OS Security Updates Address Three More Exploited Vulnerabilities
Here we go again. Bill Marczak of The Citizen Lab at the University of Toronto and Maddie Stone of Google’s Threat Analysis Group have identified three more Apple-focused security vulnerabilities that are actively being exploited. Although there’s no corresponding blog post that clarifies, as with the last time this happened (see “OS Security Updates Plug Image and Wallet Vulnerabilities Exploited by Pegasus Spyware,” 7 September 2023), it seems likely that these vulnerabilities are being used by the NSO Group’s Pegasus spyware.
One of the vulnerabilities allows arbitrary code execution while processing Web content, another allows a malicious app to bypass signature validation, and the third could allow a local attacker to elevate their privileges. To me (backed up by Security Editor Rich Mogull), that sounds like a full exploit chain.
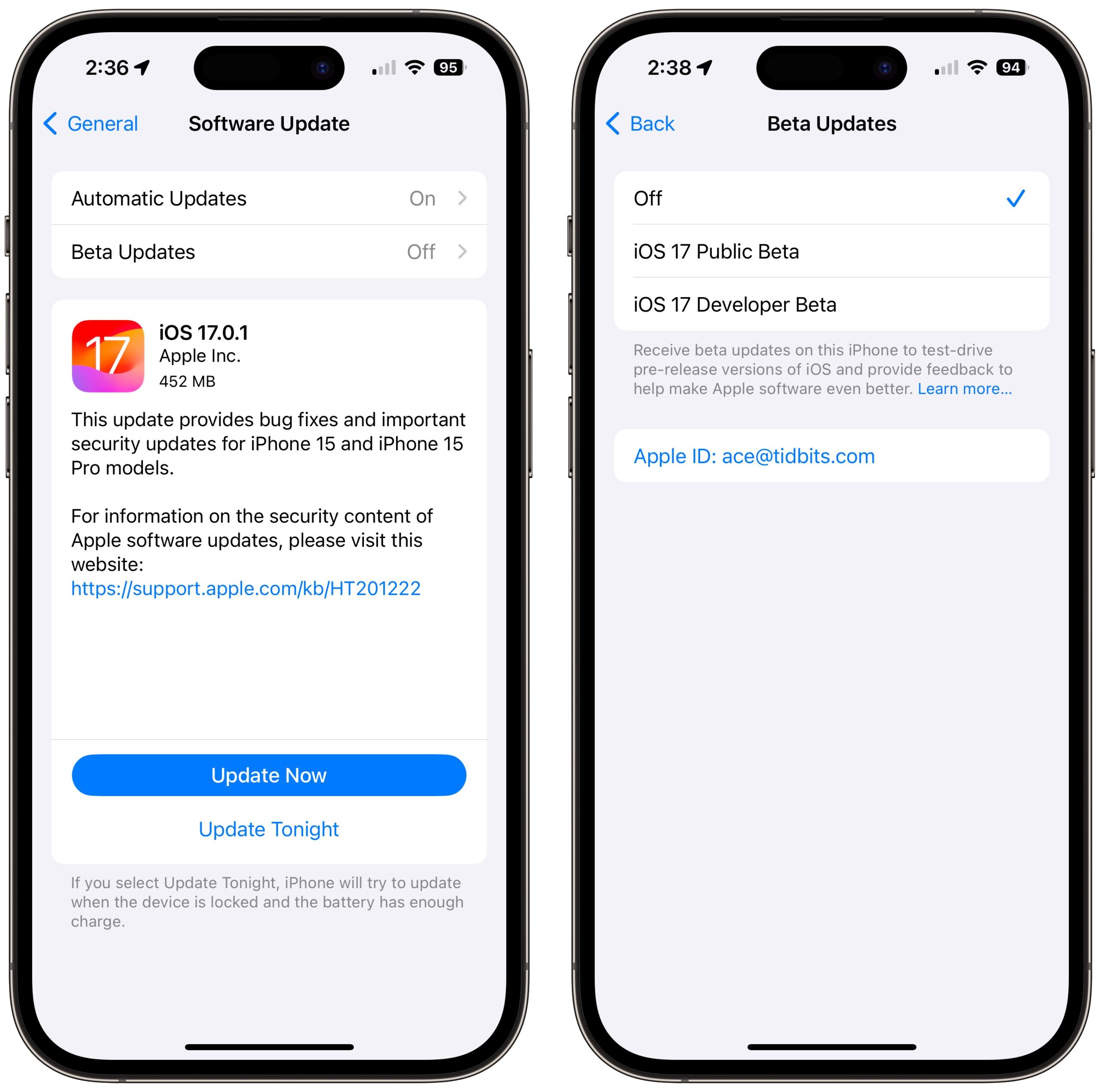
Apple has released updates for the two most recent versions of iOS, iPadOS, and watchOS, plus the two versions of macOS before macOS 14 Sonoma, which is due out next week. (You won’t be offered the updates for iOS 17.0.1, iPadOS 17.0.1, or watchOS 10.0.1 if you were receiving beta updates; turn them off to see the latest.) Install everything using Software Update.
The release notes are nearly identical for all the updates:
- iOS 17.0.1 and iPadOS 17.0.1
- iOS 16.7 and iPadOS 16.7
- watchOS 10.0.1
- watchOS 9.6.3
- macOS Ventura 13.6
- macOS Monterey 12.7
On the assumption that these vulnerabilities are being exploited by Pegasus and not something that targets a broader swath of users, I suggest that most people need not update immediately but should do so as soon as is convenient. For instance, take advantage of the Update Tonight option if possible. On my iPhone 14 Pro, installing the iOS 17.0.1 update took about 13 minutes.
Be aware that Apple says exploits targeting these vulnerabilities may have been used against versions of iOS before iOS 16.7. That may mean anyone whose device can’t upgrade past iOS 15 or iPadOS 15 remains vulnerable. Again, for most people, that’s probably not cause for concern, but if you’re worried about being targeted by a nation-state, get a new iPhone, upgrade to the latest version of iOS, and turn on Lockdown Mode.
And Safari 16.6.1 fixes the WebKit one.
How exactly does one get the new version (16.6.1) of Safari? I did a “check software updates” on my Mini running Ventura (13.6) and nothing (yet) shows up.
Nevermind - apparently Safari 16.6.1 is for Monterey and Big Sur only (but not for Ventura).
I haven’t seen the Safari 16.6.1 update offered to me just yet for Big Sur. Am I missing something? Mike
For anyone still looking for Safari 16.6.1 details, see
I see no updates from 17.01 to 17.02 for either my iPhone or my iPad yet. Maybe they’re releasing it by region? I’m in Tokyo.
I think iOS 17.0.2 is specifically for iPhone 15 series only. If I recall correctly your iPhone is one of the 13 series? If so the update is not applicable to the phone.
[Update: this is incorrect, see below]
iOS/iPadOS 17.0.2 was just now released for those on 17.0.1.
This update has no published CVE entries.
They did appear this morning for both my iPhone 13 Pro and iPad Pro. I’m updating now.
doug
Hah, I just saw the update on my iPhone as well and will be updating later (I am in Singapore).
The update is also available for iPad 17.
Well, that’s just confusing. Although I suppose it’s better if all iPhones and iPads are running the same version, and presumably the transfer problem was general to all iPhones.
A warning if you are trying to update to Ventura 13.6, which I just got an update notice on this morning. After downloading the update, my 2018 Intel Mac Mini took what seemed like an extraordinarily long time and appeared to have frozen with a dark screen. The only sign of live was a PING when I pressed enter; the dark screen would not show any action. This went on long enough that I thought the machine was frozen and tried a restart. When the machine came to life and I logged in, the machine finished the upgrade to Ventura 13.6 and Safari 17 and seems. I wish Apple would not make the Mac act look frozen when it was really upgrading!
That’s been going on for the all recent macOSs for some time now. Sometimes it’s just more noticeable if you sit there watching and the length of black screen varies. Apple must shut off all power to the screen at one point in order to conduct a firmware update, so there is no way to indicate it’s still running the installation.