Alternative Ways to Protect Yourself from Being Spearfished
If you, or people you know, have a public presence, high net worth, or something desirable to online thieves, conventional security best practices may not be sufficient. Increasingly, online thieves are targeting individuals directly via a technique called “spearfishing,” which relies on the shocking ease of stealing a cell phone number and then using it to reset passwords (see “SMS Text Message Login Codes Autofill in iOS 12 and Mojave, but Remain Insecure,” 4 October 2018). Authenticator apps are the generally accepted solution to this problem, but they can be problematic for a number of reasons, including being too difficult to use for non-technical users.
My partner Caroline Green and I co-own a Mac consulting firm in Manhattan. This year, we’ve seen two cases of spearfishing and heard of several others. In the cases we worked on, several critical accounts were stolen, such as email, domain hosting, and social media sites. While we were able to recover most of them eventually, there’s no guarantee that we could do so successfully in other situations. Further, the accounts were inaccessible for days, and reputation damage could have easily occurred via abuse of the accounts.
We worry that spearfishing will become more common as the tools and techniques of malicious actors become more sophisticated and widespread. The challenge for us as consultants and tech experts is to be able to offer our clients—especially those with high profiles or high net worth—comprehensive online security in a way that is easy for them to manage.
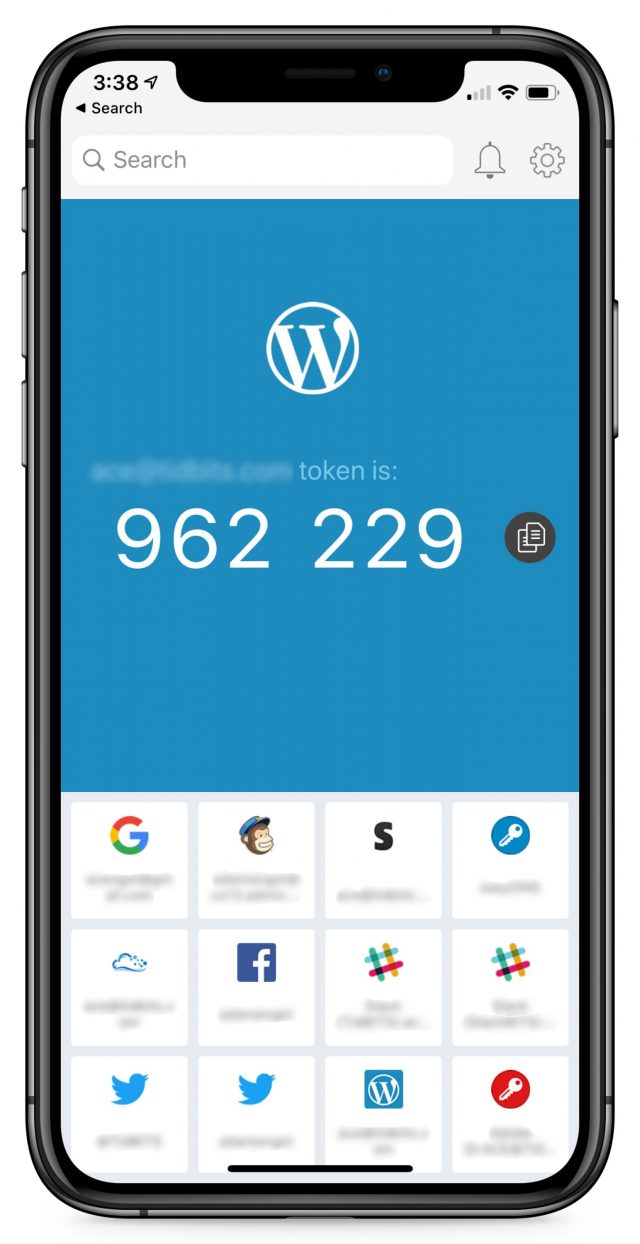
We came up with a technique that uses Google Voice text messages as an alternative to authenticator apps—although it requires a bit more setup, we think it’s easier to use and understand, plus it acknowledges some people have to allow trusted assistants or consultants access to their accounts. Our goal in sharing this technique is twofold. First, we hope that it might help other people looking for a similar solution, and second, we’re hoping outside scrutiny will reveal any potential weaknesses or vulnerabilities.
Where Are You Exposed?
First, let’s review some basics about keeping online accounts secure.
- Prioritize Your Accounts: Not every account, such as your average retail or content site, needs bulletproof security. But others do. These include your email account, Apple ID, Google account, Microsoft account, social media sites, financial sites, domain registrar, DNS host, Web host, Web site content management system, online business applications, cloud storage, cloud backup, and photo sharing sites. In short, you should put more effort into protecting any account that contains something you wouldn’t want to lose, wouldn’t want to be revealed to others, or wouldn’t want to misrepresent you if an attacker were to use it.
- Use Strong, Unique Passwords: We’ve all heard this advice, but it bears repeating. Do not try to memorize every password. Doing so means reusing the same passwords, or variants of a similar password. The risk is that if any one site suffers from a security breach, a depressingly regular occurrence, thieves now have access to all of your accounts. Every online account needs a unique, computer-generated password, remembered by a password manager, such as 1Password, Dashlane, LastPass, or at least the simpler ones built into current versions of Web browsers. I know only three of my passwords: the administrator password for logging into my Mac, my 1Password master password, and the password for my Apple ID. 1Password knows the rest.
- Use Two-Factor Authentication: Two-factor authentication (2FA) is when you enter your password and then get a separate code or prompt, via text message, onscreen dialog, or authentication app, to verify that it’s really you, and not just someone who knows your password. Most Apple users see this when signing in with their Apple ID on a new device. You should enable 2FA for any important site that supports it. There are several flavors of 2FA that I’ll discuss more below.
- Provide Fake Answers to Security Questions: In general, if you have 2FA enabled, you shouldn’t have or need security questions. But some sites require them, and in those cases, operate under the assumption that there are unseen, nefarious databases about all of us that correlate all kinds of information we might assume to be separate and private (the best-known are called “Facebook” and “Google”). Imagine that anyone can learn everything about you with a few quick searches. One way to thwart attackers from hacking your security questions is to make up nonsense answers—different for every site, of course—and keep them in the notes area of your password manager. What was the name of your first pet? “Macatma Gandhi.” What’s your birthdate? Pick a random date like “1/9/1919.”.
- Think You’re Important: It’s normal to think that good security is for other people because you’re too insignificant to warrant a thief’s attention. Alas, it’s 2020, and we’re all a lot more visible and important than we may believe we are. The phone number theft I’m about to tell you about was motivated simply because its owner also held a two-letter Instagram name—highly valuable on the Dark Web black market, as it turned out.
Your Cell Phone Number Is the Weak Link
Even if you do all of the above, you may not be safe. One of the two account thefts we saw involved a sophisticated attack in which the victim—who used strong passwords and a password manager—had thieves port his cell phone number from his SIM card to theirs. Once they had a phone with his phone number, it was trivial to gain access to his accounts by requesting password resets, since the confirmation codes were sent by text message.
You’re probably wondering how this could have happened. The thief used social engineering to persuade someone at the victim’s cellular provider to transfer the number. Lest you think that’s an unlikely scenario, consider it from this angle: anyone from anywhere in the world can call your carrier’s customer service, and every single employee who answers the phone has the capability of putting your number on another SIM card! That’s a lot of exposure. Most carriers offer a transfer lock, passcode, or PIN that they’ll require before porting a number.
I called my carrier and activated a PIN, and I keep it in my password manager. I strongly advise that you do the same—here are informational links for AT&T, Sprint, T-Mobile, and Verizon. However, I don’t want to rely solely on a carrier transfer lock. I don’t know how well they are implemented, and I assume that some thieves are really good at what they do and may be able to talk their way around it.
The Problem With Authenticator Apps
Security experts usually recommend that, rather than receiving a text message for two-factor authentication, you instead use an authentication app, such as Authy (see “Authy Protects Your Two-Factor Authentication Tokens,” 6 November 2014), Google Authenticator, or Duo Mobile. The app provides, on its own, a code that changes every 30 seconds. Some password managers, such as 1Password, can operate as an authenticator app as well. We agree that authenticator apps are a very secure method of getting a 2FA code.
The problem that we’ve found with standalone authenticator apps is that they’re not especially well designed. Our clients have difficulty setting up new accounts in them, and the apps are difficult to use even once set up. They’re serviceable for you and me, but I’m thinking about people who don’t read TidBITS. Even people who are already using a password manager that has authenticator app capabilities would have to scan QR codes and absorb concepts like “time-based one-time password” in order to set up 2FA.
Furthermore, for people like you and me, standalone authenticator apps have liabilities:
- If an assistant, colleague, or consultant needs to access an account, both people have to configure the authenticator app for the account at the same moment, with the same seed.
- Sometimes the account name shown within the app is obscured, causing confusion if the user has multiple accounts at the same site.
- Support for authenticator apps on a desktop computer may be limited, hard to use, or nonexistent.
- There is some risk of losing the 2FA codes after a device switch (we’ve seen this with Google Authenticator).
- The user isn’t told exactly what to do during login—they need to remember to look at the correct authenticator app and find the single correct code from among the many listed.
- Many sites don’t support authenticator apps at all and instead require that you be able to receive an SMS text message for 2FA.
1Password (and perhaps other password managers) elegantly addresses many of these concerns, such as by putting the security code on the clipboard during autofill, and notifying that it has done so. But building 2FA support into a password manager is not without its own issues:
- Having both the password and the one-time code in the same app creates a risk of being permanently locked out of accounts if you lose access to the password manager due to a lost master password or data corruption.
- Similarly, if there were some sort of breach of your password manager, a thief would have easy access to all accounts, despite 2FA being enabled.
- Giving a colleague or other trusted party access to an account still requires either simultaneous setup, or a more expensive “Teams” plan that adds complexity by having a secondary shared vault.
- Again, many sites don’t support 2FA via authenticator apps, instead requiring that you receive an SMS text message.
We went looking for another solution.
Google Voice as an Alternative to Authenticator Apps and Cell Phone Numbers
Google Voice is a free service that gives you a phone number suitable for both calls and text messages. You can access it via the Google Voice iOS app or a Web browser, and both can provide notifications.
The Google Voice service is attractive because it solves a lot of the problems we discussed with real cell phone numbers and authenticator apps:
- The phone number can’t be ported without login access to the associated Google account—there’s no one to fall prey to social engineering.
- Text messages are easily accessed from any browser or phone, making it easy for an assistant, colleague, or consultant to receive a code.
- Users get a notification on their phone as they would with any text message, so there’s no change in user experience.
- It’s easy for our clients to set it up for new accounts—all they have to do is provide an alternative phone number, rather than fuss with an authenticator app and a QR code.
Our approach is to create a new Gmail account—with no real, identifying information in the email address, first name, last name, or birth date fields—to host this Google Voice number. Then we add the Google Voice app to the user’s iPhone (and iPad if necessary) and sign them in. Because the account email address in no way identifies them and is used for nothing other than hosting the Google Voice number, a thief should never come across it. And, even if one did, they wouldn’t know to whom it belongs. (If you do try this Google Voice approach, be sure to remove your real cell phone number from your account, which is added by default during setup. If you don’t, an attacker stealing your cell phone number would still get the Google Voice text message codes. Also disable the default forwarding of text messages to your email address.)
With a strong password, the Google Voice account is secure. What if those credentials were lost? This may be overkill, but for account recovery of the Google Voice account, should it be needed, we use another non-identifying email alias associated with the user’s iCloud address. The actual, non-identifying iCloud account behind the alias can either be checked directly or forwarded to our client’s actual email. So, if a thief were to discover the recovery address for the Google Voice account, they couldn’t log into anything with it. We also record the account creation date and fake birthday, as Google may ask for them during account recovery.
By using the Google Voice phone number, our clients can easily set up two-factor authentication on any account simply by using an alternate phone number. When a code is needed, they are actively notified via text message notification. An assistant, colleague, or consultant can access the code as well. And the alternate phone number can’t be moved to a thief’s SIM card without login access to the Google Voice account.
Downsides to Google Voice for Two-Factor Authentication
The most significant disadvantage that we can see to this Google Voice approach is that if you don’t send a text message or make a phone call every six months or so, the number expires. Google warns you about this, of course, but it is best to be proactive, as we are for our clients. It’s a good idea to forward all mail sent to the Google Voice account’s Gmail address to an actively checked account, so that any warnings sent by Google are seen. It would also be smart to set a biannual reminder on a calendar as well.
Some Web sites may reject a Google Voice number or may not accept text messaging as a primary means of 2FA. I have seen this in a handful of cases. For example, Facebook will not accept a Google Voice number unless it is the first number you add to the account. CrashPlan supports authenticator apps, but not SMS. For these kinds of accounts, you would need to make a strategic decision whether to use an authenticator app (or a password manager that acts as one), enter the real cell phone number, or do without 2FA. Also, some prominent Web sites don’t support 2FA at all (I’m looking at you, Spotify).
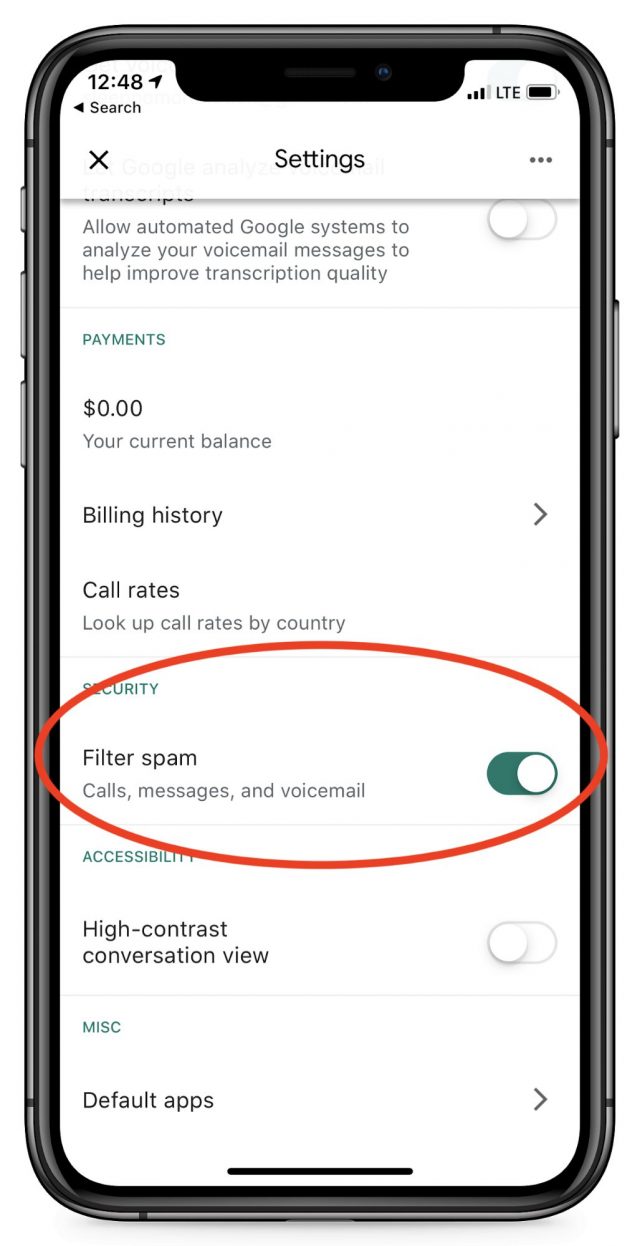 Adam Engst suggested another possible downside, which is the possibility of the Google Voice number receiving spam calls. We need to advise our clients to ignore all calls and voicemails in the Google Voice app. Better still, in the Settings area of the app, you can disable incoming calls, as well as filter possible spam, although this creates the risk of missing an important code if Google misidentifies it.
Adam Engst suggested another possible downside, which is the possibility of the Google Voice number receiving spam calls. We need to advise our clients to ignore all calls and voicemails in the Google Voice app. Better still, in the Settings area of the app, you can disable incoming calls, as well as filter possible spam, although this creates the risk of missing an important code if Google misidentifies it.
Finally, Google Voice is one of Google’s more peripheral products, so who knows if the company might drop it one day. Nonetheless, Google would likely provide sufficient warning for users to make alternate plans.
What Do You Think?
I’m not a professional security expert, but this system seems like it strikes the right balance between being safe enough and usable enough for our clients with high profiles or high net worth, or for those with an extra level of security consciousness. Do you see any glaring flaws or risks? Let us know in the comments.
Ivan Drucker is the founder and CEO of IvanExpert Mac Support in New York City. He is a former software quality engineer for Apple and began using his first Apple II in 1978, at the age of eight.

I am a huge fan of authenticator apps (I use OTP Auth), and with Apple’s Handoff technology, authenticators are a breeze to use (copy on the iPhone, paste on the Mac). I have a work-around for the what was cited as a limitation: “If an assistant, colleague, or consultant needs to access an account, both people have to configure the authenticator app for the account at the same moment, with the same seed.”
When the QR-like code (or seed number) is on-screen, I print a hard copy – which I store in a very safe location (e.g., safe deposit box or equivalent). This can be used any time later to seed another device, such as an assistant’s (and is a great backup in case an iPhone is lost or destroyed).
Ivan, I would have named that section of the article “The Utility of Authenticator Apps” and I suggest you look into OTP Auth (which isn’t pretty, but it is very well designed) for your clients.
This brings up a question: I have exactly one account that supports authentication, for which I use the built-in feature of 1Password. I remember it was slightly tedious to set up, but once done, it’s worked great for the last couple of years.
But I was disturbed to read in the article about this possibly breaking when you get a new phone. Then I realized I’ve gotten at least two new phones set I set it up and it still works fine. Is that because I’m using 1P instead of a different app?There was no QR code to save or print out that I remember.
While I got authenticator working, I remember being frustrated that there was zero info about exactly how it worked or what was going on. I’m assuming it’s secure, and it seems way better than SMS (the other choice), but the whole thing is rather mysterious.
I do wish more sites, especially banking and financial sites, supported more than just SMS for two-factor.
Google Authenticator is the main culprit with losing data between iPhone upgrades. Mine is completely empty now, even though I used it quite a bit before I found Authy (which syncs online).
The problem is that Google Authenticator was among the first, and is probably the best-known of these apps, even though it’s the worst.
I use Authy, but have never been able to get it to work on the Mac so I’m always looking up 2FA codes in its iOS widget and then typing them into the Mac.
Behind the scenes is a well-known, open algorithm, described in this Wikipedia article: HMAC-based One-time Password algorithm. Any device using this approach simply starts with the seed code, and calculates the current value. Keeping the seed code safe is the key to security (hence my suggestion of printing it and storing the paper safely).
I tend not to trust free software, and am willing to pay a little for software authored by a reputable source with a business motive to sell product (not your data). Good OTP authenticators take the extra step of being locked either by a passcode/PIN or biometrics (TouchID or FaceID), and encrypting the keys on the device (using the PIN or biometrics to decrypt them). I don’t use Google’s anymore.
Although 1Password and LastPass can handle OTP authentication, my recommendation is not to put both factor “eggs in one basket.” In the very unlikely event that one of them is breached, an attacker will have both factors.
For the Mac, I use the Authy Desktop app that appeared recently. It works like a charm although by appearance, it appears to be a Catalyst app, so its UI is less than terrific. Nevertheless, I’ve been using it for Mac authentication. Download it from https://authy.com/download/
Ah, I remember what happened. I’d had some trouble with the Chrome extension that was eventually resolved by Authy support telling me to delete it and reinstall. And then I switched to Brave and forgot to reinstall the extension. So I do have it working on the Mac now. It’s not great, but better than pulling out my iPhone each time.
@davidson if you have the organization and infrastructure to print and save QR codes, that’s super smart. Also, I haven’t checked out OTP Auth. Thanks for the tip.
I’d still be interested in any feedback as to whether SMS codes via Google Voice present any significant security flaws.
What’s dangerous about using normal SMS is that carriers do not make it difficult to SIM jack a phone, meaning that a clever person can trick a carrier to activate a new SIM on your line to them rather than you, and then that person gets all of your SMS messages (and phone calls, but for two factor auth that uses SMS, obviously that’s the vulnerability.)
A google voice number doesn’t use a SIM, so you are protected so long as your Google account is protected. However, you’d definitely want to turn off the message forwarding option that forwards any messages received on the Google Voice number to your cell phone number - you’d again be vulnerable to SIM jacking. You want to get the messages from the Google Voice app. The security “flaw” would be only that your Google account is sufficiently protected (strong password with two factor auth.)
Authy works on Apple Watch as well.
@ace I had the same bad experience with Google Authenticator, and I think you said this well. It’s the one I see most frequently suggested on web sites for 2FA, as well.
I use Authy as my 2FA application for Google Authenticator codes. I have versions on my iPhone, iPad, Apple Watch, and Mac computers (see my earlier comments about Authy Desktop). As I use Safari as my primary web browser, I don’t have it directly linked to my web browsing and must paste or type any of the codes.
You would think the Watch version (which I keep readily accessible in the Dock), would be one that I most often use, but it has one major failing; for some sites, there is no text showing the name of site being used–only the user name. Those sites, in other implementations, use the associated graphic to identify the site, but the Watch app only shows a generic graphic. So the watch app can be ambiguous for sites that use my usual email address for logging into them. Other implementations of Authy do show any associated graphics.
So, my usual procedure has become to start Authy on the device I am using during the login procedure; start the login in the app; and go to the appropriate Authy pane to get the code. If less than 15 seconds remain until a new code is generated, wait; otherwise, hit the 'copy to clipboard button and the go to the login page, paste the code, and tap enter. That usually allows enough time for the site to process the code before it changes.
So it sounds like 1P stores the “seed” in your vault so it remains valid even after device swaps, which makes sense. It also works between devices, which is good.
I’m not too worried about 1P holding both password and 2FA code; if someone gets into my 1P, I’m screwed anyway, so it’s not likely to matter that they have both. It’s worth the microscopic risk to keep things simpler and just have one app to hassle with.
The one thing I want to know. The only thing that interests me is how exactly did Bezos’ iPhone X get hacked with a simple video on WhatsApp?
Is there an issue with WhatsApp? If so, why would WhatsApp gain access to your entire phone? Is there a known bug in iOS? Was there a profile sent to Bezos and he had it installed that gave them access to everything on his phone? Did they have physical access to his phone?
Being an iPhone owner, I’d like to know exactly what types of attacks can be used on what is supposed to be the most secure device on the market.
The simple answer is that the details are not yet known, and the hack of the phone by a WhatsApp video remains a claim, not a publicly demonstrated and proved fact. We can assume that this was a security flaw in iOS as it existed two years ago, when this alleged hack reportedly happened, and, if true, is a security flaw that has since hopefully been patched.
The NY Times had an article about this: https://www.nytimes.com/2020/01/22/technology/jeff-bezos-hack-iphone.html and it was originally reported in the Guardian: https://www.theguardian.com/technology/2020/jan/21/amazon-boss-jeff-bezoss-phone-hacked-by-saudi-crown-prince
All that is publicly known at this point are in those two articles.
Yeah, I realize there isn’t a lot of information. Most security issues in iOS tend to be small leaks — a way to access someone’s contacts, etc. Rarely is it some exploit that lets you download everything on the phone.
However, I did find this article about several security flaws:
This maybe the right timeframe, and if it is, it looks like these vulnerabilities have been patched. However, I guess we don’t know what the next state backed hacker group has already discovered and keeping it secret.
The stuff I’ve seen about keeping your phone safe about the hack are things like "Don’t click on email links and enter your password. Always lock your iPhone. Maybe this is good advice, but it doesn’t stop these state actors.
An expensive zero-day exploit (or multiple) that hadn’t yet been patched in WhatsApp (and likely is now, for sure). Repressive dictatorships typically pay gray-hat surveillance firms who routinely purchase zero days, sometimes for very large amounts of money, to deploy those. A few years ago, the United Arab Emirates allegedly hijacked a UAE activist using three zero-days delivered through a single text message.
iPhone vulneralbilities? First two articles are from exactly 1 year ago, describing hacking that occurred earlier:
Inside the UAE’s secret hacking team of American mercenaries - Ex-NSA operatives reveal how they helped spy on targets for the Arab monarchy — dissidents, rival leaders and journalists.
https://www.reuters.com/investigates/special-report/usa-spying-raven/
AE used cyber super-weapon to spy on iPhones of foes:
https://www.reuters.com/investigates/special-report/usa-spying-karma/
and then a followup article in April by the same authors:
American hackers helped UAE spy on Al Jazeera chairman, BBC host
https://www.reuters.com/investigates/special-report/usa-raven-media/
“Karma provided Raven operatives access to the contacts, messages, photos and other data stored on iPhones. It did not allow them to monitor phone calls.”
“The hacking of Americans was a tightly held secret even within Raven, with those operations led by Emiratis instead. Stroud’s account of the targeting of Americans was confirmed by four other former operatives and in emails reviewed by Reuters.”
I’m a big fan of the Google Voice method for exactly what Ivan proposes. And his list of drawbacks is dead on. I’ve been using Google Voice for certain financial accounts when either I can’t use my main phone number (because it’s associated with another account at the same institution, and that institution has a one phone-per-institution limit!) or for access when I’m traveling.
I discovered a couple of years ago that due to (smart) protections added to my credit-union accounts, logging in from an unusual location would prompt a requirement to enter a second factor texted to a phone number. Unfortunately, at the time, I was in the UK and was using a local SIM, so I was unable to access text messages sent to my US number! I switched authentication on my return to a 2FA-protected Google account’s Google Voice number. (I wrote this up for Macworld’s Mac 911 in December, along with some other suggestions.)
Ideally, 2FA systems would let you entirely disable the use of text messaging, but I also agree with Ivan that most people can’t navigate the complexity of using 2FA with current setups. 2FA with SMS can be better than nothing, but for systems that let you use a text message to receive a password reset, a password-only account could be safer than a 2FA one! Someone can be unable to obtain my password, but steals my number via SIM hijacking — in this case, for sure, the Google Voice idea is much better than plain SMS.
Another thing not mentioned: Use differing email accounts. Many email services allow you to fudge the service. For example, periods in user email address names in GMail are meaningless. You can add periods to your gmail address to make it different for each service you use that email address as a user account:
are all the same email address to GMail.
In FastMail, I can append a pound sign, and then add anything I want after the pound sign:
are all the same email address.
It’s pretty easy to see the actual email address, but the hacker doesn’t know how it was modified as the user name from account to account. One of the first thing a hacker does when they break into service A is they go to service B and try the same user name and password. Now, they don’t know the user name or the password.
I ran into the issue of not being able to receive text messages due to temporarily disabling my usual cellphone SIM during a trip to the UK last month. The credit card account that I used for many of my transactions was protected by SMS-based 2FA. However, I had also provided the alternate option of a phone call to my Ooma VOIP home phone. So, while connected to my hotel’s WiFi, I temporarily enabled the associated app on my iPhone to ring when the Ooma number was called. I was then able to get the 2FA code from the call.
Of course, if the OTP authenticator is an app on your phone, then whatever locks you configured to authorize access to the phone is itself that second factor.
Even though Google Authenticator doesn’t ask for a PIN, someone needs to have my passcode or fingerprint to unlock the phone it’s running on. Depending on how secure the device’s file system is (and current versions of iOS seem to be very secure), that may be sufficient.
I haven’t used the Google Voice approach but I like the idea for certain accounts. I’m deeply wedded to OTP applications (mostly Authy and Duo) since those are used for work. Overall the advice here is solid and I look forward to things getting better over time, as they have within the Apple ecosystem at least.
Professionally I advice large enterprises to use both the “save the seed token” method (good if you don’t actively need the MFA), and the “save it all onto the latest iPhone you can get” option… but in enterprise environments it’s a phone with all wireless turned off, stored in a safe, ideally in a Faraday bag (for real).
Those aren’t practical for the average person protecting a bank account where you actually need the extra MFA on a regular basis, so that’s why I like the Google Voice idea.
The main thing, though, is to be aware and train your family members… especially older family. Bad guys are getting good even at tricking people out of their MFA codes.
You trust Google?
I tried Google voice many years ago and hated it. I found it not intuitive at all.
So far the only issue I have is with an old Yahoo mail account. I do barely use it, but there are times when messages come there that I want to see. But Yahoo wants me to provide an SMS number for account verification purposes, but it will not accept a Google Voice number. (I use TOTP whenever I can, and have about 15 accounts set up that way, but some accounts do not support it.)
For this purpose, yes. I trust that my account will be secure. I trust Google more for this than I trust Verizon Wireless to keep my number secure (though really I think I have little to worry about, I still think using a GV number when I must use SMS for 2FA as better than my Verizon number.)
In a battle between a scorpion and a snake, I’ll pick the one I can protect again the venom more readily.
International users are typically SOL on using GV at all, and even then the few that can use it cannot use it for SMS at all.
Also, IMDb is another site with zero 2FA enabled. I literally contacted them earlier today about it, but got the usual nondescript reply.
(yes not critical, but nonetheless important if you don’t want your info on there played around with or deleted maliciously).
The biggest problem that I can see is using anything from Google and expecting it to remain private
Leaving every other privacy argument aside, for the purposes of getting one time expiring two factor codes that you enter in order to complete the log in on a web site, I can’t see a privacy risk. You can create a gmail account with a random user name that you use for nothing else other than creating a Google Voice account and using it to get messages for this purpose.
allow me to ask stoopit questions.
How does something like Authy work? It seems it is cloud based, which, for some reason, makes me nervous; though I will admit to using one for some back-up.
I use Enpass for password, though it is a foreign owned company, which also makes me nervous.
But I found it easy to use. I haven’t engaged the sync part of it with my Android.
I don’t use Authy, but looking over their web site, it appears that 2FA codes are generated locally from an app, much like Google Authenticator does.
It appears that they use a cloud service to sync the keys across multiple devices and to implement remote-disable. This (I think) has the potential for a security problem, should an attacker find a way to sync one of his devices to your account, but I don’t know enough information to be sure about that.
Adam, I hope you realize that tapping Authy’s copy icon on the iPhone will also place the token on the Mac’s clipboard—just paste, no typing!
However, some site operators ask you to choose your cellular carrier, and in such cases, I’ve never seen Google Voice as an option. I’ve tried to work around this step, but it has never succeeded.
Your email address can be used to track you across the internet and is typically 50% of your login credentials. If it’s insecure to re-use a password, why are we re-using our email addresses?!
Abine’s Blur service proposes a different email address for each account, and those addresses forward to any of your real addresses; you can also read them on Blur and change the address to which they forward. Better yet, if the site spams you or sells your address, you can switch off the forwarding, either temporarily or permanently.
Doh! Of course, although I’ll have to see if it works in real-world usage. My experience with Universal Clipboard is that it’s pretty hit-or-miss.
Curious if you ever checked out OTP-Auth. I am now using it, but would like to hear your thoughts.
I am using OTP Auth on my iOS devices. I love that it is password protected and supports TouchID and FaceID. And that it can sync via iCloud and can backup its database, as opposed to Google Authenticator that leaves you SOL if something happens to your phone. And you can organize your records in folders, allowing me to separate work and personal authenticator records.
I quickly realized this would become one of my most used apps so I did an in app purchase for the pro version. I don’t think I needed the features but I feel that the author deserves some of my money.
Thank you for taking the time to offer your thoughts. Much appreciated.