TidBITS#906/03-Dec-07
We’re back from our week off with a wide variety of articles, starting with a call to vote in the just-opened 2007 TidBITS Gift Guide Survey. If you’re already shopping, check out the MacSanta and Give Good Food to Your Mac software promotions. Adam continues the theme with a look at PandoraBoy, a new Mac application that makes it easier to listen to holiday music via the Pandora online music service, and Catalog Choice, a Web-based service that helps reduce the seasonal onslaught of unwanted paper catalogs. Focusing on the world of the Macintosh more closely, Rich Mogull explains how to protect yourself from the concerning QuickTime RTSP security vulnerability, and Andy Affleck reviews Ambrosia’s WireTap Studio. Glenn talks about how to get Back to My Mac working through recalcitrant routers, examines Webjimbo 2, and shares a hidden Leopard trick for learning more about nearby Wi-Fi networks. Lastly, we release a preview of “Take Control of Easy Backups in Leopard” to cover Time Machine, along with six bonus stories and a neat widget you can use to display TidBITS headlines on your blog or Web site!
Vote in the 2007 TidBITS Gift Guide Survey
Thanks to TidBITS readers near and far, we’ve collected all sorts of weird and wonderful holiday gift ideas, along with a few painfully obvious ones (iPhone, anyone?). We spent the last few days arranging them into categories, tapping Twitterspace for a few ideas to flesh it all out, and creating the 2007 TidBITS Gift Guide Survey, which is now open for voting.
So please, come and rate the gift ideas about which you have an opinion (and if you don’t have an opinion, just skip that line in the survey). We’ll collect votes through at least the end of the week such that we can publish the final results by 10-Dec-07.
3G iPhone in 2008 Confirmed by AT&T
There’s no real surprise in this news from Bloomberg, but in speaking to a group of stockholders and financial analysts about a 3G-capable iPhone, AT&T’s chief executive Randall Stephenson said, “You’ll have it next year.” Steve Jobs justified Apple’s failure to include faster 3G cell data capabilities in the first release of the iPhone because of the lack of 3G chips with sufficiently low power consumption. But as Glenn Fleishman wrote in “3G Cell Data iPhone Now Feasible” (2007-10-14), chipmaker Broadcom announced a Phone on a Chip that would make a 3G iPhone possible in October 2007. So although Glenn was
speculating, it’s nice to see his informed speculation confirmed.
Will the 3G-capable iPhone use the Broadcom chip we wrote about? And, if so, will the new iPhone take advantage of the chip’s other capabilities to provide FM reception and transmission, a 5-megapixel camera, video conferencing, and output to an external display? Of course, there’s no guarantee Apple will tap Broadcom; Atheros and a number of other companies compete in the same space and Apple could easily be working with a 3G-capable chip from one of them that has different capabilities.
Stephenson also said he didn’t know how much a revised iPhone would cost, but it’s likely that Apple would keep the price point the same; the company frequently upgrades some parts of a device while taking advantage of reduced component costs elsewhere to maintain the same price. Amazon’s recent introduction of the Kindle, an electronic book reader with a 6-inch screen, a keyboard, and a 3G radio inside, shows that you can package quite a lot these days for $400, assuming Amazon isn’t subsidizing the price (see “Comparing Amazon’s Kindle to the iPhone and Sony Reader,” 2007-11-19).
It’s possible we could see an announcement at Macworld Expo in January 2008, though I expect Apple would wait until the 3G iPhone was actually shipping, and January might be too soon for that.
Protect Yourself from the QuickTime RTSP Vulnerability
On 24-Nov-07, the U.S. Computer Emergency Readiness Team (US-CERT) issued a critical alert for a new security vulnerability in QuickTime on Macs and PCs. This QuickTime flaw is especially serious because active exploit code exists on the Internet, because it can allow an attacker to take over your computer, and because there is as yet no patch to fix the flaw. In the security world we call this a “zero-day” vulnerability, and it’s a serious situation since it’s so hard for users to protect themselves without a patch.
Originally, the exploit code was designed for Windows, not Mac OS X, but there is now exploit code for both Tiger and Leopard. Until Apple issues a patch, we must all be extremely careful using QuickTime, which is inconvenient at best.
This particular flaw takes advantage of a vulnerability in how QuickTime uses the Real Time Streaming Protocol (RTSP) to stream audio and video over the Internet. If an attacker gets you to connect to a malicious RTSP stream, they can potentially use that connection to insert and run bad software on your system. How might you be enticed to connect to a malicious RTSP stream? By visiting a malicious Web page, clicking a link in an RSS feed, or clicking a link in a maliciously crafted email message.
Vulnerabilities in QuickTime are always hard to protect against without patching because of how tightly QuickTime is integrated into iTunes and Mac OS X. CERT advises Windows users to disable QuickTime entirely, but that’s unrealistic for us Mac types.
The best defense for now is simple caution and awareness. Avoiding risky Web sites and not clicking URLs in strange email messages reduces your risk, but there’s still a remote chance you could make an innocent mistake and end up at a malicious Web site.
Since this is a network-based attack, another security option is to block connections using a firewall. Ideally we could do this using the application firewall in Leopard, but that only lets us block inbound connections, and this attack uses an outbound connection. The next best option is to configure the ipfw firewall built into all versions of Mac OS X to block outbound access for TCP port 554 and UDP ports 6970-6999. You can do this manually or using a tool like WaterRoof. (For more on the firewall in Mac OS X 10.5 see my article, “Leopard Firewall Takes One Step Forward, Three Steps Back,” 2007-11-05, and Chris Pepper’s “What’s a Firewall, and Why Should You Care?” 1999-02-22.) QuickTime will still work fine for your local media files, and the firewall stops you from accessing only streaming media.
Unfortunately, it’s still possible for an attacker to trick QuickTime into using a non-standard port, so this is only a partial defense. Another option is to use a third-party application firewall like Objective Development’s Little Snitch 2. Just configure it to block connections from QuickTime, which is one of the default applications already protected by Little Snitch. There’s a free 30-day trial that you can use right away to protect your Macs (for 3 hours at a time), and it’s well worth the $24.95 price for non-stop protection.
This situation highlights why it’s so important for Apple to finish some of the security improvements they started implementing in Leopard (see “How Leopard Will Improve Your Security,” 2007-10-22). Both library randomization and sandboxing can help prevent exploits of vulnerabilities like this. If Apple were to add outbound blocking to the application firewall, it would let us block these kinds of attacks without having to know anything about ports and protocols. Apple is clearly on the right path, and I look forward to future updates that will keep me protected even when a new, unpatched vulnerability is in the wild.
Until then, you need to keep your eyes open for a patch (which I expect we’ll see very soon), and hone your safe computing habits.
Hidden Network Information in Leopard AirPort Menu
Leopard includes more information than meets the eye about nearby Wi-Fi networks. Mac OS X 10.5 updates the AirPort menu in the system menu bar after you select a network, which is a neat feature and provides more accurate results. It also shows a lock icon next to networks protected by some form of encryption. But you can extract even more information by holding down the Option key while dropping the menu.
In Mac OS X 10.4 Tiger, holding down the Option key would sort networks by signal strength. That feature no longer works – networks are always sorted alphabetically (except for the network you’re currently connected to, which appears at the top). Instead, Leopard reveals connection information about whatever network you’re connected to, showing four details: the MAC (Media Access Control) address of the base station’s AirPort interface; the channel used; the receive signal strength indication (RSSI), a measure of how much energy is hitting your antenna from the base station; and the current transmission rate.
The MAC address is useful because it can tell you which base station you’re attached to if you’re using a network that uses multiple identically named base stations to provide seamless roaming across a large home or office. The channel information helps if you’re trying to figure out an interference problem with another network.
RSSI can be useful if you’re trying to tune the location of a base station and computer in relation to each other. Finally, the transmission rate lets you know if you’re getting optimum performance. Wi-Fi has drop-down speeds that are used when the highest possible rate shared between the base station and an adapter can’t be achieved; the two devices keep dropping down to slower and slower rates until an accommodation can be made. With 802.11b, g, or n, if the base station is in its default mode, that could be as slow as 1 Mbps – which is fine if you really need a connection, but not so great if you need the speed.
Astute TidBITS reader Gary Smith wrote in after I originally posted this item to note that you can also obtain information about other available networks through a tooltip that appears when you hover over a network for a moment (this assumes you Option-clicked the AirPort menu to begin with). The tooltip tells you the security method and RSSI, both of which could be useful when choosing a network to access.
Mac Developers Launch Two Software Discount Promotions
We at TidBITS are big fans of independent software developers. While larger firms produce massive, monolithic products that we use regularly in our working lives, smaller companies create gems that fill in the gaps. Plus, the small staff size of most independent developers means that they tend to be more responsive to requests and sometimes crazily fast in releasing updates in response to feedback.
That’s why we’re pleased as punch that not one, but two separate groups of Mac software firms have launched discount promotions for the holiday season.
MacSanta — MacSanta returns from last year, when a few software developers launched a blanket 20-percent off discount on their products for a limited period, and then encouraged other firms to join. In the end, dozens of companies participated (see “MacSanta: You’d Better Not Pout,” 2006-12-18).
Coordinator Paul Kafasis of Rogue Amoeba explained how the MacSanta Web site works. For each day of the MacSanta promotion, starting 01-Dec-07 and running through 24-Dec-07, five different developers will offer a 20 percent discount off their normal pricing during that 24-hour period (Pacific Standard Time).
After the day on which they’re featured on the MacSanta home page, all products will be offered at a 10-percent discount, through 31-Dec-07. The site has an RSS feed to which you can subscribe in order to receive updates as they appear. (Disclaimer: Take Control Books is participating in the MacSanta promotion.)
Feed Your Mac Habit — New this year is the hilariously named Give Good Food to Your Mac site, featuring 28 products from European Macintosh developers. I heard about the promotion from MacRabbit, makers of my currently favorite program in the world, CSSEdit, and apparently one of the instigators of the promotion. Other participating companies include Aquafadas, Belight, Boinx, Cheetah3D, Coladia, Creaceed, Equinux, Iospirit, Jumsoft, Kletel, Objective Decision, Ovolab, Pixelmator, ProjectWizards, Realmac Software, Reinvented Software, and Softpress.
Give Good Food to Your Mac offers discounts based on the number of applications you buy together: buy 3 programs from their list and get 30 percent off. Buy 5 programs and save 40 percent; buy 7, save 50 percent; and if you buy 10 or more, you’ll save a whopping 70 percent. The promotion ends on 08-Dec-07.
Display TidBITS Headlines on Your Site
While taking a break from writing about iPhoto 7 the other day, I ran across the Widgetbox site, which helps people create and share widgets, mini applications that display headlines, show photos, run countdown timers, and more. The point of widgets is that they’re easy to add to blogs and other Web sites to make pages more useful, more timely, more interesting, or just more fun.
So I created a TidBITS headline widget that pulls the latest headlines from our RSS feed and lets users click headlines to read the associated article on our site. The widget is somewhat configurable, so anyone who installs it can pick a wide or narrow view, a color scheme, and whether it displays just headlines or headlines plus a snippet from the top of each article. Take a look at it in the context of our Web site, where I was able to install it by merely creating a page with a tiny piece of JavaScript code provided by Widgetbox. As you can see at Peter Cohen’s Tikkabik blog, it can have rather
different looks based on user-specified settings.
What’s particularly neat is that at the bottom of the widget is a Get Widget button that, when clicked, makes it easy for any reader to get the JavaScript code or add the widget to blogs hosted in TypePad and Blogger, Facebook and MySpace profiles, and other services like Netvibes, Pageflakes, iGoogle, and Google Reader. One tip: if you want to change the look of the widget, click the Customize Widget link and do so before
adding it to a blog, profile or Web page.
Give it a try, and if you install it, let me know the link to your site so I can check it out and see what else you’re doing there. The more people who install it, the more people will read TidBITS and the closer we’ll be to world peace. Or something like that. And if you like the TidBITS headline widget, Widgetbox has 25,000 more free widgets you can try.
Listen to Music Online with PandoraBoy
Thanksgiving is past, and December is here, which means that my month-long window for listening to Christmas music is upon me. We have a decent selection of Christmas music ripped to iTunes from our CD collection, but unlike my normal listening habits, where I want to pick the artists quite carefully, Christmas music is all about the genre for me, and I like hearing new takes on favorite songs from artists I’ve never heard before.
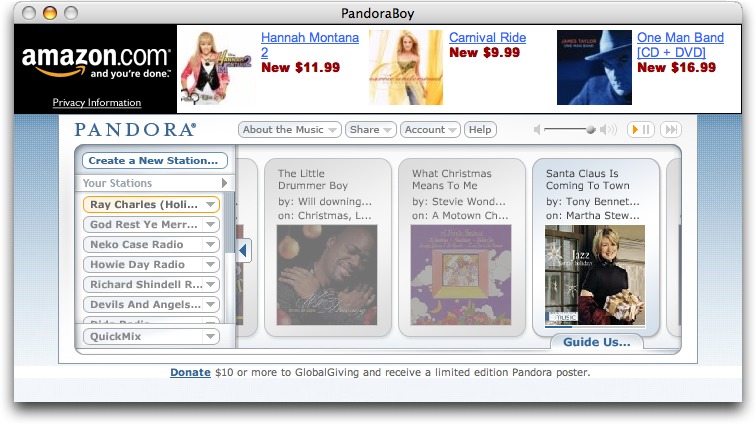
The online music service Pandora is great for that. By merely telling it what you like and don’t like, it plays a variety of songs from its broad selection of holiday music (see “Pandora Beats iTunes for Holiday Music,” 2005-10-05). But as much as I like the idea of Pandora, the fact that it runs in a Web browser bugs the heck out of me. It’s too easy to lose track of the tab Pandora’s using, and if I minimize it to a small window, clicks that open URLs from other applications often end up using that small window if I forget to switch back to a normal browser window after using Pandora’s controls.
A clever little application called PandoraBoy fixes all that. It uses WebKit to display the Pandora player in its own window, but goes beyond that to provide global hotkey shortcuts for rating songs, skipping to the next song, and adjusting volume. It also supports the Apple Remote, provides AppleScript support, updates itself via Sparkle (see “Sparkle Improves Application Update Experience,” 2007-08-20), and uses Growl to notify you when a new song starts playing.
Future plans for PandoraBoy include integration with the iTunes Store (to make it easy to purchase tracks you’ve heard), logging of played tracks, and support for the Last.fm online music service. For now, though, the free PandoraBoy 0.4.2 is a 757K download and works with Mac OS X 10.4 or later.
Stop the Catalog Madness with Catalog Choice
Discussing ways of lightening your mailbox’s load of paper catalogs in TidBITS may seem a bit unusual, but remember that one of the reasons Tonya and I started TidBITS back in 1990 was to provide an online alternative to weekly technology magazines like MacWEEK. Many of those magazines have disappeared in favor of publishing news online, and although most retailers now sell online too, the onslaught of paper catalogs, particularly around the holiday season (now starting in September!) seems to have increased. Don’t believe me? There are now 19 billion paper catalogs mailed to U.S. consumers annually, consuming over 8 million tons of paper each year.
We’ve long tried to reduce our catalog load by calling catalog companies and asking to be removed, faxing the back page of the catalog with the mailing label on it to the company with a request to be removed, and using the Direct Marketing Association’s Mail Preference Service (which apparently now costs $1). I’m sure it has helped, but the holiday catalog flood is starting anew.
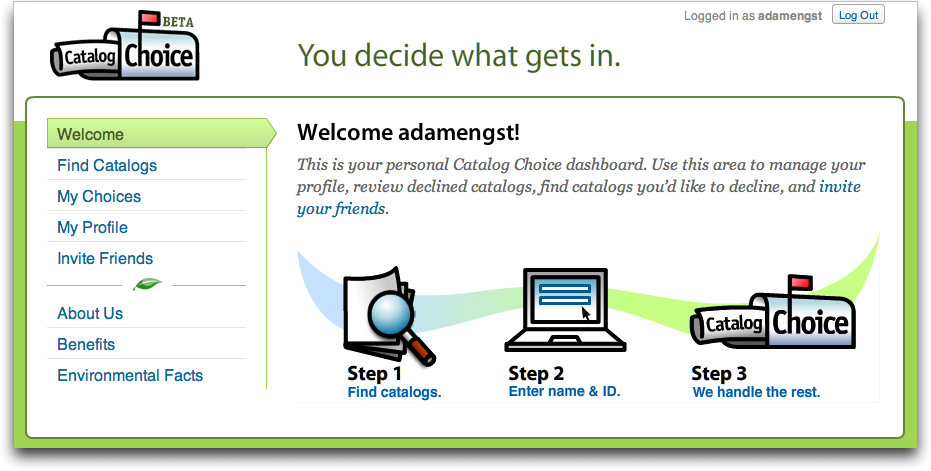
Thanks to long-time TidBITS reader Matt Henderson of MakaluMedia for alerting me to a new service his company has launched in conjunction with the Ecology Center. Called Catalog Choice, it’s an extremely slick Web site that automates the process of asking merchants to remove us from their catalog mailing lists. It’s entirely free, and although it remains to be seen how effective it is (it can take up to six weeks to be removed), I rather enjoyed finding catalogs and asking to be removed in the Catalog Choice system. If nothing else, it felt like I was doing something productive.
So far, Catalog Choice has proven quite popular, with over 250,000 people opting out of more than 3 million individual catalogs. And we’ve quite enjoyed using it – after school, Tonya and Tristan sit down with the daily haul and opt out of nearly every catalog we receive – 57 so far. We even do this with catalogs from companies we like because Catalog Choice records which catalogs have been declined and includes links to the associated Web sites, making it easy to order in the future.
Don’t get me wrong – I’m not opposed to the concept of paper catalogs in general. In fact, I often find them more effective at conveying information and more enjoyable to browse than online catalogs. But I want to be in control of which catalogs I receive, and I absolutely hate receiving new catalogs from the same companies every few weeks. For instance, until we managed to beat them off, Victoria’s Secret seemed to think we were members of the Lingerie of the Week Club. One or two catalogs a year would be more than sufficient, thank you very much, and if I like them, I’ll keep them around until I get a new one. Of course, I’m old enough to remember the yearly Sears, Montgomery Ward, and JCPenney catalogs that provided hours of youthful
consumer lustfulness and that were heavy enough to be duct-taped into boat anchors.
But in this day and age, I just want most catalog companies to leave me alone. If Catalog Choice can do that, reduce the environmental impact of catalogs, and even save the merchants from wasting catalogs on me, we all win.
Webjimbo 2 Eases Network Setup, Adds iPhone Interface
Webjimbo, a third-party interface to password and miscellany manager Yojimbo, has received a significant upgrade, now offering simple network configuration, a persistent remote access URL using NAT port mapping, and a specially tailored iPhone front end. Webjimbo 2 can now also edit stored passwords and encrypted notes. A list of new features appears on a Webjimbo mailing list.
Webjimbo uses Yojimbo’s extensive AppleScript interface to enable Web-based remote access to nearly everything you can stick in Bare Bones Software’s data manager. Encrypted PDFs and Web archives are the two exceptions. I use Yojimbo religiously for storing every password, sales record, and random bit of crud that I accumulate in daily life. It’s a decent solution to the problem expressed in David Weinberger’s excellent book “Everything Is Miscellaneous.” (We reviewed Yojimbo 1.0 in “Let Yojimbo Guard Your Information Castle,” 2006-01-30; it’s now at version 1.4.2.)
Like the previous version of Webjimbo, the new release uses a secure SSL/TLS Web connection with a self-signed certificate that enables you to access confidential information and passwords without worrying about sniffers. (Self-signed certificates produce a warning in browsers, including Safari on the iPhone, that the certificate can’t be independently confirmed. You can permanently accept such a certificate in most browsers; Safari for iPhone makes you click Ignore once per session.)
Webjimbo also now offers automated router configuration to make computers without publicly routable IP addresses reachable through a directory that the developer has enabled; you can also configure a router manually. Like Back to My Mac in Leopard, you need to have a router that supports the Apple-developed NAT-PMP protocol (all AirPort Extreme and AirPort Express models), or the more widely found UPnP.
By registering the software with the Webjimbo directory, you can remotely access your system through http://findme.webjimbo.com/yourname, replacing yourname with the account you set up.
While there are a few other iPhone-based password managers that use cleverly tailored bookmarks to store password information (a technique pioneered by Selznick Scientific Software’s Password Wallet for iPhone), Webjimbo links directly and in real time to a more versatile information store. Webjimbo’s iPhone interface is well designed to take advantage of limited screen real estate, limited download speed (when not on a Wi-Fi network), and the special limitations of the iPhone (no downloaded attachment). You can also view unencrypted PDFs, which is a nice plus.
Punching a Hole for Back to My Mac
[Editor’s note: Since this article was published, Glenn Fleishman has written two interrelated books about Back to My Mac use and troubleshooting, and Screen Sharing in Leopard. The ebooks are $10 each and $15 for both of them. You can read excerpts and purchase the books for immediate download.]
If you’re a Mac OS X 10.5 Leopard user dying to use the new screen- and file-sharing service called Back to My Mac, Apple has released some new information that’s helped me get the service to work and may help you too. In brief, Back to My Mac requires a full .Mac account and connects through secure tunnels all the computers on which you have both entered your .Mac account information and turned on Back to My Mac in the .Mac preference pane. (You can read a full rundown of the service in an article I wrote for Macworld.)
Back to Which Mac? I had difficulties getting Back to My Mac to function correctly. It first worked between two of my computers set up with Leopard; one computer was at home, the other at my office. The home computer could access the screen and files of my work machine, but not vice versa. I knew that a firewall might be in the way because of a Qwest-supplied DSL router that was problematic to configure. Back to My Mac requires either NAT-PMP (Network Address Translation Port Mapping Protocol) or UPnP (Universal Plug and Play) to open a static incoming port via which remote computers can connect.
(The router crashed whenever I attempted to connect it via its Web interface, but I discovered that if I used a URL path (like /home.html), and not just the IP address of the router, I was able to configure it successfully. This is apparently a bug in the 2Wire DSL router that manifests itself for Mac users, but not apparently for other users.)
After a few days of using Leopard, I was unable to get Back to My Mac to work at all. Fellow TidBITS editor Jeff Carlson had the same experience. When 10.5.1 was released, my home machine could once again see my work machine but not vice versa. Jeff and I did some testing, and found strange problems. When we used the same .Mac account details at one of his computers and two of mine, one machine would show the other two computers in the Back to My Mac set, one would show none, and another would show just one. We were stymied.
However, after overcoming my Qwest DSL router problems, I was able to test information provided in a Knowledge Base article about Back to My Mac security. Apple notes that the service uses UDP over port 4500 and TCP over port 443. While I had already known that, I hadn’t tried to set up my DSL router’s firewall. (Apple also links from this note to a page I’d forgotten that describes all the ports its operating systems use for common and Apple-specific services. This is very helpful when configuring a firewall.)
Turning on Incoming Access for Two Ports — Because the router crashed when I was configuring it, I had disabled its Wi-Fi capabilities and attached an AirPort Express Base Station to an Ethernet port on the router. NAT-PMP was turned on for the AirPort Express, but that apparently didn’t enable the right kind of punch-through for Back to My Mac via the router.
I determined that the Qwest DSL router lacked UPnP, which is a shame, but it had some very fine-grained controls for enabling incoming access to specific services by name for computers on the local network. (It seems to pick up the Samba sharing name of those computers to identify them by IP address, even when the address changes; or I could assign a static private address, too. It’s a little complicated, but well implemented and explained in the router Web interface.)
I turned on incoming access for the two ports mentioned in the Apple tech note, and now Back to My Mac works as expected. If you’re in the same boat, it’s worth digging out the manual or calling technical support to figure out how to enter the port information you need to allow incoming access. Some devices don’t offer the level of control that my 2Wire DSL router has, and you would have to either open incoming access for all computers on given ports, or map those ports from the outside world to a particular computer on your privately addressed network.
Apple’s Lacunae in Security for Back to My Mac Documented — It’s worth mentioning that the Knowledge Base article I mention earlier explains briefly many of the security concerns that I mentioned in my Macworld article. Notably, Apple points out that Back to My Mac’s linchpin is your .Mac password. While the password is protected when you log into .Mac and Back to My Mac uses strongly encrypted tunnels, the password itself is the only key needed to enable this feature. Thus, if you have a weak password or if it can be easily guessed, other people could gain access to any Back to My Mac-enabled system, too. Picking a strong password provides a greater defense against a password being compromised through
guessing or social engineering.
Apple suggests that you use the screen locking feature that’s available with the Leopard screen saver; that you use Keychain Access to enable a menu item that lets you manually lock the screen; that you disable automatic login for any user account with Leopard that has a .Mac account pre-filled in the .Mac preference pane; and that you consider the physical security of any Mac for which you’ve entered .Mac password information.
All of this is laughable, because Apple could have provided a simple assistant and/or a checkbox for Back to My Mac that would have guided you through picking a stronger .Mac password and turning on the various features it mentions. It’s not rocket science.
Apple’s note amounts to a statement like this: “Back to My Mac is very secure between locations and doesn’t disclose any private information; but the endpoints are very weak and we didn’t provide any help to you to make the endpoints stronger automatically.”
It’s a big admission, couched as advice.
Do you have experiences with Back to My Mac, for better or for worse? I’d like to hear them. If you can’t get it to work, I’d like to offer some advice. Contact me at [email protected]. I’m working on a book on the subject of remote access, and learning more about Back to My Mac problems will help me better help others in the book.
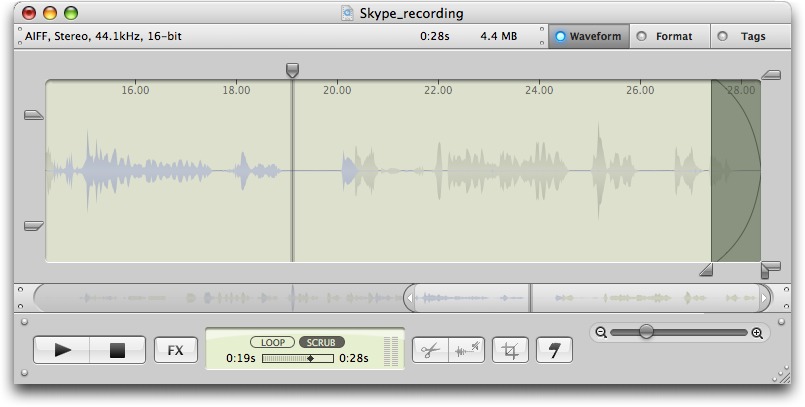
WireTap Studio: Lossless Editing and Real-Time Audio Preview
Ambrosia Software’s new WireTap Studio is an impressive collection of tools for recording and editing audio on your Mac. WireTap Studio manages the entire process of selecting your audio source(s), post-processing the recording, and exporting the finished product in the format of your choosing. What’s most interesting is that, like edits made to photographs in iPhoto 7, all edits made to an audio file are completely non-destructive, and are essentially applied on top of the file. You can even selectively remove specific changes, such as removing a particular filter or a specific cut in the audio.
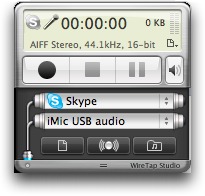
Basic Recording — Recording is managed by a small controller window in which you select one or two audio sources (Skype, iChat, iTunes, built-in microphone, etc.), a format in which to record (MP3, AAC, AIFF, Apple Lossless, etc.), and any effects you want to apply (reverb, hiss removal, hum removal, etc.) After choosing settings, you click Record, and that’s all there is to it.
You can optionally play back a live preview of your recording through your speakers or headphones as you record, a useful feature for checking that your settings are giving you what you want. Unfortunately, it performed poorly when doing a live voice capture (such as when creating a podcast), since the lag between saying something and hearing it played back was around 4 seconds on my 1.25 GHz PowerBook G4, which is, admittedly, near the bottom of the recommended hardware. It is virtually impossible to speak coherently while hearing your words played back on a time delay.
You can set WireTap Studio to split the resulting files based on size (to keep audio files no larger than 200 MB each, for instance) or on silence (to create a new file after 2 seconds of silence, for example). This latter feature came in quite handy when I recorded a mix tape my sister made in 1981 so that each song on the tape was split into its own track, enabling me to work with each song individually.
Being able to record multiple sources comes in handy while recording something like a Skype call. The first input is Skype itself, capturing everything the remote caller says. The other input is the microphone that’s recording everything you say. Together, they capture both sides of the conversation.
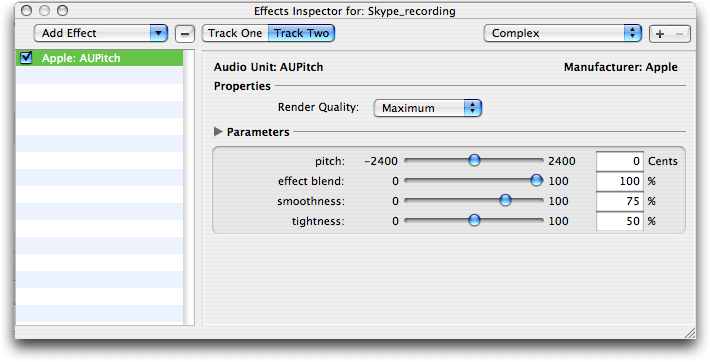
You can apply filters to the audio as it is being recorded or afterwards when editing the recordings. Previously, I always did my filtering after the recording was finished, largely due to the limitations of my computer. But since WireTap Studio applies filters in a non-destructive manner, there’s no performance hit (unless I am doing a live preview), which provides welcome flexibility.
Editing the Sound — WireTap Studio’s audio editor is simply gorgeous. You can perform all of the basic transformations you can make in most other audio editing tools but, unlike other tools, these transformations may be edited or even removed afterwards. Say you recorded a Skype conversation for a podcast, and you want to edit out a side comment your guest made to trim the interview. Select the audio in question and hit the Delete key. WireTap Studio automatically removes the offending clip and provides a smooth fade out and back in again to make the transition cleaner than a straight cut might be. You can adjust both the type of fade and its duration. Better still, you can undo the entire thing and restore
the cut audio even long after performing other edits.
This non-destructive editing and processing applies throughout. Even if you change the format of the audio – perhaps reducing it from CD-quality to a low quality MP3 – you can always return it to its original format, restoring all the original fidelity to the recording. The same thing applies to audio effects. If you punch up the audio, perhaps by adding a little reverb to provide some depth and increasing the bass slightly, you can always change your mind later, tweaking your settings or removing the effects entirely.
What’s most impressive about this is that you can apply all of these format changes and effects while listening to a live preview, so you can hear, in real time, what your changes sound like. If you have done even a minimal amount of audio editing, you’ll appreciate what a time saver this is and, honestly, how much fun it is.
WireTap Studio’s editing flexibility extends to the level of individual sources. When you record from two sources, they’re displayed in two colors in the editing window: gray for one, blue for the other. You can apply filters to each source individually and adjust their relative volumes. You cannot, however, edit the specific waveforms of one source without affecting the other, nor can you join two different sound files into one multi-channel file.
The main downside to this non-destructive editing is that WireTap Studio keeps ultra-high quality audio files lying around at all times, essentially requiring you to have a large hard drive. If you are absolutely certain you won’t need to revert to the version before your current edits, you can remove that original version to save hard disk space.
Timed Recording — WireTap Studio has the capability to do timed recordings. You can tell it to begin recording immediately, for a set number of minutes, or you can set it to start recording at a given time for a certain length of time. I was able to set up a recording of a radio stream via Windows Media Player for a specific date and it recorded without a hitch. But I had to know the URL and the date and time, so it lacks the simplicity of Rogue Amoeba’s RadioShift (for a full review, see “Radioshift TiVos Internet Radio,” 2007-10-02).
Podcasting — Thanks to WireTap Studio’s capability to capture audio easily from any source, podcasters will find the program particularly useful. For example, you could record an interview via Skype, and then later record and edit your own voiceovers.
Once you had captured all of your source audio, you could bring everything into a multi-track editor, such as GarageBand, to sequence it together and create your master mix-down. This file could in turn be brought back into WireTap Studio for any final edits and to be exported in the correct file format. WireTap Studio’s capability to preview different format settings in real time would help you to find the perfect balance between file size and audio quality.
From WireTap Studio you could export it to iTunes or export to a file for uploading to your server. In short, WireTap Studio is an excellent and useful addition to any podcaster’s toolbox.
Comparing to Audio Hijack Pro and Fission — Those familiar with audio recording and editing programs may wonder how WireTap Studio compares with Rogue Amoeba’s popular Audio Hijack Pro (for recording; see “Rogue Amoeba Hijacks Phone Calls More Easily,” 2006-07-31) and Fission (for editing; see “Fission Manipulates Audio Tracks of All Stripes,” 2006-09-25). Neither of those programs, good as they are, has seen a significant update in some time, and I find WireTap Studio’s interface to be cleaner and more easily
navigated, particularly when it comes to recording audio from different sources. Plus, WireTap Studio’s capability to add and remove filters before and after recording is unique. On the flip side, Audio Hijack Pro beats WireTap Studio handily when it comes to providing an interface to metadata such as lyrics, track number, and so on. Overall though, WireTap Studio has caught up with and, in some cases, surpassed Rogue Amoeba’s tools for the moment, giving Rogue Amoeba incentive to come up with some innovative improvements of their own.
Closing — WireTap Studio is a beautifully designed, highly functional tool that is a joy to work with and that provides a wealth of powerful recording and editing tools. However, this power comes at a price – you need a sufficiently fast Mac and a lot of free disk space.
WireTap Studio costs $69, with upgrades from WireTap Pro priced at $30. You can use the program for 30 days for free without limitation; after 30 days, a voiceover is mixed into all recordings, although the editor and library continue to function normally. WireTap Studio requires Mac OS X 10.4 or later and QuickTime 7.0 or later, running on a 1 GHz PowerPC G4 or faster Mac, or any Intel-based Mac.
[Andy Affleck is the author of “Take Control of Podcasting on the Mac” and has been tinkering with audio tools since the days of Farallon’s MacRecorder on his Mac Plus.]
Take Control News: Make Easy and Safe Backups in Leopard
Leopard’s new Time Machine is great, but there’s more to a secure backup strategy than turning on Time Machine and hoping for the best. Plus, a lot of people are wondering how to integrate Time Machine into an overall Leopard backup strategy. The answers are now available in “Take Control of Easy Backups in Leopard,” by backup guru Joe Kissell.
Joe’s strategy for a complete Leopard backup system – including archiving, a bootable duplicate, and offsite backups – is designed to protect you from mishap while minimizing the amount of time you spend making backups. You’ll find thorough, step-by-step instructions for Time Machine, bolstered by helpful details that you won’t find in Apple’s documentation, but you’ll also learn about alternatives for seven cases where Time Machine won’t provide the backups you need. Most importantly, Joe explains clearly how to recover your precious data in case of a deleted or corrupted file, a dead hard drive, or a stolen laptop.
Because of the many questions we’ve received about Time Machine and backing up in Leopard, we’ve decided to release this ebook in preview form so you can take advantage of Joe’s research and advice right away. If you buy now, you will receive a three-page PDF. The first page contains the all-important red starburst, which you click to access the Web-based preview (you can also make comments and ask questions within the preview) and to access the final PDF ebook when we’re done with it. The second two pages are coupons for 50% off Data Backup (save $30) and 10% off on CrashPlan or CrashPlan Pro (save $2 or $6). We hope to release the PDF in December or January.
If you own (or purchase) the second edition of Joe’s best-selling “Take Control of Mac OS X Backups,” click Check for Updates on the cover to access “Take Control of Easy Backups in Leopard” for free. Owners of the first edition will find a discount on an upgrade to the second edition. We’re bundling the two like this because we updated “Take Control of Mac OS X Backups” in September 2007, and its next update – with coverage of Time Machine – is scheduled for 2008.
Bonus Stories for 03-Dec-07
Leopard Compatibility List Updated — Curious about what programs have been updated for Leopard? Look inside for a list of the important or interesting programs that specifically claim Leopard compatibility. (TidBITS Staff, 2007-12-02)
Powerless? iPhone Provides a Light — In a brief power outage, I discovered the joy of continuous Internet connectivity with my iPhone. I express outrage at the outage reporting, too. (Glenn Fleishman, 2007-11-10)
Google Used 70 Times More than Yahoo — Why is it that we get 70 times more referrals from Google than from Yahoo, considering that Google serves up only about 3 times as many searches? (Adam C. Engst, 2007-11-07)
iMovie ’08 Meets Wild Robot Cars — Back from the field filming the DARPA Urban Challenge, will I be able to perform a simple task using iMovie ’08 – to overlay some text onto an entire movie – without ever having used the program before, and without reading the manual? (Matt Neuburg, 2007-11-02)
Nisus Writer Pro Wrangles Word into HTML — Faced with the tedious task of converting styled source text from Word into HTML, Adam remembers that the proper tool for the job is Nisus Writer Pro, with its grep-based, attribute-sensitive Find and Replace capabilities. (Adam C. Engst, 2007-10-25)
My Real Breakfast with Fake Steve Jobs — Dear diary: I had breakfast with Fake Steve Jobs! He showed me the next-generation iPod (hint: it requires minor surgery to use), gave me a shiny new penny, and then wiped my memory using his reality distortion field. All I recall is eating a bagel with a Boston-based Forbes reporter named Dan Lyons. (Glenn Fleishman, 2007-10-24)
Hot Topics in TidBITS Talk/03-Dec-07
Google Analytics question — Why is Google Analytics reporting far fewer Web page visits to a reader’s site than the figures provided by his hosting company? (12 messages)
A Simple Hack To Fix Leopard’s Stacks — One method of making Stacks under Leopard more usable isn’t working for one reader, leading to suggestions from others. (5 messages)
Punching a Hole for Back to My Mac — Glenn’s article about making Back to My Mac work reliably brings up more questions about router firewalls and dynamic DNS. (5 messages)
Registrar for domains as good as easyDNS is for DNS? After finding success with easyDNS, a reader is hoping to get a recommendation for a domain name registrar that is as easy to work with. (6 messages)
Anyone used Automator? Apple’s scripting utility is one of the major additions to Mac OS X, but does anyone use it? And how well does the new recording function work under Leopard? (9 messages)
Leopard Firewall – ipfw script inherited in migration — Leopard’s obscure firewall leads to more confusion, this time over settings migrated from Tiger that are hampering network communication. (1 message)
Leopard firewall vs iChat over Bonjour — More information about Leopard’s firewall, this time reporting a reader’s discoveries about how it operates via Bonjour networking. (1 message)
2007 Holiday Gift Ideas: Hardware — What computer hardware do people want to give or receive for the holidays? (21 messages)
2007 Holiday Gift Ideas: Software — What software do people want to give or receive for the holidays? (15 messages)
2007 Holiday Gift Ideas: Games — Do. You. Want. To. Play. A. Game? Be nice to Joshua and discuss your favorite games of the year. (7 messages)
2007 Holiday Gift Ideas: Computer Miscellaneous — This thread covers the computer-related gift ideas that don’t fit into the other categories. (13 messages)
2007 Holiday Gift Ideas: For the Macintosh-minded — It’s not all about the computer – just look at the Baker’s Edge Brownie Pan! (12 messages)
802.11n over Ethernet? A reader wants to relay wireless networking signals through his Ethernet port, and there’s an adapter out there that may be able to do it. (2 messages)
Transparent Menu Bar — What’s your opinion of Leopard’s transparent menu bar? Most of the Mac press hates it, but many readers either like it or don’t mind. (13 messages)
Writing Terminal commands — The syntax of representing what to write for a terminal command can be confusing if you’re new to working within the Terminal. (7 messages)
Parallel Printer Connection Suggestions — Simple adapters (and the right drivers) can keep an old printer in working order, even if it offers only a parallel connector. (7 messages)
Hands on with Kindle — Glenn’s experiences with the Amazon Kindle ebook reader prompt comments about readers in general, and comparisons to Sony’s offering. (34 messages)
Word Completion Feature in Mail.app and TextEdit — Pressing Esc when typing in Mail or TextEdit under Leopard brings up a list of similar words to choose from. Do other applications support this little-known feature? (12 messages)
Reunion — Readers comment on the features of this genealogy application, and how well it works for information that isn’t specific to the United States. (9 messages)
Tab, Delete & Return keys just beep in Tiger text boxes — A reader tries to identify a problem, leading to a discussion of input managers under Tiger and Leopard. (7 messages)
Software adapted for using Mac Pro 4/8 cores? When looking for a list of applications that take full advantage of multi-core processors, the important answer is Leopard, which provides such support to all multi-threaded applications. (3 messages)
Eudora Error message – help? Ah, the day arrives for a young reader when one of his Eudora mailboxes fills up, which of course sends the program into spasms of obscurity. (4 messages)
Printing from Personal RecordKeeper for OS X — Even though old data can be read under Mac OS X running Classic, a reader can’t get it to print. The tedium of creating PDFs and printing from another source is sometimes the best you can expect. (4 messages)
syslogd, mdworker and mds … oh My! These system processes can generate quite a bit of work for the processor, which also brings up the issue of processes that you thought were uninstalled but still run. (13 messages)
Spotlight and Google Desktop problems — Why aren’t these two search solutions finding a file in a reader’s home directory? (11 messages)
MacBook Pro AC Adapter – Surge Protector — What capabilities does the power adapter for a MacBook Pro have? Also, we discuss the pros and cons of using a 65W adapter to power a laptop that normally uses an 85W adapter. (8 messages)
iPod software v1.2.3: readme? Apple characteristically is quiet on the changes in a recent iPod software update, but it’s clear that new signature features found in later models are unlikely to show up in these types of incremental updates. (2 messages)
France iPhone conditions — The pricing structure of the iPod and its associated wireless plans is finally made available, leading to the now-inevitable redefining of the term “unlimited.” (4 messages)
Quay Sticks It to Stacks — A reader agrees with Matt Neuburg’s opinion of Quay, which restores hierarchical menus to folders on the Dock. (3 messages)
What to do when the software company vanishes… SoftChaos has departed — What do you do when a company disappears? (And can we choose which companies disappear?) (3 messages)
Pandora and Apple TV — Is there any way to get the Pandora service on an Apple TV, and what’s happened to the Apple TV anyway? (10 messages)
Accessing email and files on Windows 2003/2000 and Exchange servers — A reader can no longer access email and files remotely from his Mac, but more information is needed to determine the cause of the problem. (3 messages)
Protect Yourself from the QuickTime RTSP Vulnerability — Will the rise of Intel-based Macs make it harder for malicious software writers to craft buffer overflow exploits? (1 message)
Bonjour not working after 10.4.11 update — Has Bonjour network discovery gotten fickle with the recent operating system updates? (2 messages)
Guitar to Mac connection recommendations — Some lucky kid is getting a guitar and an amp for Christmas (hope he’s not reading that thread, Dad!), so what’s a good way to connect the guitar to the Mac? (5 messages)
Hidden AirPort Information in Leopard Menu — Readers try out Glenn’s discoveries on the AirPort menu under Leopard. (6 messages)
iTunes 7.5 (19) has a bug — When playing a CD, iTunes apparently locks up. Anyone else seeing the same problem? (1 message)
What’s the deal with Palm? Hasn’t that been the question for the last 4 or 5 years? Sigh. (1 message)