate from my company’s IT support department. Mismatches like this are another good hint that a message isn’t real.
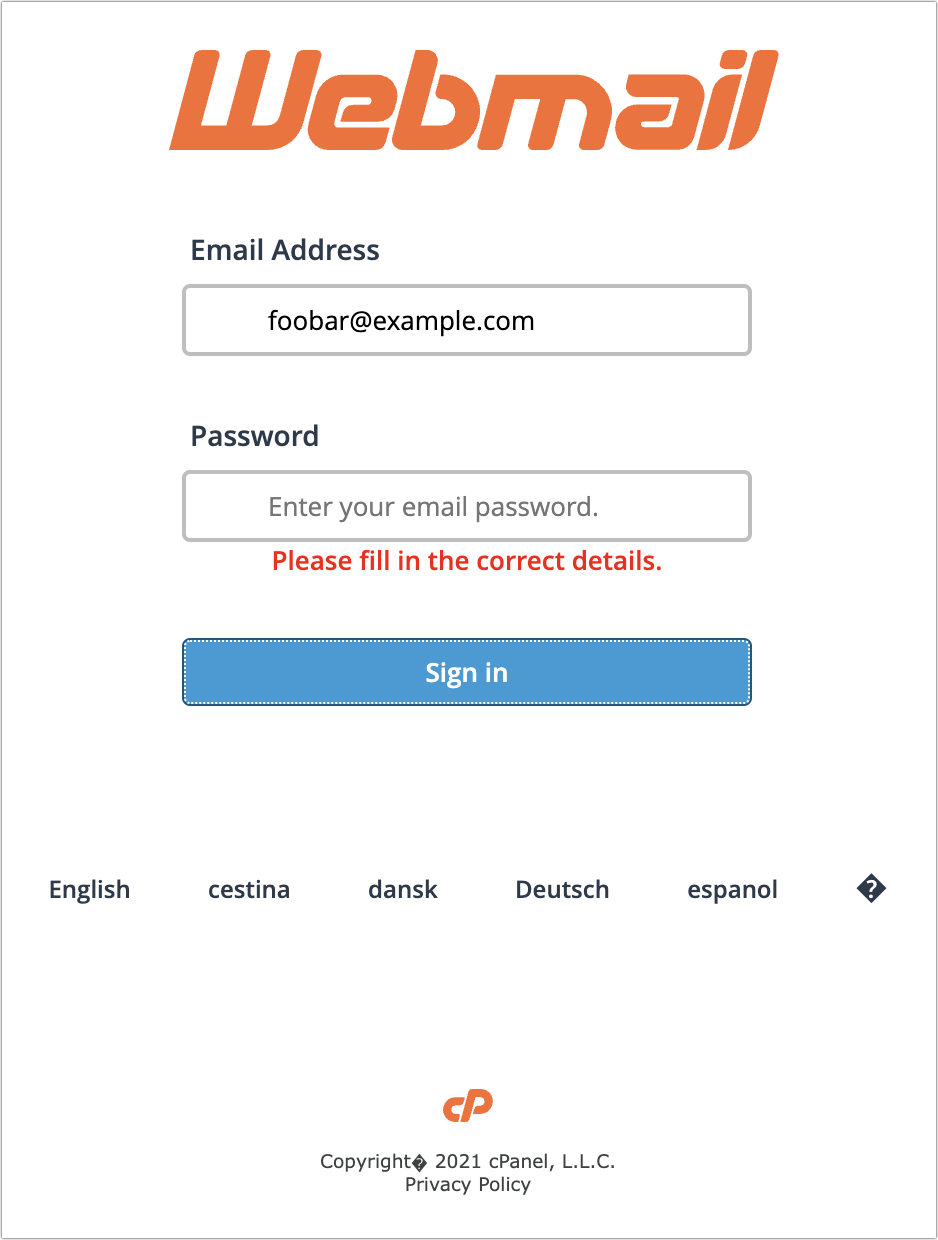
Clicking the Confirm and Update button loaded a generic cPanel login for a webmail service. It has a little trouble with its copyright symbol, and I hope it wouldn’t fool anyone who was expecting to see their organization’s webmail system. I fed it a random email address and password and got an expected error, but I presume that all the data is being captured on the other side.
Overall Advice
I hope you’ve found this tour of a few selected phishing attempts helpful. As you can see, they vary widely in their sophistication and techniques, but with careful attention, you shouldn’t have much trouble resisting their siren calls. My main pieces of advice for identifying phishing attempts are:
- Assume that you shouldn’t click anything in an email message until you’ve given it a closer look. It’s easy to skim and respond to a full inbox, which is exactly what phishers are counting on.
- Read the text of the messages, looking for capitalization, spelling, and grammatical mistakes. Nothing prevents phishers from writing correct English, but it seldom happens. Pay special attention to the fine print at the bottom—it’s often more of a giveaway than anything else because phishers are trying to make the message look right without continuing the deception.
- Evaluate any claim about something happening within your organization against what you know to be true. Would your IT department do something extreme like deactivating accounts with little warning? Even if that’s not inconceivable, it’s safer to ask someone in the organization if a message is real than to click buttons randomly.
- Be careful when you see big, legitimate-looking buttons. They’re easy to make and can sucker people who don’t read the surrounding text carefully.
- If a message is just an attached image, it’s almost certainly fake.
- With messages that don’t set off any other warning bells, like the PayPal phishing attempts above, be alert for names and email addresses that aren’t familiar.
Good luck, and stay safe out there!
Coincidental article timing for me.
As it happens, the last couple of months my outlook.com email account is getting endless phishing emails daily (10-20 throughout the day) from similar sounding sources (eg’s. one is “m ic ro soft” type things, another is various suppliers of air fryers I apparently keep “winning” and need to claim ASAP, or shipping to pay for [the obvious ones around at the moment]!). They’ve been driving me nuts.
Regardless of whether they arrive into my Inbox or into Junk, I keep going to the Outlook email website, and marking them as ‘Phishing’ in there for the last couple of weeks in an attempt to get Microsoft to notice them and perhaps do something, but they don’t seem to be curtailing them at all.
Aaaraaagh?!?
In November and December I got loads of obvious phish, mostly thru my ATT/Yahoo account. When my wrist got tired of swipe-Delete I decided to create filters. These have been great for repetitive patterns (many emails offer the same product or service) but there have been 2-3 dozen different types of phish to “fry.” Most of this problematic “school” have swum off somewhere else but I realize that security requires this “Old Man and the Sea” to maintain constant vigilance. Thanks for your basket of fresh tips, Ace!
I wonder if Chat AI will help construct more readable text in future phishing attacks
Since I access email through a Web interface (mail.yahoo.com), as many other folks do, it is instantly obvious that any claim that my email software is (or is about to become) outdated must be coming from a phisher. AT&T manages and maintains the Web interface without any intervention on my part.
This may be somewhat tangential, but I’ve recently been getting phishing attempts via Apple Messages, purporting to be from UPS or USPS, and telling me that they attempted delivery and were unable to deliver and I should click a link to reschedule or arrange pickup.
Like Adam’s examples, these are pretty easy to spot due to poor use of English and the fact that they said they attempted delivery at 3am. Never mind that I hadn’t ordered anything or was expecting any deliveries. Trashed the text and blocked that sender.
I don’t know how the scam is supposed to work, but presumably they looking for personal data to use in other scams. Beware.
Names and email address munged- I am ABCD
On — 2022, at 6:53 AM, [email protected]> wrote:
Hi, Let me know you got my email.
On – 2022 at 7:00 AM [email protected]> wrote:
Yep - got it a few minutes ago-
ABCD
On 2022 at 7:03 AM
[email protected] wrote
Re favor request
I’m so glad I got your email
actually I’m trying to get a google play
gift card as a birthday gift for my (family member) . It’s his birthday but i can’t do this now because I’m currently
OUT OF TOWN and the stores around here are out of stock and i tried purchasing online but unfortunately no luck with that.
Can you get it from any outlet around you?
I’ll pay back as soon as I am back? Kindly let me know if you can handle this?
Await your urgent email.
Thanks JKLM
++++
NO I did not fall for it, and later got ahold of JKLM since it was NOT something they would do .
But note just how fast I got the response-phishing email
The rest off the story follows; ( cliff note version-) after several hours of background work, checking ip etc plus comm witha a few others.
1)JKLM and myself are casual friends in a retirement community rarely comm via email
2) Others had gotten similar from JKLM
JKLM was unaware
Turned out one of the others who had gotten similar had previously had their Outlook contacts hacked/phished and had been in normal email contact with ABCD and some of the others who had gotten similar to myself.
Retirement communities are superior phishing grounds
As far as I ( we) have found out so far, no one fell for the scam.
Suggest that those who have relatives in similar communities take the time to notify, explain, and suggest they use two or three emails, some for only significant stuff and one for casual conversations
One thing I’ve also seen is phishing through Facebook. This provides an advertisement for a company with a special sale. The link takes you to a website that is definitely not associated with the real company, and has excellent prices, like 80% off. I assume that if you buy something that it wont actually buy anything but record credit account details or PayPal, which will then be used to perform fraudulent transactions.
While I was writing that, got a text informing me that my mobile phone number had changed at a bank, that I don’t have a relationship with, and asking me to ring a number.
With regard to the ‘Paypal’ phishing email, last November I received the following text in an email that appeared to come from PayPal:
Hi Peter [& my real surname],
DEVONIA ROSS sent you a money request
NOTE FROM DEVONIA ROSS:
ALERT: SUSPICIOUS ACTIVITY ON YOUR ACCOUNT AMOUNT £989. 99 GBP DEBITED FROM YOUR ACCOUNT, IF YOU DIDN’T AUTHORISE THE TRANSACTION CALL US AND STOP THE PAYMENT IMMEDIATELY @+44-800-260-5986
This was followed by a very long Pay Now link! I was sure this was a phishing attempt, although examination of the real headers didn’t show any telltale signs such as .ru domains! However, rather than just trashing it or reporting it to SpamCop I separately logged in to my Paypal account, only to discover that the payment request had indeed been made, but when I clicked on the Cancel button after my independent login it merely threw up an Error code, causing mild panic, so I rang the number given, +44 800 260 5986. The man who answered, in what sounded like a busy Indian call centre, instead of promptly cancelling the fraudulent payment request asked me ever more ‘security’ questions requiring full details of both my bank cards linked to my Paypal account, expiry dates and even the CVV numbers from the back, and still this wasn’t enough, he wanted my place of birth and my mother’s maiden name. After 32 minutes I was so suspicious of these questions and lack of action in cancelling the payment request I disconnected, rang my bank and cancelled both payment cards. At one point in the call to Paypal we were disconnected and I was rung back. Could the return call have been from a scammer? It sounded as if from the same Indian call centre.
Three hours after the large payment request was made a mysterious credit of $1.26 was made into my account, from someone else I had never heard of. This had the effect of blocking my attempt to close my Paypal account until I reversed this transaction. I was able eventually to cancel the payment request online and close my Paypal account. Has anyone else been asked such a large number of ‘security’ questions by Paypal? I then changed my email password as a precaution as I could not understand how such a payment request could have been possible to make and I think it incredible that Paypal should simultaneously flag up a suspicious payment request while incorporating into the warning email a Pay Now link for that payment!
Thank you to Adam for such a thoroughly researched and useful article about phishing emails.
I have yet to see a single corporate email that would actually require clicking on a link in the email. Actual corporate email that requires action for me always means I can trigger that action by going to that company’s website, logging in on their user portal, and then triggering the action from there. That way it’s me who initiates the communication and I know who I’ve gotten in contact with.
I’m tempted to claim there are no legit corporate emails that would require you click on anything within that email.
I do get legit emails with embedded links. But they’re usually from colleagues at work (or perhaps friends/relatives) linking to a document on our Google share or some other internal document managing system. Those emails are from known colleagues, usually come expected or at least with accompanying personalized body text that make them credible, and look entirely different from any corporate or phishing type email.
Good article, @ace. Appreciate the examples and advice.
Another clue to phishing can often be seen by looking at the link addresses of the sender, reply to, and embedded links, as can easily be done in Apple Mail.
Another example is receiving emails from people you know with their suggestion to click on an embedded link. Even though the ‘friend’s’ name appears in the From field, inspecting the From link is usually a giveaway. Another clue, often used, is a list of other people in the cc: field, some of whom you may recognize as friends of the alleged sender. I figure this is an indication the real sender’s email has been hacked and the spammer is sending the email to everyone in the sender’s address book… time for the real user to change their email password…
This is certainly true, however, everybody should keep in mind that the From: in any email can easily be spoofed. And by easily, I mean pretty much anybody equipped with the right email client and SMTP server. It does not require any fancy “hacking” whatsoever. In fact many people do this routinely because they choose to send email from one account but supply their From: as coming from the other.
So always be suspicious of what is says under From:.
If you inspect the header and follow the SMTP path of an incoming email, using simple tools such as nslookup or host, you’ll easily recognize when Uncle Will’s email that claims to be coming from his Google account actually originated from freepornXXX169 registered in Russia.
Just saw this bit of news:
When I worked for a corporation that sent emails to its customers, this was policy. No clickable links to pages that required authentication. We also sent PSA emails from time to time informing our customers “XYZ Bank will never send you an email with a login link”. Can’t say this is followed 100% by other companies, but it does seem to be followed pretty broadly, especially among larger ones.
Identifying Phish
And here I was intrigued that Adam choose to focus on a rock band and how to identify something about them? I thought it had to do with the various iTunes/Music/Apple Music discussions going on. (The band came before the scam: Wikipedia: Phish is an American rock band formed in Burlington, Vermont, in 1983.)
Simon, thanks for the enlightening edumacation on the matter. Sure is the wild, wild, west out there. Gratefully, I’ve acquired a bit of a ‘spidy-sense’ and am pretty cautious about taking the bait from phisermen.
Cheers
The best way to fight phishing attacks is to a password manager like 1Password and use it.
You can’t use clues any more. Phishing has gotten good. Phishing attacks will use misspellings like replacing an “m” with an “rn”.
https://amex.comlooks very similar tohttps://arnex.com. Or even get a security certificate. Sometimes Cyrillic characters that look like Latin characters are used in domain names.However, if you go to a website, are asked to log in, and 1Password doesn’t automatically fill it in, you’re being phished.
I had the same feeling, Jack. Followed closely by “Hmm, “phish” as a noun, but not referencing the band, that is suspicious syntax, it might not be from TidBITS.”
This isn’t always true. I have several sites where I’ve set up an account, but the login uses a different URL (like
login.account.comor some such variation) so 1P won’t automatically fill in the password. I have to choose it manually from within 1P.I suppose I could set up a duplicate entry in 1P with the secondary URL, but then if I ever change the password I have to remember to do it in both places. (And most of the time my login is via FaceID, so it’s not an everyday hassle.)
If the 1Password URL is
https://login.foo.com, 1Password won’t automatically log in unless the url ishttps://login.foo.com. However if the 1Password URL is justhttps://foo.com, 1Password will automatically login if the URL ishttps://foo.com,https://login.foo.com, orhttps://admin.foo.com.When I create a new password, I’ll make sure I make the URL to the base URL with no subdomains.
You can add multiple URLs in 1Password. For example, 99 Percent Invisible can be either
https://99percentinvisible.orgorhttps://99pi.org.Yeah, I wrote about this scam a while back too.
That was nagging at the back of my head, but I was really thinking of muscle spasms. I’ll change it.
Actually, I just looked at the site that’s the most problematic for this (it’s a banking site and their app will often stop using FaceID after a bit, forcing me to put in the password, but won’t autofill from 1P) and the URL of the login site is completely different. It’s like the main site is
alocalbank.comand the login site isspecialbanklogin.com– I think the bank is too small to support their own login system so they license it from a third party. I have seen “are you sure?” warnings from 1P because it assumes I’m giving my password to a different site than the URL, which does make me nervous.I never thought about doing that! I just added the secondary site, so next time it happens I’ll see if 1P will autofill. That will be safer and easier.
Well, I want to find the person who decided that HTML formatting for email was a good idea and punch him/her in the mouth.
It’s worth learning how to view the message source and inspect the email headers to see where the message actually originated from. Here’s one guide: Find Out Where an Email Came From (Read Email Headers) | IT@Cornell
But part of the problem is that outsourced messaging is pretty much undistinguishable from spam email, and a lot of companies, including the so-called “professional messaging service providers” don’t properly set up things like SPF. Of course, CIOs are not held responsible for the problems their outsourcers produce. (And I see this particularly with UNH’s outsourced IT, with multiple messaging systems, multiple message originators all claiming to be a valid [email protected] address.)
Just got this text. Non-native English speaker, head-scratching inclusion of “copyright” information, and weird non-Apple organizations listed are just a few of the tell-tale signs of phishing…
Actually you can set up both urls in the same entry so that it will autofill with either url. Depending on how you’ve set up…you might have to choose edit, then add field and choose url but in mine the alternate url field is already visible when I select edit.
@peter728:
I read your post and shuddered when you wrote that you rang the number in the email you received.
A better course would have been, after logging into the PayPal site from a bookmark or typing the URL by hand, to look up a contact number on the site.
When I clicked the Contact link at the bottom of the PayPal home page, this text was at the top of everything:
On the contact page there were links to chat as well as a phone number. I would expect that the phone number linked from the PayPal contact page was not the one in your email.
If I’d have seen any one of these phishing messages, it would have immediately been deep sixed.
My motto to my kids and grandkids is to trust everything you see on the Internet and trust nothing on the Internet. The real answer is in-between.
Mike
Yes Jonathan, you are quite right! I was really duped and I had thought I was pretty smart and scam aware too. I have just googled the phone number that I rang and it is listed as linked to a bank scam and is quite different to the real UK Paypal contact phone number.
What completely fooled me was that I DID separately log in to Paypal, without replying to the email or clicking on the link or at that point considering phoning the number as I was sure that email was a phishing email, but then I discovered that by independently logging in to paypal.com my account WAS showing a payment request for £989.99 from the person named in the email. I even checked the email’s full headers which looked good, so then I completely - stupidly - trusted that phishing email as being genuine and consequently falsely trusted the phone number it contained. Later I found on the Paypal site a record of my account having been accessed from a computer that was not mine - a useful security check I recommend everyone with a Paypal account should be aware of.
The scammers were very smart. They had sent me a phishing email to warn me about the fraudulent payment request that they had made! So, their real aim was not to gain £989.99 from me via Paypal (unless I would accidentally click on the Send Payment button or email link which some people in a flurry might do) but to get me to hand over personal bank details. What I cannot explain is that after I independently logged in to my Paypal account why did my attempt to click on the button cancelling this payment request result in an error message? It was only after receiving this error message that I wanted to make a phone call - although hours later the cancellation button did work. This failure to be able to make an online cancellation was crucial for the scammers to be able to execute their scam, certainly in my case. Could there have been any insider involvement in facilitating this scam? Is it easy for anyone to make a payment request from a Paypal account? The phishing email had a Send Payment link. Why did the scammers not simply falsely label this link as ‘Cancel Payment’ rather than ‘Send Payment’ so getting the victim to unwittingly authorise £989.99 being taken from their account?
The end result seems to have been that after I rapidly cancelled both my bank cards that I’d divulged details of and then afterwards closing my Paypal account the scammers failed to take any money, but their shrewdness in social engineering has to be admired. This was a well targeted attack, with a tiny sum deposited into my Paypal account effectively slowing down account closure. Unfortunately here in the UK it is open house for scammers as the police resources don’t match the scale of the problem. I have reported it to actionfraud.police.uk but media reports suggest that only actual losses over £10k stand any chance of being investigated.
On the flip side, I’ve received genuine emails that look phishy. This includes financial institutions. The language is usually OK, but the sender’s address and subject line can be obscure, and the messages may be brief and badly formatted.
I like the idea of not including clickable links (though I see those all the time in genuine emails), but I think companies could do more to check that their emails look professional. Then again, here in the UK many financial websites are pretty crummy.
That’s Apple’s Irish real corporate name and address. The only part that’s wrong is the misspelled name of the country (and the fact it’s actually in the Republic of Ireland, because “Ireland” is an island, not a country).
Obviously the URL is bogus.
Well, that would be the correct spelling of the country, in French.
Just lately I’ve been seeing a lot of emails like this one - it’s full of phishing clues, but one of my clients fell for one just like it. This is addressed to me - from me. Except that I’m not in China and my return address to me is not in Russia!
Here’s another one I got a few days ago that I could easily see convincing someone to click. Simple is more believable.
That’s a really big PDF attachment for a report, though
My SO bought me a gift from Verizon, forgetting the email would go to me and he couldn’t stop the sales rep in time. I saw the email come in but it was plain Jane with an attachment that said Purchase Receipt. I hadn’t gotten any notification that someone was in the account so I didn’t open the attachment and junked it. 10 minutes later he calls and apologizes for spoiling the surprise and I just burst out laughing and told him I’d junked it thinking it was spam! Then I had to unjunk it in case he needed it back.
Diane
Yes, how hard could it be to set the subject to: “Purchase receipt for your shiny gadget / subscription plan / whatever” ? (Not that you would have wanted that in this particular case )
)
PDF bills and receipts are similar. They’re all called “download.pdf” or meaningless strings of digits. I use Hazel to rename them, but I wish they could be sensibly named in the first place. It can’t be very difficult.
Clearly a Very Important Report that Adam should download without delay.
No I would not have wanted a descriptive subject, and I didn’t even guess what he got :)
This is the screenshot, it still looks like spam to me! Unknowingly or not, Verizon’s cheap looking email saved the surprise :D
Diane
I’ve seen a lot of that, too. I wonder how much of it gets caught by spam filters, which may account for bills that go unpaid.
@ace
You’ve hit the a home run with this article.
Your piece is linked from Bruce Schneier’s Schneier on Security site today.
Congratulations.
Thanks! I think that’s my first appearance on Schneier’s site.
Spam filtering effectiveness varies greatly among email service providers, which is one reason I have been using Runbox.com for years now. . . The Norwegian employee-owned company focuses on user privacy and security. And when it comes to spam, their filtering is very effective. Hardly any spam makes it past Runbox and I cannot recall the last time I got a phishing message. Runbox customer support is also among the very best I’ve experienced.
One of my favorites was similar to the first scheme you described, telling me that a certain email’s password was going to “expire” in a few days. It came from “Web-Mail Support”
This was followed by a button labeled “Keep the same password”.
Since I am, in fact, the email support for our very small non-profit, and set up all the accounts and passwords, I just blocked them and ignored it.
Anything that takes me a few minutes to decide if it is spam is dangerous. For people in a hurry, worse. This came today, complete with the footer about “Learn to identify Phishing”. I ended up looking up the LLC “company” and the phone number before deciding that it was a just better version of phishing. I didn’t click on anything.
About a month ago I ordered a small jewelry item from a well-known retailer in Scotland. When the item shipped, I received a notice from FedEx that the item had been consigned to them (definitely from FedEx.com, but also another from “Fedex” (note the erroneous capitalization), and the “From” field in the basic email headers listed the sender as [email protected]. Over the rest of that day I received another dozen or so emails purporting to come from entities such as clothing stores, IT companies, etc., formatted in similar or identical fashion, but obviously fraudulent in origin.
Because this bloom of fraudulent emails started immediately after the shop in Edinburgh contacted FedEx, I worried that my personal information (email address AND possibly my email password) might have been captured by miscreants. I’ve been told by fellow members of an independent Apple Ecosystem listserv that they too have received those messages (from the same bogus domain), which I find a bit reassuring, but I still have a question about Apple’s email security.
I do know that Apple has done things to make its iCloud email platforms more secure, I still wonder about a system where the email password MUST be the same as the password one uses to purchase hardware and software, update computer operating systems and applications, and subscribe to entertainment platforms. Is that a concern to anyone here?
Receiving fraudulent messages sent to your Apple mailbox doesn’t say anything about Apple’s email security.
Anybody can forge any address on an e-mail message and send it from any server.
Now if there was mail where the “Received” headers indicate that it came from your mailbox, that would be reason for concern, although that may be hard to detect, since those messages would probably be sent to other people.
As for why you got all this spam after shopping at one retailer, I would guess that their computer system has been hacked and the crooks got your address from them. Or worse, they may be selling their customer lists to advertisers. After that, it’s open season.
That was my conclusion as well. When I contacted the retailer, the instant reply was “oh, no, that could NEVER happen to us; we contract with IT professionals who make sure we’re protected.” I was tempted to say “just like T-Mobile, and even LastPass?”
But my final question about Apple’s own email security could have been stated more clearly. Actually, I have two questions:
Is it good design to have the same identifiers and security (the Apple ID password) for one’s financial transactions with the world’s richest company (buying hardware, obtaining support, subscribing to entertainment services, etc.) and for one’s everyday trips into an environment (email) that’s known widely as far more smarmy than the bar in the very first Star Wars Movie?
I’m aware that Apple is promoting “hide my email” addressing, and I don’t really understand how that works. I converse with dozens of people by email every day, and many hundreds over the course of a month or two. What I don’t understand about this new security effort is how my correspondents will know who I am if my email address (the FROM field in my headers) is just gibberish. If, every time I send an email message, Apple creates an encrypted substitute for the “FROM” field unique to that one interaction, won’t that consume ENORMOUS amounts of server space eventually? If, on the other hand, Apple creates a catalog that substitutes the SAME bit of gibberish each time I communicate with a specific email address, doesn’t that risk eventually becoming an easy way to resurrect that chain of correspondence? I’m pretty sure I’m not understanding how this is supposed to work, even with the help of Joe Kissell’s latest Take Control of Apple Mail ebook .
Thanks so much.
Yep. I’ve gotten that kind of runaround from even bigger companies who should know even more.
Like when I got a virus from Microsoft’s Windows update server (proven because I wiped the computer and reinstalled Win95, then reinstalled the virus scanner, which found nothing. Then ran Windows Update, and it immediately detected an infection.) They responded that it’s not possible because they have automatic scanners, so it must somehow be my fault.
And even longer ago when I found a bug in Borland’s Turbo Pascal for Windows compiler, where it generated incorrect machine-language code. I wrote a short 10-line test app and sent it to them, along with the generated code as proof. Their response was that they have no bugs. Then they told me how to change the test program to get the correct results (basically removing the code that triggered their bug).
So I am never surprised when some company, no matter how big or small, reacts to critical problems with flat-out denial.
I would prefer that they provide the option for separate passwords. But I’m not convinced that this is a big problem. If someone manages to log in to your e-mail, that’s a big problem, but I rarely ever hear stories about things like that, and when I do it’s always the result of either phishing or an easily-guessed password. People forging your address on mail sent through other servers is impossible for anyone to prevent.
See What is Hide My Email? - Apple Support
I don’t use this feature, but according to the above page, you request creation of these random e-mail addresses. You give it to whatever people or web sites you like.
I suppose you could generate a new address for every mail message you send, but I don’t think that is the intended use-case. And I wouldn’t recommend it, because legitimate recipients will likely decide that you are a scammer and will block all further communication.
If you generate a new address for each service (web site, store, etc.) you subscribe to, then you should be able to tell who is selling/leaking your address based on where the spam comes from. (I assume you see that address in mail Apple forwards to you.) If you can delete the generated addresses later (I don’t know if you have that option), then it’s a good way to cut-off addresses that have become compromised.
I don’t think the purpose is to hide a chain of correspondence. If you need that level of secrecy, you probably need a different product. I think the goal of Apple’s product is to simply keep to real e-mail address hidden, so identity thieves will have a harder time tracking it to your other accounts, and so you can abandon it (when it gets compromised) without having to abandon your real address.
I guess I should try it out with a few people to whom I send messages routinely, just so I can get a sense of what happens in my own inbox and sent mail box if I use it. I don’t understand very basic things, such as how responses to hidden-address email find their way back to me. I guess I could actually just hide my iCloud mail address in a few messages I send to one or two of my own mail accounts with other providers, or even messages I send to listservs to which I subscribe, but I assume the hiding will result in the listservs’ automated processing rejecting such messages. It seems to me it’s not meant to be a “use it all the time” tool.
I assume Apple sets up mail-forwarding for these addresses. So a message sent to it (to an Apple server) will result in it being forwarded to your iCloud mailbox. If these random addresses are served by the same server that handles the real mailboxes, then this forwarding should be a very quick and simple procedure - just look up the destination mailbox and drop it there.
The web page seems to indicate that when you receive a message via one of these random addresses and then reply to it, the reply will appear to come from that address. This should be no problem if you are using Apple’s mail apps (Mac, iOS or the iCloud web site), but I can’t see how that would work for a third-party mail app, unless you explicitly configure it for each such address. (But maybe there’s an e-mail standard that I’m unaware of that allows this to work in a portable fashion. I haven’t looked.)
That’s not what it’s for. It’s for signing up to services to hide your real email from them, so that if you ever don’t want that service any more, you can just delete the email alias and they have no contact real info for you. Or if they leak that email and you start getting spam to that address, you know they leaked it and can block that address.
While I don’t use this for a “real” service that already knows a lot about me (such as Amazon, which is going to have payment information, my address, and other details), but it’s great for apps that require an email address to set up an account, temporary services you want to test before committing, etc. I use it to sign up for things like fast food apps, etc. which track reward points and give you coupons, games, web apps, and other “throwaway” accounts.
There is someplace where you can go to actually manage these email aliases, but I can never remember where it’s hidden when I need it.
From memory it’s something like
Settings > Apple ID > iCloud > Hide My EmailWonderful that preferences search didn’t bring that up when I searched for “hide” and “email” . I tried both Mac and iPhone. Bad Apple.
. I tried both Mac and iPhone. Bad Apple.
That’s exactly like the PayPal phishing I documented in the article. It’s not real spam since it’s sent legitimately through PayPal’s systems, but it’s absolutely a scam that should be reported to [email protected]. I’ve gotten a bunch of these, and I always report them and then delete them without marking them as spam.
I don’t think this is problematic. In fact, I’d suggest that you’re actually reversing the two examples in importance: email is much more important to protect than something you can make purchases with, because control over someone’s email gives them control over many other accounts.
The real key is two-factor authentication, which prevents even a compromised password from being used to break into your account.
And, wherever possible, use 2FA that does not depend on receiving text messages for the response, so a SIM swap scam won’t neutralize that second factor.
I prefer using TOTP code generators, like Google Authenticator (among many that implement the same algorithm). Once initially configured, they generate all their codes locally, without any data exchange with the remote service. So there’s no data to intercept.
As I understand it, Apple’s 2FA is also TOTP (but possibly with a different algorithm). Although it receives notifications from the network, the actual code is generated locally and is not received over the air.
Unfortunately, you don’t always have a choice. Some systems (including banks) insist on sending you SMS text messages or e-mail as a part of their authentication process, which won’t help you if your phone number or mailbox has been compromised.
I have two methods I use for
Sign the f()ckers up for spammy newsletters.
Also, report the phishing to phishtank[dot]com. This way it gets verified and added to antivirus software as malicious. Any spam email, I report to spamcop[dot]org, any suspected virus gets passed through virustotal[dot]com
One thing that is about the easiest way to test where the email came from is in the picture.
I try to always go directly to the location if asked to go to “my bank” and log in directly.
Although I would agree that this is the first place to check for phishing, it’s not the last. That field can be easily faked and does not positively identify the source of the message. The full headers showing the where the message was first received need to be examined in order to access the true source of the message.
See also this recent thread:
Quite a lot of information in an e-mail’s headers can be forged, so you need to know what to look for and what to ignore when determining if mail is real or not.
Many times, it’s not possible to know conclusively, in which case you should assume it’s fake and proceed accordingly.
Refusing to click on links from unexpected messages (instead going straight to the source, like your bank, with a URL you know to be valid) is a good practice in general these days.
Of course, if the phish is looking for a direct response, you can also check the "Reply-To:’ header and be sure it is going to a reasonable address in the real domain. As the phisher needs to see the response, it is less likely for this to forged if the real domain has not been hacked.
Scanning the headers is not real hard to pick up some information. I figure if I send the phishing e-mail to an IT person, they can figure out the headers, and what to take action on, much better than I can. Especially if the headers contain info that shows the e-mail originated on their site, and the sender does have an account on their server.
No, that’s what https://spamcop.net is for, not some random IT guy that you hope has some spare time to deal with your issue.
Al,
If the e-mail was sent from one of his servers, it IS his issue! Either an employee has gone rouge or an intruder is using his server. He needs to deal with either possiblility!
No. Please don’t trust what you see there. This cannot be repeated enough:
It is super easy to spoof header information and put into From: whatever a scammer wants. Do not trust anything you see there as a guarantee for anything.
This on the other hand is sound advice.
Always go to the company/service website yourself, manually typing in the address or using your own bookmark. If the email was legit and you need to do something related to your account with them, they will tell you once you log on. The massive advantage of this is you need to trust only yourself about who you are dealing with. You initiate communication with a known entity using your own URL information. You do not rely on a link provided by any external party. This way you always know who you are dealing with.
I have yet to encounter a company or service that will send me a link to do something which I can only access using that email they sent me. If I truly need to do something, logging on to my account with them will always give me the same option. In fact, many companies will immediately query me on the task they want me to carry out as soon as I log on (like my utility that will ask me to verify my contact details are up-to-date before I can do anything else on my account with them). No need to follow any email directions or use any email links. None at all. Using such an email as a reminder is fine, following its links is not.
Agree.
I’m sure it has happened to me (and I wish I could cite a specific example); it is extremely annoying, for the reasons you mention. My general rule is never to click on a link in email, although there are exceptions (verifying a registration being the most common).
Partially related is when an email tells me to call and provides a number that I have not recorded. This happened with a bank, and a search at the bank’s web site did not find the number, so I used my preferred search engine. It returned sites that said the number was legit and it returned sites that said the number was a scam. (“Ask the internet, and pick the answer you like.”) Any advice for that situation?
Me, I’m pretty certain I’d never call an unknown phone number suggested in an email.
I have yet to encounter a serious company that will tell me in an email I need to call them on the phone.
If they need to talk to me, they will either call me (which opens another can of worms…) or they will send me a proper letter. Either way, I will make sure to initiate the call myself to a number I have on file and if that requires a callback, so be it. No way I will just take some email or call and assume it’s legit.
I realize that this is not a timely reply but there are email provider options that do a much better job at preventing phishing and spam from reaching your inbox. Of course, it may cost a bit more than outlook.com but when your sanity is at risk, isn’t that worth spending pennies a day for relief?
I’ve used the privacy-oriented email service Runbox.com for years now and I cannot recall receiving a phishing email in recent years. . . Its server-based spam filters do an outstanding job. The small amount that gets through to me is snagged by SpamSieve. No spam reaches our family inboxes.
Using the Runbox website to “train” the filters is easy and customer support really is 24/7 if assistance is needed. The company is based in Norway, which has no downsides as far as I am concerned.