#1462: TidBITS turns 29, more data breaches, Google Keep on watchOS, explaining the Mac’s T2 security chip
We’re celebrating our 29th anniversary this week in conjunction with Earth Day, so Adam calculates just how many trees would have been sacrificed if TidBITS had been a print magazine instead of purely digital. Data breaches keep making headlines—here’s how to check if your data was among the billions of records exposed so far this year. Have you ever wanted access to Apple’s Notes app on your Apple Watch? Embarrassingly, Google has beaten Apple to the punch by bringing Google Keep to Apple users’ wrists. If you have a recent MacBook Pro, a new MacBook Air or Mac mini, or an iMac Pro, your Mac has a T2 security chip. Geoff Duncan rejoins us with a deep dive that explains what that means for new Mac owners. It’s good, but not all good. Notable Mac app releases this week include Microsoft Office for Mac 16.24, Pixelmator Pro 1.3.3, Moneydance 2019.2, and Evernote 7.9.1.
TidBITS Marks Its 29th Anniversary… and Earth Day!
Last year’s TidBITS anniversary happened during the month-long crunch of replacing our entire Internet infrastructure, so we never publicly marked the date (see“Everything You Need to Know about the TidBITS 2018 Infrastructure,” 2 April 2018). That would have been our 28th anniversary, making this our 29th. The actual date ticked over last week on April 16th, but we decided to hold off briefly so this article could coincide with Earth Day.
Why? From very our first issue on 16 April 1990, TidBITS has been purely electronic. At the time, that was extremely unusual—all the professional publications in the technology world were paper magazines. These magazines—Macworld, MacUser, MacWEEK, and so on—were great, but they consumed an insane amount of paper.
That got me thinking. How much paper—and how many trees—has TidBITS avoided using by focusing our attention on digital distribution from the outset? Coming up with a number required a great deal of estimation, but it was fun, so I’ll share some of the thinking and silly asides.
How many characters appear on a magazine page?
The first problem was to determine how many characters fit on an average magazine page. Our friend Jason Snell told me that, back in the day, his one-page column in Macworld was 800–850 words, and a page was probably 900 words tops. Depending on the source you consult, there are around 6 characters per word on average, so that works out to between 4800 and 5600 characters per page. To check this, I pulled out an old Byte magazine, found a page that was entirely text, and counted the number of characters in a line (40), the number of lines in a column (65), and the number of columns per page (3). That’s 7800 characters for a full page of text, but with graphics occupying a third of the page, the numbers work out to 5148, which is in line with Jason’s estimate.
How many characters have we published in TidBITS?
A relatively simple SQL query revealed the answer, a highly precise 59,387,344. But that includes HTML tags, so I spot-checked a few representative articles and estimated that HTML accounts for about 25% of the total, leaving 44.5 million characters of real text. Shakespeare wrote only 884,421 words, or roughly 5.3 million characters. Of course, his plots and character development are better, and he made up over 1700 words, but I invented a word too—see “The iPhone and the Googlewhackblatt” (20 December 2007).
How many pages would the TidBITS archive occupy?
Dividing the number of characters by the character-per-page count tells us that, if the entire archive of TidBITS were printed out like a magazine, it would be 8652 pages. And yes, I realize there’s a lot of hand-waving around graphics. Go with it.
How many pages would we have sent to TidBITS subscribers?
8652 pages may seem like a lot of paper on first glance, but remember, we send TidBITS to tens of thousands of subscribers in email. That circulation number has varied widely over time—it started under 100, peaked at over 50,000, and is currently a little under 24,000. For simplicity’s sake, let’s say that it has averaged 25,000. Suddenly, we’re up to 216.3 million pages.
We’ll ignore Web page views because TidBITS pre-dates the Web. Although the World Wide Web celebrated its 30th anniversary on 19 March 2019, that was 30 years from the date of the proposal that Tim Berners-Lee wrote, not from when the Web became functional. I met one of the co-founders of the Web, Robert Cailliau, at the Hypertext ‘93 conference and mentioned the story briefly in “20 Years of the World Wide Web in the Public Domain” (1 May 2013).
How much paper is that, if laid out straight on a road?
It’s hard to visualize 216.3 million piece of paper, but there are 500 sheets in a ream, and a ream is roughly 2 inches (5 cm) thick. That makes 432,600 reams of paper, and lining them up on edge would thus create a row 13.8 miles (22 km) long. At the pace of my most recent half marathon—1:22:28 for the Montezuma Half Marathon last year—it would take me 1:26:43 to run that far. Tonya ran that race too!

How many trees have we saved?
Getting back to why we’re linking this anniversary to Earth Day, it’s all about the trees. There’s a commonly cited number that a tree produces 8333 sheets of paper. So that’s nearly 26,000 trees. Which sounds like an awful lot, but you don’t want to lose sight of the forest for all those trees. A healthy forest has about 50 trees per acre, so we avoided clearcutting 519 acres (2.1 square kilometers) of virgin woodland. Yay, us!
Can you still see the forest?
For visualization reasons, area calculations are commonly cited in terms of a number of football fields, ignoring the fact that it would be extremely difficult to play football in a forest, especially if there were wild animals of the fierce type living there. Regardless, a football field turns out to occupy 1.32 acres, so we saved 393 football fields of trees. Or, for those for whom football means soccer, where the field is somewhat wider, that would be 292 soccer fields. I think soccer would be even harder to play with trees in the field, although much more amusing thanks to all the ricochets.
How much would that have cost?
Of course, we could never have afforded the necessary paper, printing, and distribution costs that a paper magazine would have required without subscriptions and vastly more advertising—that’s how magazines work. And, increasingly, why they don’t work at all anymore, which accounts for all the magazine closures in the last few years.
But the beauty of the Internet, particularly back in 1990, was that it made it possible for a couple of kids just out of college to start a publication and somehow keep doing it for the next 29 years. Check out the full TidBITS History series for lots of great stories.
As always, we couldn’t have done this on our own. Or maybe we could have, but it would have been a lot less fun given the wonderful people who have helped out over the years. And we certainly couldn’t have kept doing it without the support of thousands of readers who help us keep the servers running, pay our writers and employees, and put cheese on the table.
If you’re not currently a TidBITS member, we’d appreciate it immensely if you’d join, and we have a bunch of perks and discounts on Mac apps for those who do. Thanks for all the cheese, and let us know if you have any great ideas for how to celebrate our 30th anniversary next year!

Was Your Data Included in Recent Security Breaches?
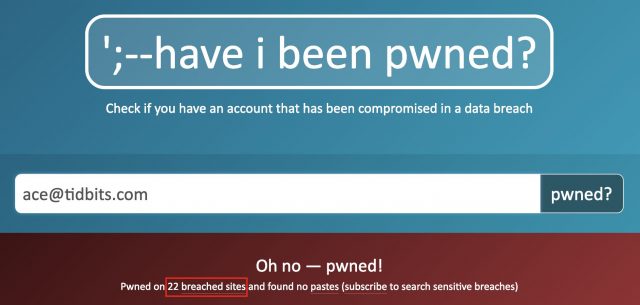
So far in 2019, I’ve received four email notifications from the Have I Been Pwned service, each one alerting me that I was one of tens or hundreds of millions of people whose data was stolen in a security breach. In fact, if I add up all the people whose data was compromised just in those four breaches, the total comes to 1,588,640,494. That’s right—over 1.5 billion records of data, including names, email addresses, passwords, dates of birth, employers, genders, geographic locations, IP addresses, job titles, phone numbers, and physical addresses.
Such laxity and malfeasance are incredibly distressing, but these breaches are all in the past, and there’s absolutely nothing you or I or anyone else can do about that exposed data now. However, any of that data—particularly passwords—could be used against you, so it’s essential to make sure that you’re as protected as possible from such attacks.
The best thing to do is to make sure that you’re using a password manager like 1Password (TidBITS members get six months free!) or LastPass to create a strong, unique password for every Web site. That way, even if one site is compromised, as seems to happen every other week now, your accounts on other sites won’t be vulnerable (and yes, this happens; it’s called credential stuffing). According to one 2017 survey, as many as 25% of users reuse the same password across a majority of their accounts, and over 80% of people have reused the same password across two or more sites.
If you fall into that 25%, or someone close to you does, I strongly recommend Joe Kissell’s recently updated Take Control of Your Passwords, Third Edition. It’s one of Take Control’s best-selling books because it explains everything you need to know about making your online accounts more secure and simultaneously easier to access. And if you or someone you know has ever said, “But I don’t have anything to hide,” read Joe’s Take Control of Your Online Privacy, Fourth Edition, which he just updated with essential advice on dealing with all the latest threats. (It explains what you do have to hide.) Each book costs $14.99, but you can buy both together for just $20.
One last thing: Take a minute and search for your email address on the Have I Been Pwned site. It will tell you how many breached sites contained your address. (Don’t worry, the site is safe to use; the email address is never stored.) My address, which I’ve used broadly and consistently for many years, has been caught up in 22 breaches; if you can beat that, let me know in the comments.
Google Keep Now Supports the Apple Watch, Apple’s Notes Still AWOL
Apple’s Notes app for iOS has improved in recent years (see “Five Major New Capabilities in Notes in iOS 11,” 5 October 2017), but it still suffers from a baffling omission: a lack of Apple Watch support.
An Apple Watch version of the Notes app would serve those who want at-a-glance access to shopping lists and the like without having to dig out an iPhone, or who want to dictate quick notes on their wrists to avoid losing track of fleeting ideas.
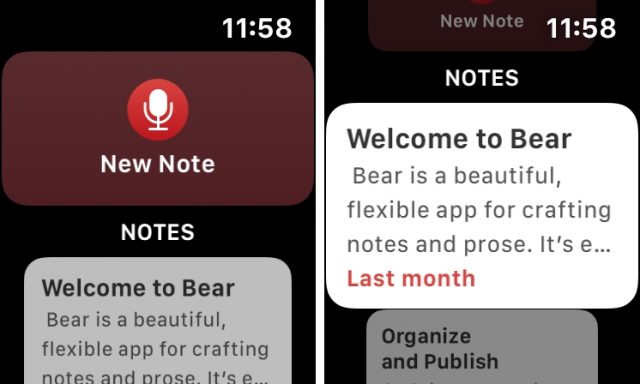
Apple Watch support is a common feature in note-keeping apps for iOS, which makes its absence from Notes all the more puzzling. Apps that include this capability include Awesome Note 2, Bear, Drafts, Evernote, Microsoft’s OneNote and Soho’s Notebook—more on them in a bit.
Now you can add another note-keeping app to the list: Google Keep.
This ends Google’s absence from the Apple Watch platform after the search giant dropped the watchOS version of its Maps app in May 2017. It’s a welcome development for iOS users like me who are heavily invested in the Google ecosystem and largely prefer Google apps for the iPhone over Apple equivalents.
Viewing Google Keep Notes
Fire up Google Keep on your Apple Watch and you’ll see your 10 most recent notes. The small screen means you won’t want to tap into your extensive notes archive, but you do have other interesting options:
- Text notes: If a Google Keep note has a lot of text, much (if not necessarily all) of it will show up on your Apple Watch. In testing, I got eight short paragraphs or six longer paragraphs, to appear in a note on my watch. More than that was truncated.
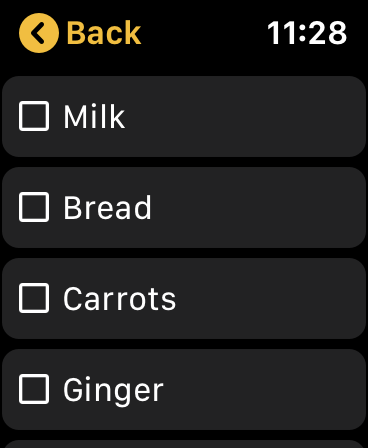
- To-do lists: You can set up notes as to-do lists by adding checkboxes when creating them. Then you can tap on your iPhone—and, now, also on your Apple Watch—to check off items. As you do so on the watch, you will get haptic feedback, which is a nice, um, touch.
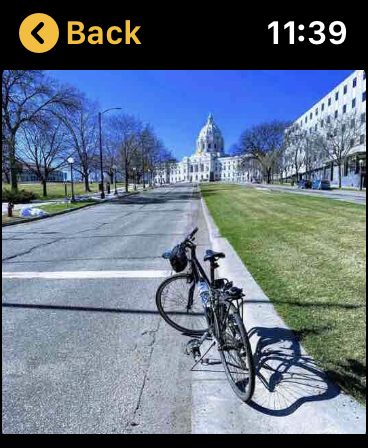
- Pictures: You can embed images in a Google Keep note, and those will show up on the watch eventually—I experienced syncing delays of up to several minutes.
- Notes with drawings: In its Web and iOS versions, Google Keep lets you doodle, draw, and sketch with a decent selection of creation tools, paper types, and more. Once you’ve scribbled something, it will show up on the watch eventually—as with picture notes, I experienced syncing delays of up to several minutes.
- Web clippings with URLs: Sharing extensions for iOS and the Google Chrome Web browser let you use Google Keep as a basic Web-clipping tool. Save a page and you get a URL and a thumbnail in those versions, but on the Apple Watch, all you can see the URL, and you can’t do anything with it.
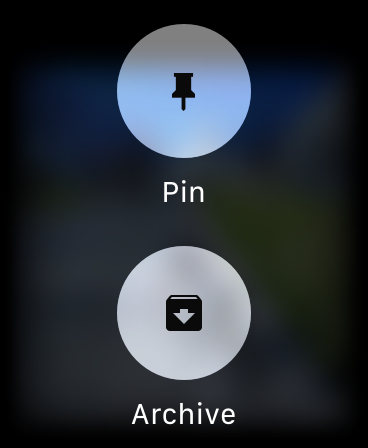
- Pinning and archiving. Google Keep offers the option to “pin” a note so it always appears at the top of the screen in the iOS app and the Web interface. Apple Watch users also can do this by force-pressing a note to reveal a pinning button—though this has no effect on how notes are shown on the watch. Another force-press option lets you archive a note if you no longer want to see it on any of your devices.
Composing Google Keep Notes
Google Keep for Apple Watch wouldn’t be complete without tools for composing notes. Force-press on the main screen (but not on a note) and a button called Text Note appears. Tap it and you get three composing options:
- Microphone: Dictate a note and Google Keep will automatically transcribe it (using Siri, as nearly as I can make out) to create a text note. Dictation accuracy is pretty good.
- Drawing text: Use your finger with the Apple Watch’s Scribble feature to draw the shapes of letters, numbers and other characters. Google Keep does a pretty good job of deciphering your doodling to assemble words and sentences.
- Emojis: Google Keep provides one-tap access to an emoji library. Common or recently used emojis are shown first, followed by category buttons that lead to corresponding emoji groupings. Tap an emoji to insert it into a note.
What’s Missing in Google Keep?
Some of the features of the iOS and Web versions of Google Keep, such as complex drawing, don’t make sense on the Apple Watch, with its small screen and minimal input options.
However, more irksome is the fact that the watchOS version of Google Keep trails the version Google makes available for smartwatches that use its Wear OS. Google Keep for Wear OS lets you compose lists as well as notes directly on the watch, set up reminders, and displays three times as many notes.
How Do Other Apps Compare?
As I noted earlier, Google Keep isn’t the only notes app to support the Apple Watch, and other apps are more sophisticated in some ways:
- Voice notes: Dictation has its limitations but you can avoid them in some apps by creating an audio note instead. Drafts, Evernote, and Soho’s Notebook let you create voice notes on your watch and can sync them to your iPhone.
- Show more notes: Google Keep’s 10-note limit feels arbitrary and unnecessarily restrictive. Other apps are less draconian. Notably, Microsoft’s OneNote lets you scroll through several dozen notes on the watch screen.
- Better organization: OneNote offers a notebook organization system and color-codes notes on the Apple Watch to match their notebooks. SoHo Notebook does roughly the same thing. Drafts, meanwhile, provides an Inbox to stash drafts and lets you create organizational cues (tags, flags, and more) within notes.
- Appearance: Most notes apps for the Apple Watch have generic, utilitarian looks. Not so Bear, which, like its iOS and Mac incarnations, is quite attractive.
- Integration: For an all-in-one approach, there’s Awesome Note 2, which combines notes with task and schedule functions, and integrates with iOS reminders and calendars. On the Apple Watch, you can toggle between Awesome Note 2’s note and event/reminder functions.
A Final Note
The addition of an Apple Watch version of Google Keep isn’t likely to compel anyone to switch away from their preferred notes app. But if you happen to be in the market for a notes app and you use an Apple Watch along with an iPhone, it’s worth a look, particularly if you prefer Google services over Apple’s equivalents
In particular, I don’t see many users of Apple’s Notes defecting to Google Keep because of this watchOS support, but it maybe it will put more pressure on Apple to make its Notes app work on the Apple Watch.
What Does the T2 Chip Mean for Mac Usage?
Beginning with the iMac Pro in December 2017—and continuing with Mac mini, MacBook Air, and MacBook Pro models introduced in 2018 and onwards—Apple has packed Macs with its own homegrown T2 chip. Like its predecessor, the T1, the T2 is designed to shift responsibility for security-critical aspects of Mac hardware out of the hands of the Mac CPU and traditional computing components—where they can be subject to hacks and malfeasance—into a “secure enclave,” a separate environment inaccessible to hacks, malware, and even hardware-based security risks. Even if macOS were somehow completely “pwned” by a security flaw or attacker, the critical functions and data handled by the T2 would be completely unaffected.
These days, it’s safe to say most technology users are interested in more security, rather than less, so the benefits of the T2 seem clear, if decidedly nerdy. But that doesn’t mean a T2-equipped Mac is the right choice for every Mac user right now—even those who want to be as secure as possible.
Why Does Apple Need Security Chips?
It’s no secret Apple’s hardware group has been on a roll for the last several years: it currently makes five processor lines (the A, H, S, T and W chips) that power everything from iPhones and iPads to the Apple Watch and AirPods. So it’s not surprising Apple would bring its own silicon to the Mac to enable Apple-exclusive features.
The company introduced the T1 in late 2016 to handle the fingerprint processing for Touch ID sensors in the first Touch Bar-equipped MacBook Pros, and it also helped lock down sensitive components like the built-in microphones and cameras. Further, the T1 took over the System Management Controller (SMC), which is responsible for heat and power management, battery charging, and sleeping and waking the Mac. Finally, the T1 determines if macOS is running on actual Apple hardware.
The T2 picks up from there, with four major capabilities:
- It takes over all access to built-in solid-state drives, enabling real-time encryption and decryption so your data is never stored in the clear
- It provides the processing power that lets you invoke Siri with “Hey Siri”
- It offers image enhancement for built-in FaceTime HD cameras
- It can optionally lock down a Mac’s boot process—so if someone were to steal your Mac, they wouldn’t be able to start it up using an external drive and steal your data
The T1 and T2 can do all these things because they’re basically separate computers with their own isolated memory and storage: they’re ARM chips running Apple’s bridgeOS. The T2 is based on the A10 processor that shipped in the iPhone 7, and bridgeOS derives from Apple’s watchOS. In some ways, the T1 and T2 act as independent co-processors, enhancing performance by handling common tasks for the Mac and enabling the CPU to focus on other things. But in other ways, they significantly beef up security, since they offer a fully independent system that remains secure even if macOS is compromised.
What Does The T2 Do For You?
Apple has published an overview of the T2 chip spelling out some of its technical details, but here are the main points:
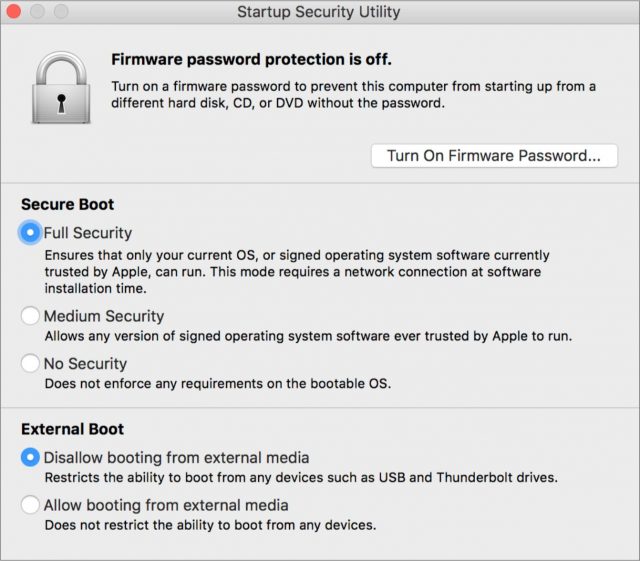
- Secure Boot: The T2 ensures all components of the startup process—including firmware, the kernel, any kernel extensions, and bootloaders—can be cryptographically verified as trusted by Apple before booting. The idea is to prevent the Mac from being started up on compromised low-level software, thereby exposing users’ data. Secure Boot also covers Recovery Mode, Diagnostics mode, and Internet Recovery mode. By default, Secure Boot trusts only software signed by Apple or—get this—signed by a Microsoft certificate to authenticate Microsoft bootloaders. That means Boot Camp installations of Windows 10 on the internal SSD have all the benefits of Secure Boot, but anything else—like Linux—is currently out in the cold.
Macs with T2 chips also have the Startup Security Utility available in Recovery Mode. Users (with a valid admin password!) can set a firmware password and/or downgrade some Secure Boot functionality. However, the No Security setting doesn’t necessarily enable untrusted operating systems to start up using the internal SSD, since they’d have to support the T2 as a storage controller (sorry, Linux). Using other operating systems seems to be possible only from external drives, and they gain virtually none of the benefits of the T2, including fingerprint authentication. - Encrypted Storage: The T2 enables on-the-fly encryption and decryption of data on a Mac’s built-in solid-state drive. The encryption uses the same technology as FileVault and requires a valid password to boot up. Because the T2 is a separate system, it can enforce delays on failed password attempts: there’s a limit of 30 password attempts on the Login window or in Target Disk Mode, with a 1-minute delay on each after 14 failures. More attempts are available in Recovery Mode and FileVault recovery (including iCloud recovery), but the delay can grow to as much as an hour between allowed password attempts. This sort of delay makes brute-force password attacks impractical. However, don’t expect to see the T2’s on-the-fly encryption on anything but internal SSDs: Macs with traditional hard drives (some new iMacs still have them!) will probably never see this benefit. External drives don’t gain this protection, either.
- Touch ID: On the MacBook Pro and MacBook Air, Touch ID works much as it does on iOS devices: you get five tries to match a fingerprint, and the odds of any random fingerprint matching one stored in Touch ID are about 1 in 50,000. (So if you set up 5 fingerprints, roughly 1 in 10,000 will unlock your Mac. That’s a lot of grubby hands on your Mac.) The Mac will still require a password at startup if it hasn’t been used in 2 days, or if no password has been used in roughly a week. (The real criteria are that a password hasn’t unlocked the Mac in 6.5 days and no fingerprint has unlocked it in 4 hours.)
- Hush, Now: All T2-equipped MacBook Pro and MacBook Air models have a hardware disconnect for the built-in microphone whenever the lid is closed. That means even if some malware were able to take control of your microphone and surreptitiously listen or record through it, the microphone is essentially physically unplugged from the Mac when you close the lid. The same can’t be said of headsets, external microphones, or other audio gear, though. There’s no hardware disconnect for the FaceTime HD cameras: closing the lid blocks them effectively.
Downsides of the T2
For most Mac users, the benefits of the T2 are clear, particularly for notebook users who take their Macs with them wherever they go. If your new MacBook Air is stolen, the T2 offers decent assurance that sensitive data—like email, passwords, credit card numbers, social media accounts, super-secret projects, or those pictures—won’t fall into the wrong hands.
The T2 isn’t without trade-offs, however:
- Less Repairability: The T2 chip requires technicians to run a proprietary diagnostic tool to replace certain components like flash storage, the Touch ID sensor, and the main logic board, which means repairs or replacement of those components can only be done at Apple Stores or by Apple Authorized Service Providers. Most Mac users will never need to replace those components, but it’s yet another way Macs are becoming less repairable.
- Goodbye, NetBoot: T2-equipped Macs can’t boot from network volumes, which could be a serious issue for organizations and schools that still rely on the now-deprecated NetBoot. If you need NetBoot, take note: Apple’s recently refreshed iMac line does not have the T2 chip (see “Apple Boosts iMac Performance with Faster Multi-Core CPUs,” 19 March 2019).
- Data Recovery As-Good-As Impossible: That on-the-fly encryption and decryption the T2 chip provides for the SSD means the T2 is the only way to get data off the internal drive. If the T2 is damaged or becomes inoperable, your data is inaccessible, even to top data forensics experts, so have a solid backup strategy in place—check out Take Control of Backing Up Your Mac, Third Edition for all you need to know in that department.
- Linux & Older Windows Boot Issues: Lots of software developers—particularly Web developers—prefer to work in Linux or other operating systems, even if they own a Mac. T2-equipped Macs can only boot Linux or versions of Windows prior to Windows 10 from external drives after disabling the T2’s Secure Boot feature. If you need to run one of these operating systems, get used to doing it in a virtual machine. If you must run one of these systems on “bare metal,” a T2 Mac is not for you.
So What’s With These Audio Problems?
Since the introduction of the iMac Pro—and continuing with newer T2-equipped Macs—users have reported occasional audio glitches: little clicks, pops, or bursts of noise that seem to happen at irregular intervals. They occur with both audio playback and audio recording, and can happen using any app, whether listening to Apple Music, watching a video on YouTube, playing a game, or—uh oh!—playing a hot DJ set at a party or recording a live symphony orchestra.
The problem seems most common with USB-connected audio devices—whether consumer-grade headsets, podcaster-level microphones, or professional audio gear—but the glitches also happen with built-in speakers and microphones as well as audio devices connected via Thunderbolt. How often do they happen? Hard to say. Some users see a few every hour, others maybe only one per day.
Many Mac users won’t care. If there’s a little pop while streaming “Baby Shark” for the thirty-first time, it’s not the end of the world, am I right? OK, maybe I’m right?
However, for others, these glitches are literally showstoppers. If you’re using your Mac to process live audio—maybe you’re a DJ, or a musician using your Mac to run software instruments with programs like Ableton Live or Apple’s MainStage—blasting your audience with random pops, clicks, and bursts of sound is a Very Bad Thing. If you are recording music—whether in your bedroom using GarageBand or burning through hundreds of dollars per hour in a professional studio—those glitches will inevitably happen during critical moments, often destroying your recording. Imagine telling a legendary performer: “Hey, that was great, but the Mac glitched. Let’s go again, maybe it’ll record OK this time!” It’s a quick way to end a career. For musicians and audio professionals, this problem makes T2 Macs unreliable and untrustworthy—an irony, since many of these people use Macs to avoid the famous undependability of audio setups under Windows.

For professional recording studios, the T2 chip isn’t yet much of a problem. (No joke: plenty of Mac-based recording studios are still using decade-old Mac Pro towers.) But a tremendous amount of amateur, enthusiast, and professional audio work—whether music, podcasts, mixing, or DJing—doesn’t happen in professional studios: it happens on notebooks and in small Mac-based project studios. Plenty of musicians take their Macs on stage with them to perform in real time. The T2 is spreading across ever-greater swaths of Apple’s Mac lineup, which makes choosing a new Mac difficult.
What to do? The T2 audio problems have been known for well over a year, and Apple has been utterly silent about them save for a vague claim that macOS Mojave 10.14.4 “improves the reliability” of USB audio devices used with T2-equipped Macs. Some audio developers (like Germany’s RME) have reported improvements with USB audio, but my limited testing with a T2-equipped MacBook Pro found no discernible improvement using 10.14.4 with USB or Thunderbolt audio devices.
Some T2 users have been able to reduce the frequency of glitches by killing the built-in timed process (which synchronizes the Mac clock with a time server) and/or locationd (which tries to determine a Mac’s location for Location Services). Some folks have had good luck with these workarounds; others still experience problems. Unfortunately, stopping these background processes is non-trivial and requires disabling macOS’s System Integrity Protection. In other words, not recommended.
Is A T2 Mac Right For You?
For most Mac users, the T2 chip offers clear benefits: not only does it power spiffy fingerprint detection on the MacBook Pro and MacBook Air, but it also provides fully encrypted storage and hardens the Mac against a range of sophisticated attacks—including the sorts of things that a government might carry out if one were to seize a computer.
But the T2 also highlights how fragile the Mac world can be. Users who don’t have easy access to an Apple Store or authorized repair shop may encounter real problems getting a T2 Mac fixed. Users who don’t have a good backup strategy probably won’t be able to recover any data at all if the T2 chip fails—even if they turn to data recovery experts. And developers who want to run anything but macOS or Windows 10 natively are basically out of luck. So if your Mac has a T2 chip, figure out in advance where you’ll get it repaired if necessary, make sure you’re backing up regularly to multiple locations, and stick with virtualization for guest operating systems.
All that said, if you rely on your Mac for audio—whether recording podcasts, DJing parties, or as a professional engineer or musician—I recommend avoiding T2-equipped Macs until audio issues have been verifiably resolved for quite some time. If you need a new Mac before that happens, consider one of the few remaining models without a T2 chip, or perhaps an older pre-T2 Mac—sometimes Apple offers a good deal on refurbished and clearance models.
 Josh Centers
No
comments
Josh Centers
No
comments
 Josh Centers
2
comments
Josh Centers
2
comments