#1610: Avoid hacked email scams, disable a known AirTag’s alerts, battery technology tricks, industry support for passwordless login
Could passwords finally be on the way out? Apple, Google, and Microsoft have taken another step in that direction by promising expanded support for the FIDO Alliance’s passwordless login technology over the course of the coming year. Do you ever get AirTag tracking alerts when you borrow your spouse’s keys? Josh Centers shows you how you can disable them—at least for a day, despite Apple’s claim that it’s possible to do so indefinitely. Josh also explains how Apple uses two technologies—fast charge and Optimized Battery Charging—to improve battery life and lifespan. Finally, Adam Engst shares how he helped an acquaintance whose email account was hacked to spread a scam—read on to learn how to respond if you’re targeted. Notable Mac app releases this week include 1Password 8.0, Firefox 100, Hazel 5.1.2, Camo Studio 1.6.4, TextExpander 7.2, and Moneydance 2022.3.
Another Step Toward a Password-Free Future
Put bluntly, passwords suck. We just published a lengthy article about an email scam that exists only because too many people have weak passwords that they reuse across multiple sites (see “How to Help a Friend Whose Email Has Been Hacked to Send Scams,” 5 May 2022). Why don’t we instead get to use sophisticated biometric authentication like Touch ID and Face ID more broadly? That may happen in the coming year, thanks to Apple, Google, and Microsoft committing to support the FIDO standard for passwordless logins.
To an extent, all three companies already support FIDO Alliance standards to enable passwordless logins, but this announcement expands those capabilities by providing automatic access to FIDO passkeys on multiple devices without having to re-enroll every account and by allowing FIDO authentication on a mobile device to sign in to an app or website on another device nearby, regardless of the operating system or Web browser in use.
Last year at Six Colors, Dan Moren wrote about Apple’s Passkeys system, introduced as a technology preview at WWDC 2021. It gives a glimpse of how Apple thinks this new passwordless authentication approach will work. In short, when you sign up for an Internet account, you would create only a username; Passkeys would create the passkey and store it in your keychain. All the Internet service would have is your username and your public key. When you want to sign in later, all Passkeys would have to do is prove that your device has the corresponding private key, which it would do by asking you to authenticate via Touch ID or Face ID. That would raise questions about how users would deal with the loss of a device and seemingly eliminate the possibility of signing in using someone else’s device, but those are implementation details.
With luck, we’ll start to see Passkeys (or whatever Apple ends up calling it) implemented for real in the upcoming releases of macOS 13, iOS 16, iPadOS 16, and watchOS 9. As the press release says:
These new capabilities are expected to become available across Apple, Google, and Microsoft platforms over the course of the coming year.
It can’t happen soon enough. Death to passwords!
TipBITS: How to Disable a Known AirTag’s Alerts
Apple wisely designed the Find My system so your iPhone alerts you if it determines that you’re traveling with an unknown AirTag. But unfortunately, you’re also alerted even if you’re knowingly traveling with an AirTag owned by a friend or relative. I regularly use my wife’s car, which means borrowing her keys, taking her attached AirTag with me, and getting AirTag alerts.
Apple hints at a way to disable these unwanted alerts…
It’s possible that the AirTag or Find My network accessory might be attached to an item you’re borrowing, or you might get this alert if you’re borrowing someone else’s AirPods. If you’re borrowing an AirTag or another item compatible with the Find My network from a member of your Family Sharing group, you can turn off alerts for that item for one day, or indefinitely.
…but doesn’t explicitly state how to disable them. So I took her car to run some errands to figure out how to do it.
What’s funny is I drove around for a couple of hours with my wife’s AirTag, but it didn’t trigger until I got home. So if she were stalking me, she could have easily tracked me to my house. Thankfully, we live in the same house.
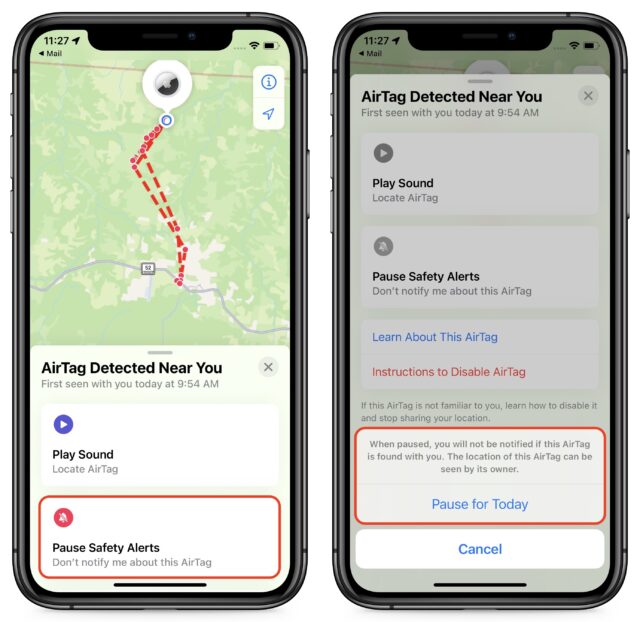
Once you get the “AirTag Found Moving With You” alert, tap the notification to see the AirTag in the Find My app, and then tap Pause Safety Alerts to stop receiving alerts for that particular AirTag.
Unfortunately, I was only presented with the option to pause the alerts for the rest of the day, not indefinitely. If you try this and are offered the option to pause them indefinitely, let us know so we can figure out what’s different.
How Apple Works Around Battery Chemistry Limits with Fast Charge and Optimized Battery Charging
The most significant limitation for mobile devices is power. Engineers keep finding ways to cram more transistors into chips, but batteries have hit a brick wall of physics, forcing hardware makers like Apple to invent creative workarounds for those limitations.
The inherent problem is that lithium-ion—the current battery chemistry of choice—isn’t particularly stable. It’s more forgiving than older technologies like nickel-cadmium, but it’s all too easy to shorten a lithium-ion battery’s lifespan by:
- Draining the battery completely
- Holding the battery at a 100% charge level
- Letting the battery get hot
Users have two conflicting desires with regard to batteries, whether or not they realize it. In the short term, they want the device always charged and ready to use—little is more frustrating than running out of power earlier than you’d expect in a day. Long-term, they want the battery to maintain its capacity for as long as possible—replacing a battery to bring a device back to decent daily battery life is expensive and annoying.
In an effort to meet both of these conflicting desires, Apple has developed two seemingly contradictory technologies: fast charge, which does what it says, and Optimized Battery Charging, which actually makes the battery charge more slowly.
Fast Charge
Certain Apple devices—most notably the iPhone 8 and later, USB-C iPad models, and 14-inch and 16-inch MacBook Pro models—support fast charge, which can boost the battery up to 50% in 30 minutes.
Fast charge requires a sufficiently powerful charger and appropriate cable—it does not work with wireless MagSafe and Qi chargers. For each of the device families, you need:
- iPhones: At least an 18-watt (20-watt for the iPhone 12) USB-C power adapter that supports USB Power Delivery (USB-PD), plus a USB-C to Lightning cable
- iPads: At least a 30-watt USB-C charger with a USB-C cable
- 14-inch MacBook Pro: At least a 96-watt power adapter plus a Thunderbolt, USB-C, or MagSafe 3 cable, or an external display with 94-watt power delivery via Thunderbolt 3 or USB-C
- 16-inch MacBook Pro: A 140-watt power adapter plus a USB-C to MagSafe 3 cable
Fast charge works by delivering more power to the device from the adapter. But with great power comes great responsibilityheat, leading some to believe that fast charge shortens your battery life. However, Marques Brownlee explains that fast charge doesn’t typically reduce your battery life by much, if at all, due to various techniques that reduce the amount of heat generated.
But fast charge only takes a battery to 50%. To get the rest of the way in a manner that doesn’t result in the battery sitting at 100% for a long time, Apple developed Optimized Battery Charging.
Optimized Battery Charging
Batteries don’t like being held at 100%, but users want their batteries to be at 100% when they start the day. How does Apple walk that line? Starting with iOS 13 and macOS 10.15.5 Catalina, Apple has provided features to reduce the maximum charge to extend the battery’s life. The first is Optimized Battery Charging.
Optimized Battery Charging uses machine learning to guess when and where you charge your devices the most and hold the battery’s charge at 80% until it thinks you need it to be at 100%.
On TidBITS Talk, David C. provided a great technical explanation of Optimized Battery Charging:
Apple’s optimized battery charging is a variation on this. It uses constant current charging until the battery’s charge reaches about 80%. Then instead of doing constant-voltage at a fixed voltage, it will dynamically select voltages so it will reach 100% shortly before it thinks you will remove the device from the charger. For example, if your usage history says you remove it from the charger at 8:00am every morning, it might try to reach 100% at 5:30am, even though a traditional constant-voltage charger might be able to bring it to 100% at 2:00am.
In theory, you should rarely notice this feature because it works while you’re asleep. In About Optimized Battery Charging on your iPhone, Apple says:
Your iPhone uses on-device machine learning to learn your daily charging routine so that Optimized Battery Charging activates only when your iPhone predicts it will be connected to a charger for an extended period of time. The algorithm aims to ensure that your iPhone is still fully charged when unplugged.
Optimized charging is designed to engage only in locations where you spend the most time, such as your home and place of work. The feature doesn’t engage when your usage habits are more variable, such as when you travel.
Optimized Battery Charging is location-specific, as you can tell by the fact that the following settings must be enabled for it to work on an iPhone:
- Settings > Privacy > Location Services > Location Services
- Settings > Privacy > Location Services > System Services > System Customization
- Settings > Privacy > Location Services > System Services > Significant Locations > Significant Locations
When Optimized Battery Charging is enabled on an iPhone, a notification appears on your screen. To bypass it and fully charge your battery, touch and hold the notification and tap Charge Now. You can also turn off Optimized Battery Charging in Settings > Battery > Battery Health, but that’s probably a bad idea unless you’re regularly starting the day with less than a full charge.
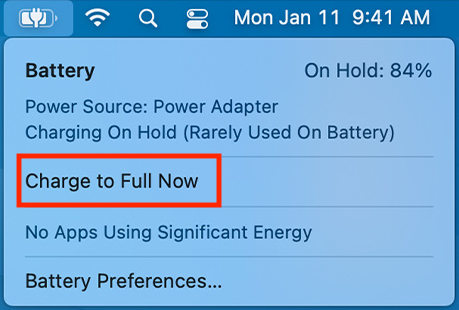
Optimized Battery Charging works slightly differently on Mac laptops, where it prevents a battery from being held at 100% for a long time if you regularly leave the laptop plugged in. When you click the battery icon in the menu bar, you may see Charging on Hold. You can then choose Charge to Full Now to override Optimized Battery Charging and charge the rest of the way.
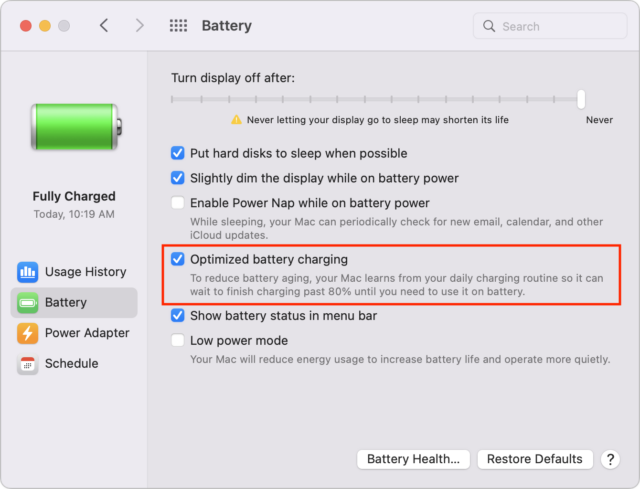
To turn off the feature, go to System Preferences > Battery > Battery and uncheck Optimized Battery Charging. You can disable it permanently or just for a day. Again, don’t do this unless you’re regularly butting heads with the feature.
As far as we can tell, iPads don’t support Optimized Battery Charging.
Battery Health Management
Beyond Optimized Battery Charging, iPhones and iPads have a charge management feature that temporarily reduces the battery’s maximum charge capacity when devices are constantly plugged into power. Apple says:
iPad with iOS 11.3 or later and iPhone XS, iPhone XS Max, or iPhone XR with iOS 12 or later include a charge management feature to help maintain battery health, which monitors these devices for use in these charging situations and, as required, reduces the maximum capacity of the battery. The battery indicator will display the charge percentage based on this adjusted maximum capacity. The maximum capacity will revert back to the nonadjusted level when iPad or iPhone is no longer connected to power for prolonged periods and as conditions and battery health allow.
On iPhones and iPads, this charge management feature is automatic, and you can’t turn it off.
Apple calls a similar feature on Macs “battery health management.” It works slightly differently on M1-based Macs and Intel-based Macs. On M1-based Macs, macOS will temporarily reduce your battery’s maximum charge capacity to extend the battery’s lifespan:
Battery health management is designed to improve your battery’s lifespan by reducing the rate at which it chemically ages. The feature does this by monitoring your battery’s temperature history and its charging patterns.
Based on the measurements that it collects, battery health management may temporarily reduce your battery’s maximum charge. This happens as needed to ensure that your battery charges to a level that’s optimized for your usage—reducing wear on the battery, and slowing its chemical aging.
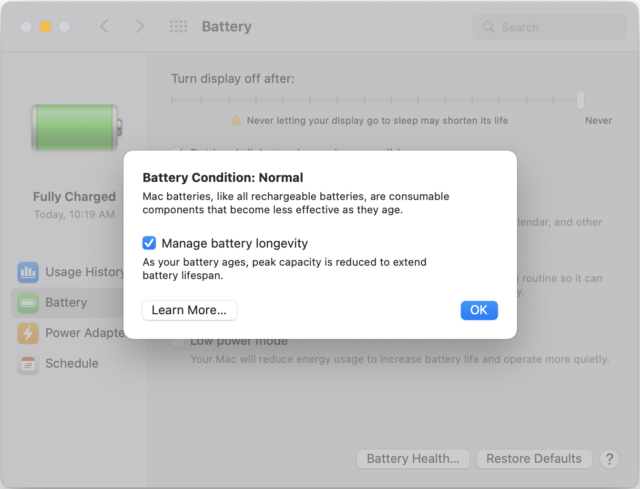
You cannot disable the feature on M1-based Macs, but you can on Intel-based Macs by going to System Preferences > Battery > Battery > Battery Health and unchecking Manage Battery Longevity. Again, we generally recommend against disabling it, but if it’s preventing you from charging to the level you need at a particular time, it might be worthwhile to turn it off.
In the end, as frustrating as it is that battery technology hasn’t evolved in step with the computational capabilities of our devices, it’s nice to see that Apple is using some of that processing power to make the most of what our batteries can do.
How to Help a Friend Whose Email Has Been Hacked to Send Scams
Beware of an email-based scam that’s making the rounds this year! Since January, I’ve been targeted three times, and I wanted to share the story—both to help you avoid falling prey to the scam and so you can better alert any friends or acquaintances whose email accounts have been hacked.
First, let me bang the drum one more time: None of these people would have had problems if their email passwords had been strong and unique. If you reuse your email password anywhere, or if it’s short and obvious, stop reading right now and go change it.
Your new email password can be at least 13 truly random characters (something like iR82dGlQf3&@C) or at least 28 characters of common words separated by hyphens (like the classic correct-battery-horse-staple), or you could generate it through some combination of numbers (like dates) and letters (such as initials) that make sense to you. Whatever you choose, it must be strong and unique. And if you’re not using a password manager, you’re wasting your time and likely being insecure.
How the Scam Progresses
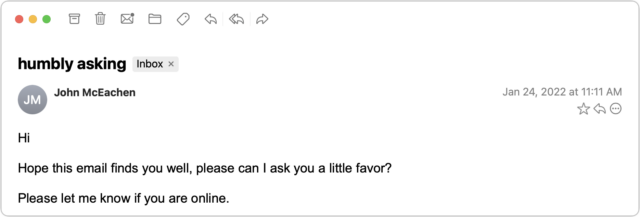
The email scam message I received came from someone I know quite tangentially—John is a runner from a nearby city who had participated in some of the track meets that I organize. Since I assign bib numbers and announce all the races, his name was sufficiently familiar that I wasn’t surprised to receive email from him—we had corresponded once in 2021 about an upcoming track meet. But with only one prior conversation, I had no sense of his email style, so his first message didn’t raise any alarm bells in my head.
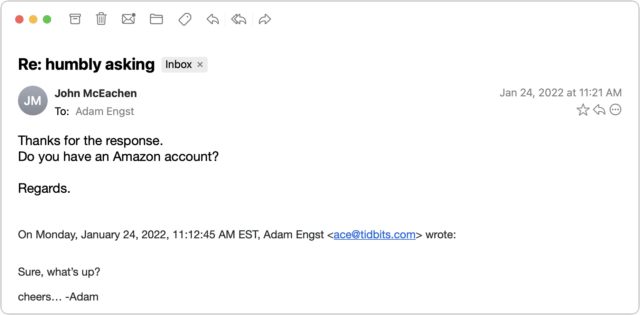
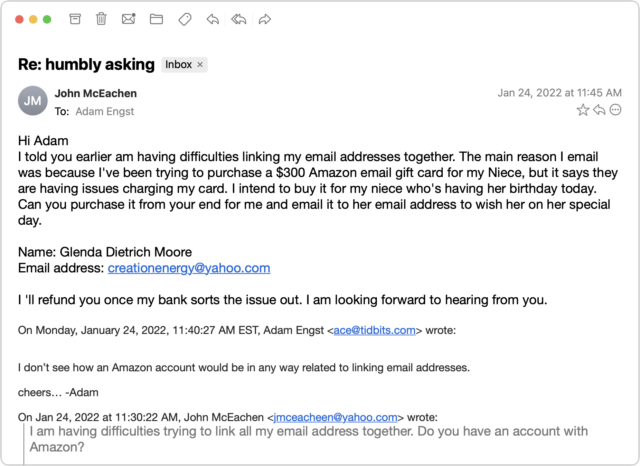
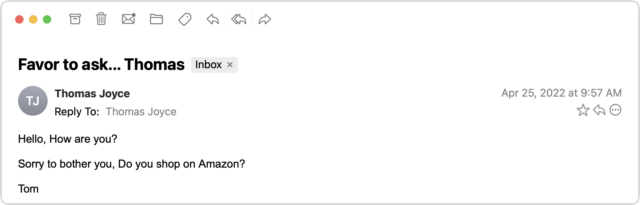
I replied generally to the first message—there were various reasons an upstate New York runner might contact me—but those alarm bells went off instantly upon receiving the next message.
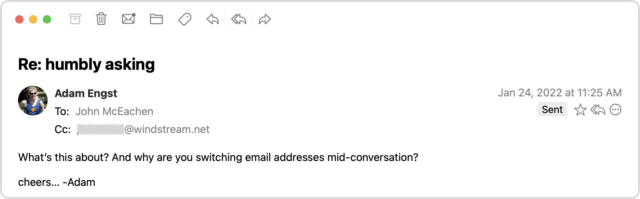
I couldn’t see any reason why a person I barely knew would ask if I had an Amazon account, and besides, at this point, who doesn’t? I switched into investigation mode. What you can’t tell from the message above is that although the sender’s name remained the same, the email address had changed from windstream.net to yahoo.com. Combined with the strange request about an Amazon account, I was now nearly certain I was talking to a scammer who was using the email address switch to get me into their own account in case John locked them out by changing his password. I decided to keep the scammer talking and see what I could learn.
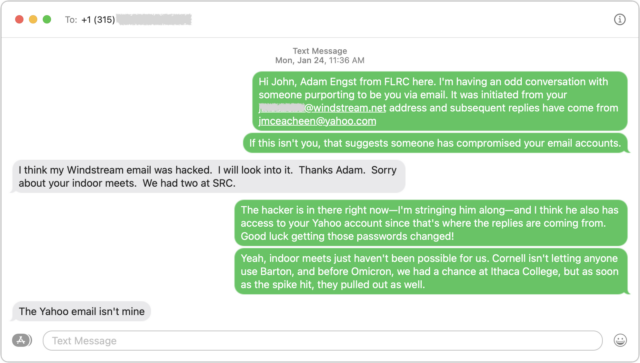
After sending that message, I looked up John’s phone number in his most recent track meet registration and texted him. Luckily, I was able to provide sufficient context in my initial text that he knew who I was. As I expected, he knew nothing about what was happening and confirmed that the Yahoo account wasn’t his.
By now, I was curious what the scam would be, so I kept pretending that I was skeptical but still going along with it all. After another message or two, it became clear—the scammer wanted me to buy a $300 Amazon gift card for which they would reimburse me later. Yeah, right.
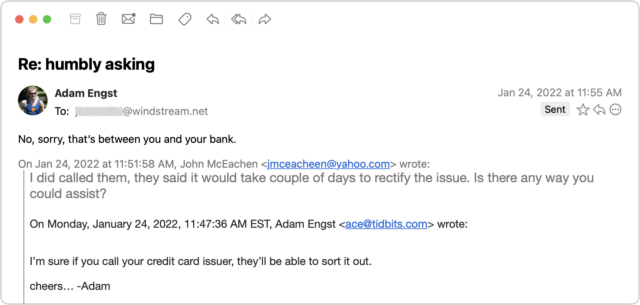
Throughout all this, I made sure to send only to the windstream.net account in part to see if the scammer would lose access. I was simultaneously keeping up the text backchannel with John, who said that he saw none of these messages in his Sent mailbox nor messages from me in his Inbox, which suggested that the scammer was somehow deleting them instantly to cover their tracks. I assume that John changed his password, but if so, that apparently didn’t kick the scammer out because I kept getting replies to the messages I sent to windstream.net.
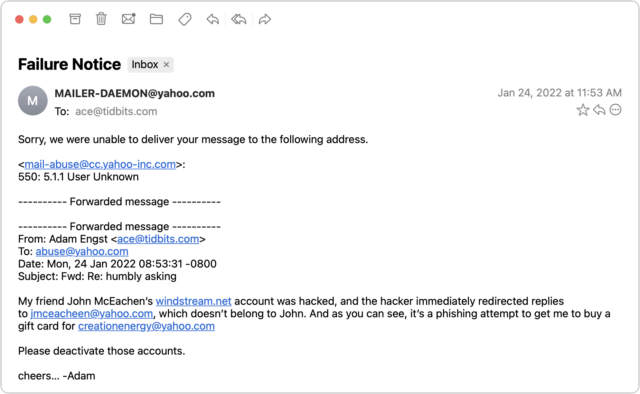
I entertained a faint hope that Yahoo would be interested in shutting down both the scammer’s address and the address they wanted me to use for the Amazon gift card. But no, my attempt to alert [email protected] failed. I subsequently tried to contact Yahoo via a recommended Web form after I mentioned the issue in “Yahoo-Backed POP Connections Cause TidBITS Formatting Error” (26 January 2022), but that was equally unsuccessful.
By this time, I had traded a few more messages with the scammer to keep the conversation going, but they eventually gave up on me. I never heard back again after this message.
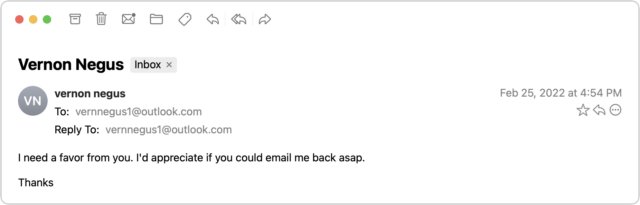
I didn’t get around to writing up this story right away and quickly forgot about it. But a month later, it happened again! Vern isn’t someone with whom I’ve ever exchanged email, but he runs an excellent U-Pick blueberry farm in my nearby hometown, and I had left my email address in his visitor book the last time I picked berries there. Luckily, I had an in for contacting him—my father used to be the mail carrier, and he still knows most people in town. Dad was able to call him and let him know about the problem, and Vern changed his password and alerted all his email contacts not to reply to the scam messages. Amusingly, this time, Vern’s real email address was at Yahoo, and the scammer was trying to redirect replies to a fake Outlook account.
Two months later, the scam reappeared in my email, with the scammer victimizing an older runner in the area. In this case, I’d been talking about Tom with another friend who worked with him regularly just the day before, so I recruited my friend to encourage Tom to change his password.
How to Help Your Friends
Let’s assume that you get one of these messages. They’re so weirdly generic that you’ll realize it’s a scam right away if they come from someone you know well. Or, as in the case of my second example, you’ll know the person so slightly that the scam will be obvious purely because a stranger would never ask such questions. The awkward middle occurs if the message is like my first and third examples, where I knew the people just well enough that I wasn’t surprised to get email from them but not well enough to be certain that the message was fake.
Nevertheless, if you’re unsure, there’s no harm in replying—just don’t get sucked in! If you notice that your reply (or any subsequent one) is going to an address other than where the first one originated, that’s another clue that you’re in the middle of a con. Once you realize what’s going on, here’s what I recommend doing… and not doing:
- Do recommend a password change: By calling, texting, or emailing a secondary address, tell the person whose account has been hacked to change their email account password immediately and recommend that they create a strong, unique password using a password manager. You must assume that the scammer has full control over the victim’s primary email account and will delete all warnings and evidence of wrongdoing.
- Do encourage alerting of other contacts: Although the person whose account was hacked probably won’t be able to tell who received the scam message, encourage them to alert all their contacts that the previous message was fake and should be ignored. Also, suggest that they encourage their contacts to check their passwords—might the acquaintances of people whose passwords were so weak as to be compromised be likely to have weak passwords as well?
- Don’t fall for the scam: Never buy an Amazon or other gift card for someone you don’t know just because they ask. (If you want to give someone money, become a TidBITS member.)
- Don’t mark it as spam: Don’t mark the initial message from the scammer as spam or report it as phishing. Remember, it’s essentially legitimate email, having been sent from the compromised account, so marking it as spam could cause future real messages from that person to be filtered too.
- Don’t bother reporting the scammer: Sadly, I don’t recommend trying to report the scammer to whatever email service they’re using. The goal is good, but it’s all too likely to be a waste of your time.
To make it easier to alert victims, here’s a sample message you can text them or use as a script when talking to them:
It looks like your email account has been hacked and used to send scam messages to contacts like me. I’d encourage you to change your email password immediately, making the new password strong and unique, ideally using a password manager app. Also, it would be good to alert your contacts to ignore the scam message and encourage them to make sure their own passwords are secure.
Finally, if you have friends who aren’t Internet-savvy, share these stories so they have a better chance of avoiding being scammed or having their accounts compromised.