#1641: LastPass breached, Live Text aids recipe input, fix for failed MobileDeviceUpdater installs
Welcome to 2023! Our first issue of the year focuses on the serious security breach suffered by password management service LastPass, explaining what happened and how users should react. Adam Engst passes on a TidBITS reader’s surprising fix for installation failures that can afflict MobileDeviceUpdater, the software that lets Macs talk to USB-connected iPhones and iPads. He also shares a tip for using Live Text in iOS to scan printed cookbook and magazine recipes into the Paprika recipe management app. Notable Mac app releases this week include Affinity Designer, Photo, and Publisher 2.0.3, SuperDuper 3.7.2, Airfoil 5.11.4, Audio Hijack 4.0.7, Piezo 1.7.12, SoundSource 5.5.7, Quicken 6.11.1, BusyCal 2022.4.7, Pixelmator Pro 3.2.3, Default Folder X 5.7.3, Zoom 5.13, Mimestream 0.40.2, Alfred 5.0.6, and Lunar 5.9.1.
A Fix for MobileDeviceUpdater’s “Installation Failed”
Of all the processes Apple manages under the hood of macOS, few are as mysterious as MobileDeviceUpdater. When macOS requires a driver update to talk to a USB-connected iPhone or iPad, this software agent launches an installer that doesn’t look like any other macOS activity.
Despite MobileDeviceUpdater’s alert sometimes causing people to wonder if it’s malware or a phishing attempt, it’s a real and necessary update that you must install to enable your Mac to talk to your iPhone or iPad. Because you might update your devices on different schedules, it’s common to end up in a situation where an older version of macOS doesn’t know how to interact with a newer version of iOS or iPadOS.
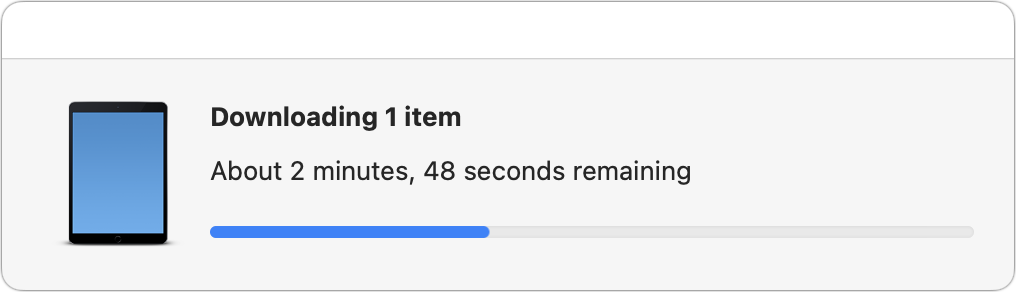
When you see this alert after plugging your iPhone or iPad into your Mac, go ahead and click the Install button. You’ll see a progress window for downloading and installing. When it finishes, all will be well—or should be!
The installation can fail. What do you do in that event? Apple provides no suggestions about how to resolve the problem if you see this dialog at the end of the installation.
I hadn’t experienced this problem until about a month ago when I plugged my iPad Pro into a 2020 27-inch iMac running macOS 12 Monterey. I wasn’t even trying to sync; I just wanted to charge. Although I never sync my iPad or iPhone over USB, I figured I’d agree to the installation to prevent future dialogs from nagging me. So you can imagine my irritation when an installer that I didn’t even want to run failed. I tried restarting the iPad and the Mac, but neither made any difference.
By happenstance, TidBITS reader James Weil posted a solution on TidBITS Talk a few days later. It was my lucky day, and now it may also be yours. Follow these steps:
- In versions of macOS before macOS 13 Ventura, open System Preferences > Sharing; for Ventura, open System Settings > General > Sharing.
- Uncheck every service that’s enabled. For me, it was Media Sharing, Content Caching, and AirPlay Receiver.
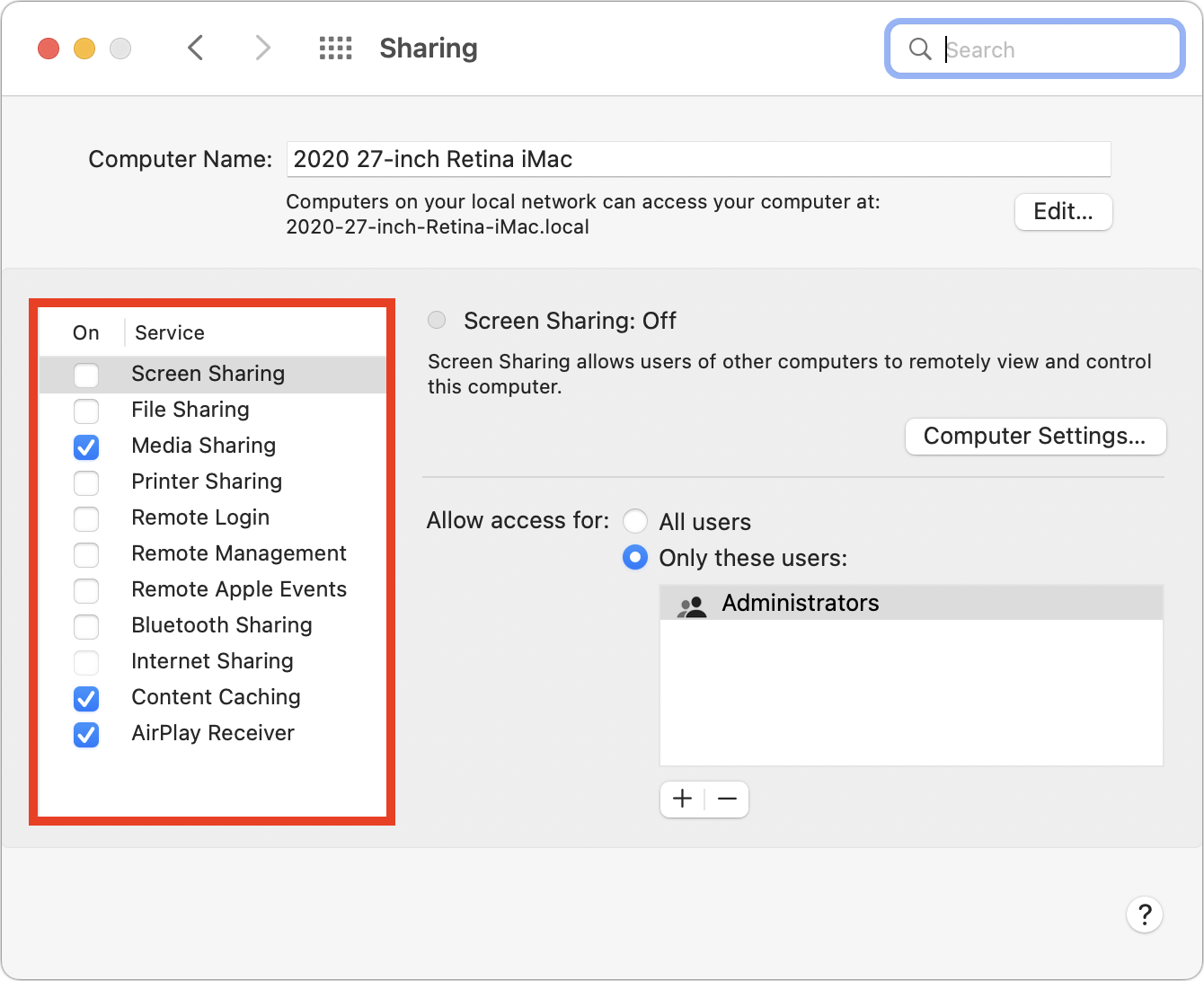
macOS 12 Monterey’s version of System Preferences is shown above, but the same actions happen with switches in Ventura. - Unplug the iPhone or iPad and then plug it back in.
- When MobileDeviceUpdater prompts you again, click Install. This time the software update should download and install correctly. Interestingly, the download took significantly longer to complete than when it failed, with a several-minute progress bar. That suggests the problem relates to the download.
- Enable the services in Sharing that you previously turned off.
Because I successfully ran through this process in December, after James first posted, I was a little surprised when the same error cropped up again just now. It seems that the error can recur, forcing you to repeat this process each time new software updates cause your Mac and iPhone or iPad to fall out of sync.
Confusingly, it didn’t appear that any one of the enabled services was at fault. I turned off the three services I had enabled one at a time, attempting an installation before re-enabling the service and moving on to the next. I didn’t expect Media Sharing or AirPlay Receiver to be the culprit, but I could imagine a connection between MobileDeviceUpdater and Content Caching. But no: leaving any of the services running caused MobileDeviceUpdater to fail. As soon as I disabled them all, it downloaded and installed fine, just as James said it would.
This solution is deeply unsatisfying, along the lines of voodoo fixes of yesteryear like rebuilding the Desktop or zapping PRAM. I’m open to suggestions for what might cause the problem, but without such an explanation, I can’t guarantee that this solution will work for you. At least it’s easy to try. (And if it doesn’t work, post in the comments below, particularly if you find another solution.)
Apple should put in the time to fix this problem once and for all.
Use Live Text to Digitize Your Cookbooks
I love cookbooks. I’m a sucker for paging through them and trying to imagine how difficult recipes will be and what they will taste like. Some authors, like J. Kenji López-Alt and Deb Perelman, are tremendously amusing, and cookbooks often have luscious photos that are always prettier than what I end up plating.
But my no-longer-secret shame is that after an early infatuation with a cookbook, it often ends up on my shelf, brought down only occasionally for a handful of recipes. Sometimes those favorites are marked with sticky tabs or bookmarks; more frequently, I resort to the index. Much as I approve of the Eat Your Books searchable recipe index site, I never managed to work it into my habits (see “Use the Web to Cook Your Books,” 17 March 2022), so I often have to flip through a cookbook to find the one recipe I make repeatedly.
A few years ago, when Tristan was starting to cook on his own in college and asking for recipes for the foods he had grown up eating, we went all in on Paprika, a brilliant recipe app available for the iPhone, iPad, and Mac, along with Android and Windows (for our original coverage, see “FunBITS: Paprika Recipe Manager for iPhone, iPad, and Mac,” 14 March 2014). I can’t remember if there was a bundle deal then or not—the apps are now sold separately—but it’s a perfect use of Family Sharing since Tonya, Tristan, and I can all now access our family recipes from whatever device we have handy.
The hurdle with Paprika—and any digital alternative to analog cookbooks—is importing recipes. It does a solid job of importing recipes from websites using the systemwide sharing extension or while viewing a site within Paprika’s built-in Web browser. But most cookbooks don’t have companion websites, and even cooking magazines like Cook’s Illustrated often charge an annoying extra fee for digital access to the recipes you can read on paper.
My initial method of speeding up the process of transferring a recipe from a cookbook or magazine to Paprika was to use Voice Control’s dictation, which is still more capable than the improved dictation available in the iOS/iPadOS 16 keyboard (see “How iOS and macOS Dictation Can Learn from Voice Control’s Dictation,” 31 August 2020). It’s easy to read a recipe clearly enough to get a good transcription, although you must be careful to speak punctuation marks and line breaks. Between Web imports and dictated recipes, we now have over 200 favorites in Paprika, but I still frequently need to find recipes in our cookbooks.
With the rise of AI-driven image scanning, I recently wondered if Paprika would let me take a picture of a recipe, do OCR on the text, and recognize the layout to split out the description, ingredients, directions, and notes. Alas, the answer turns out to be no, and although such a feature does exist in other recipe apps, including CookBook, the reader-recommended Mela, and Recipe Keeper, I don’t want to switch away from Paprika just for that feature.
However, once I was thinking along the lines of scanning, I realized that the Live Text feature Apple introduced in iOS 15 can insert text detected in the camera viewfinder. Although Live Text is unquestionably cool, I hadn’t found any meaningful use for it until now. With Paprika, though, importing a recipe from a cookbook takes just a few minutes, far less time than dictating it.
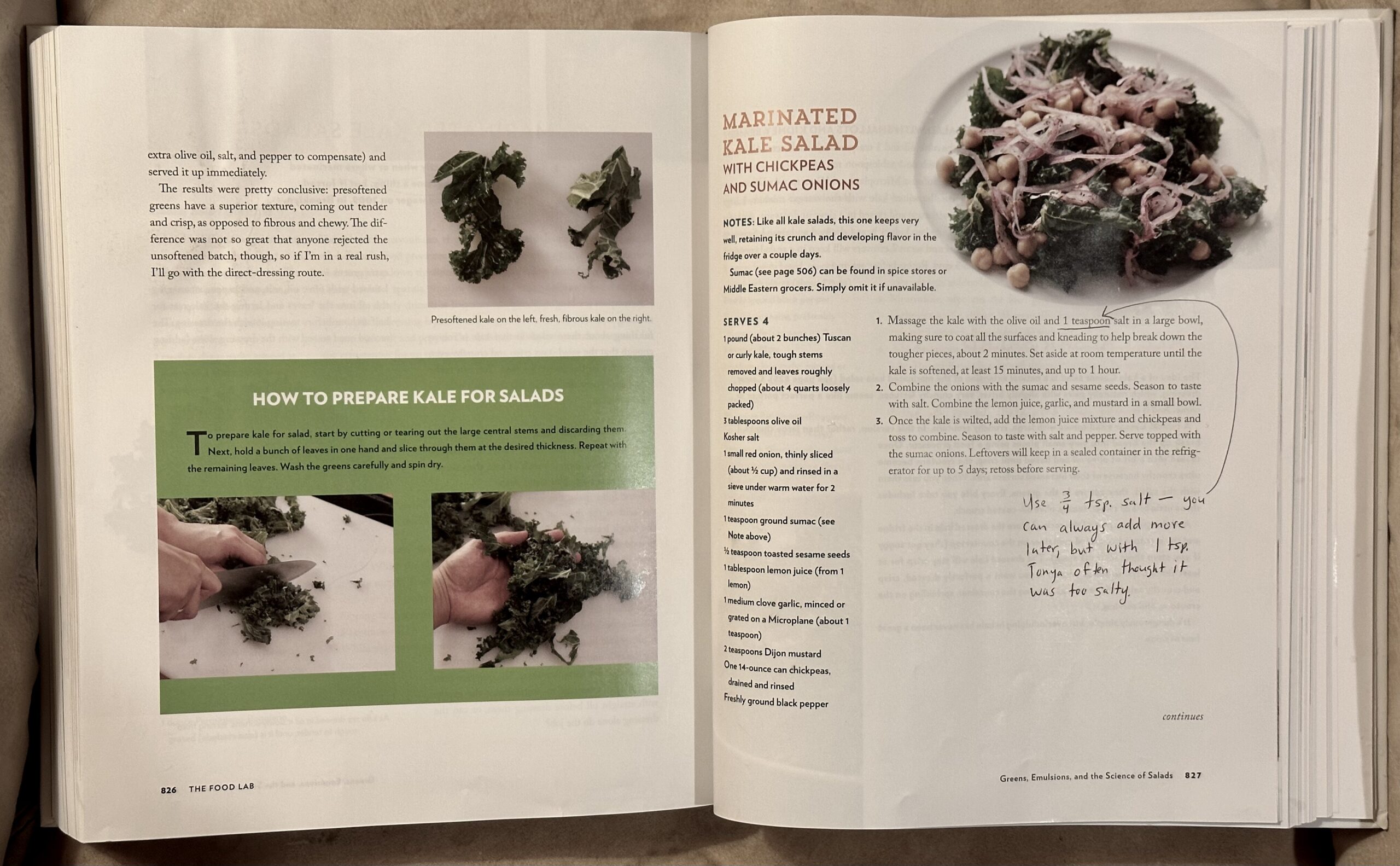
Here’s how I used Live Text to scan the “Marinated Kale Salad with Chickpeas and Sumac Onions” recipe from J. Kenji López-Alt’s The Food Lab, complete with some handwritten notes.
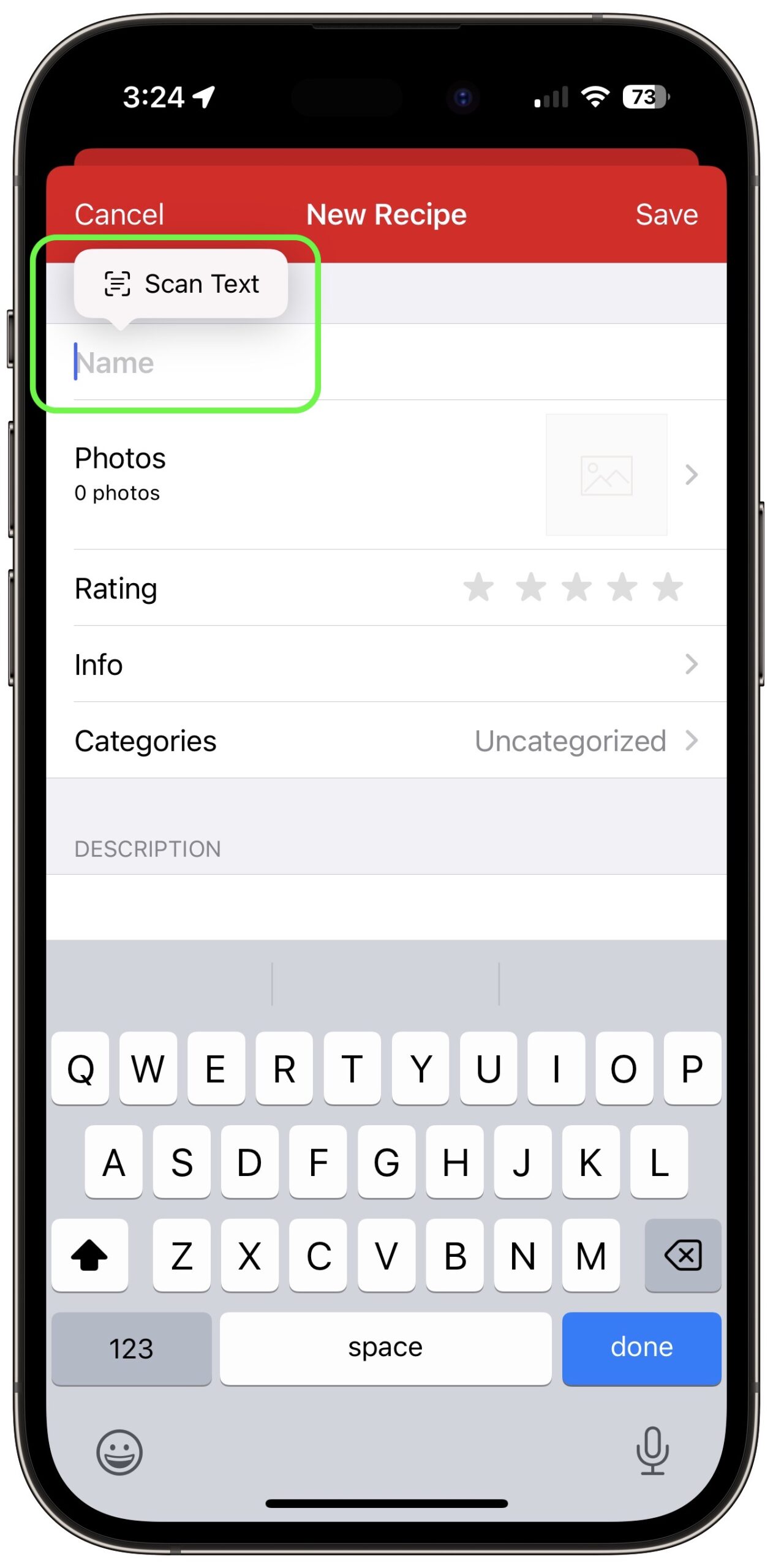
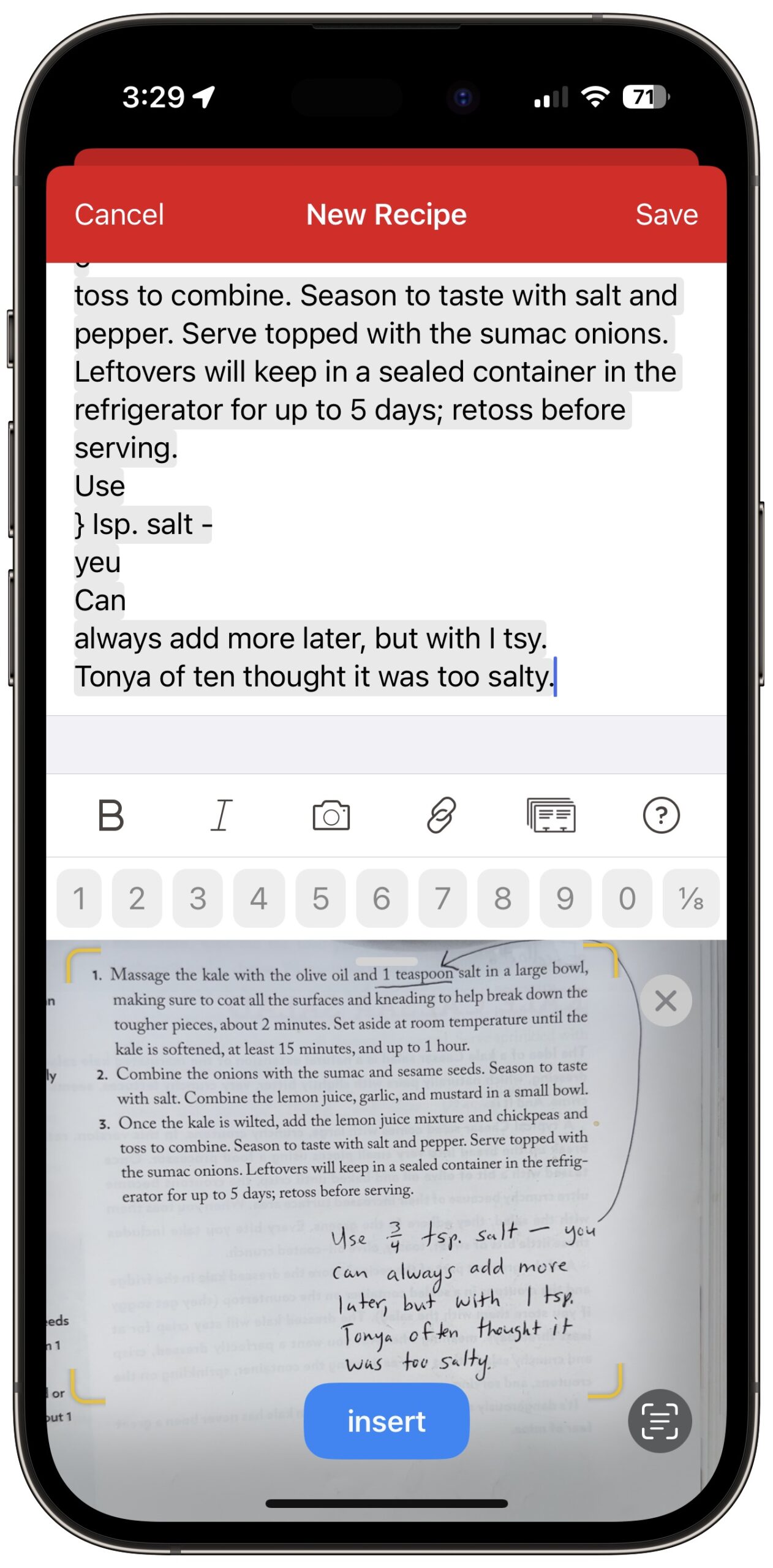
Start by creating a new recipe in Paprika. Then follow these steps, which you can see illustrated in the screenshots below:
- Tap the Name text field as though you were going to type in it.
- Tap the Scan Text button that appears. The Live Text camera viewfinder replaces the keyboard at the bottom of the screen.
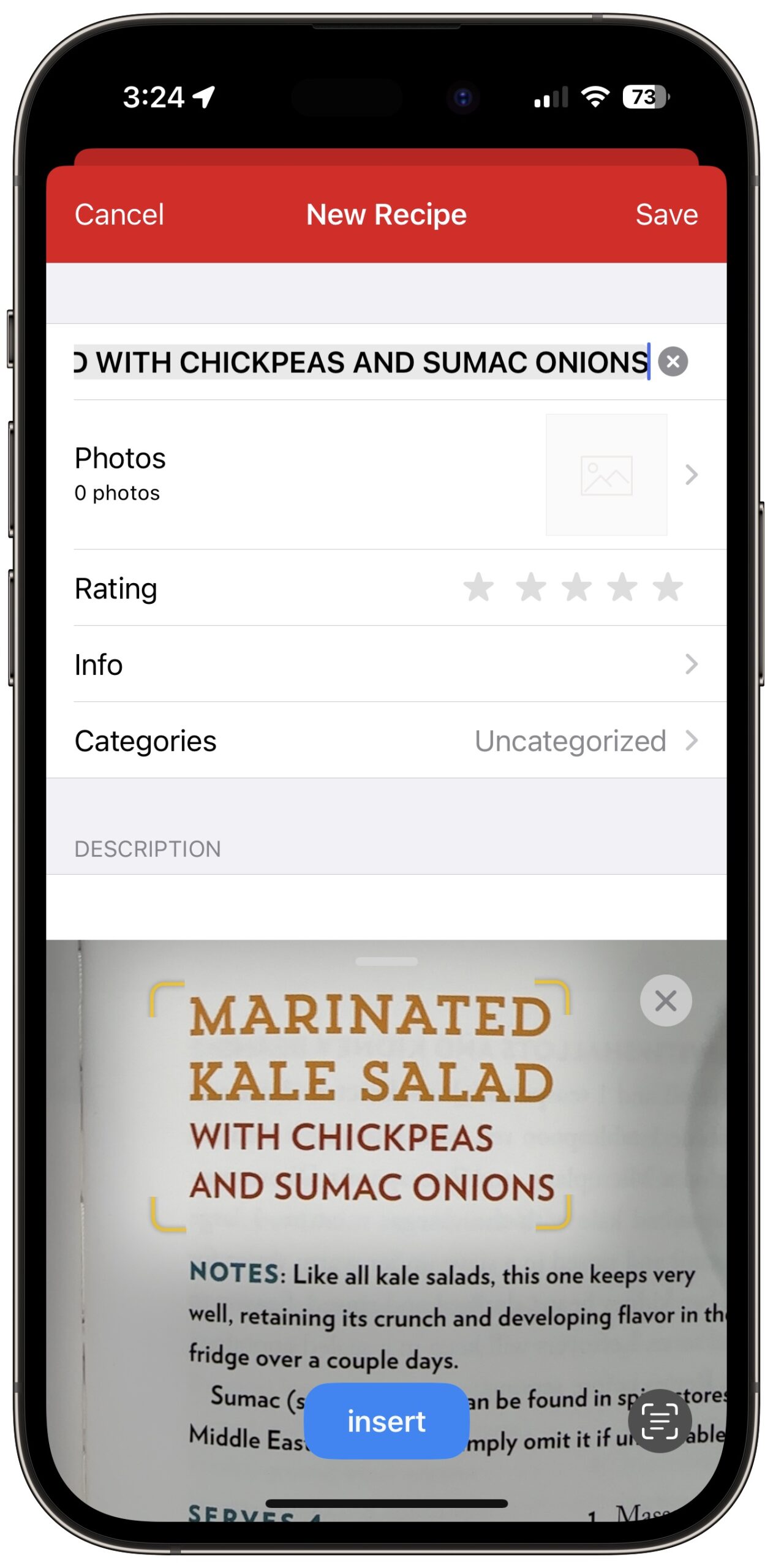
- Position the text you want to scan in the viewfinder and verify that it has yellow marks around it.
- Tap the blue insert button. (And no, I cannot fathom why Apple made it lowercase.)
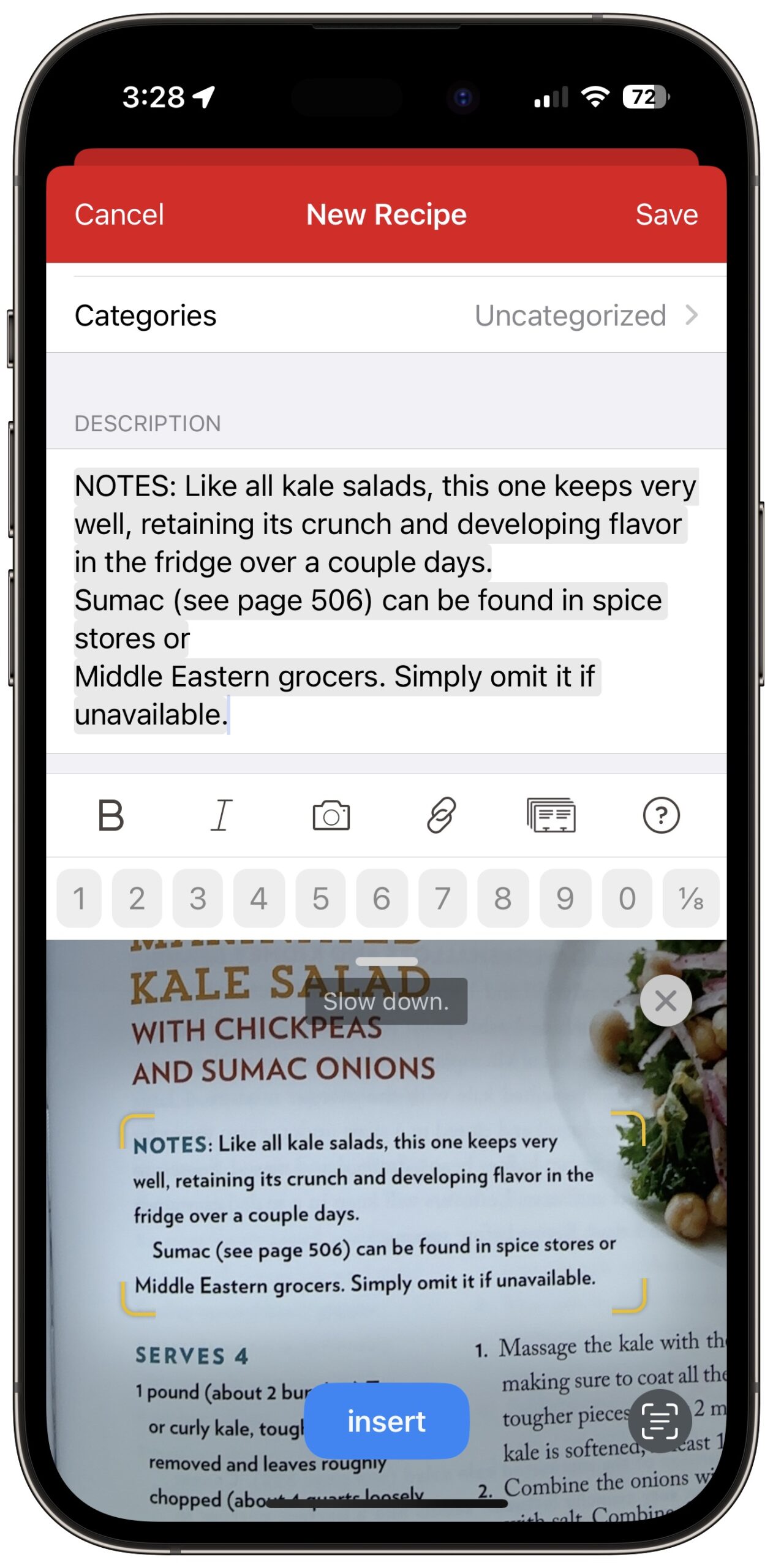
- Repeat with the rest of the fields in the recipe: Description, Ingredients, Directions, and more.
A few comments and tips prompted by the screenshots:
- In this recipe, the name is broken into multiple short lines, which works well with Live Text. When you’re faced with a long line length, whether for the name or other parts of the recipe, it’s difficult to get the desired text to fit in the viewfinder without also capturing more text above or below. You may have to insert more text than you want and delete it afterward.
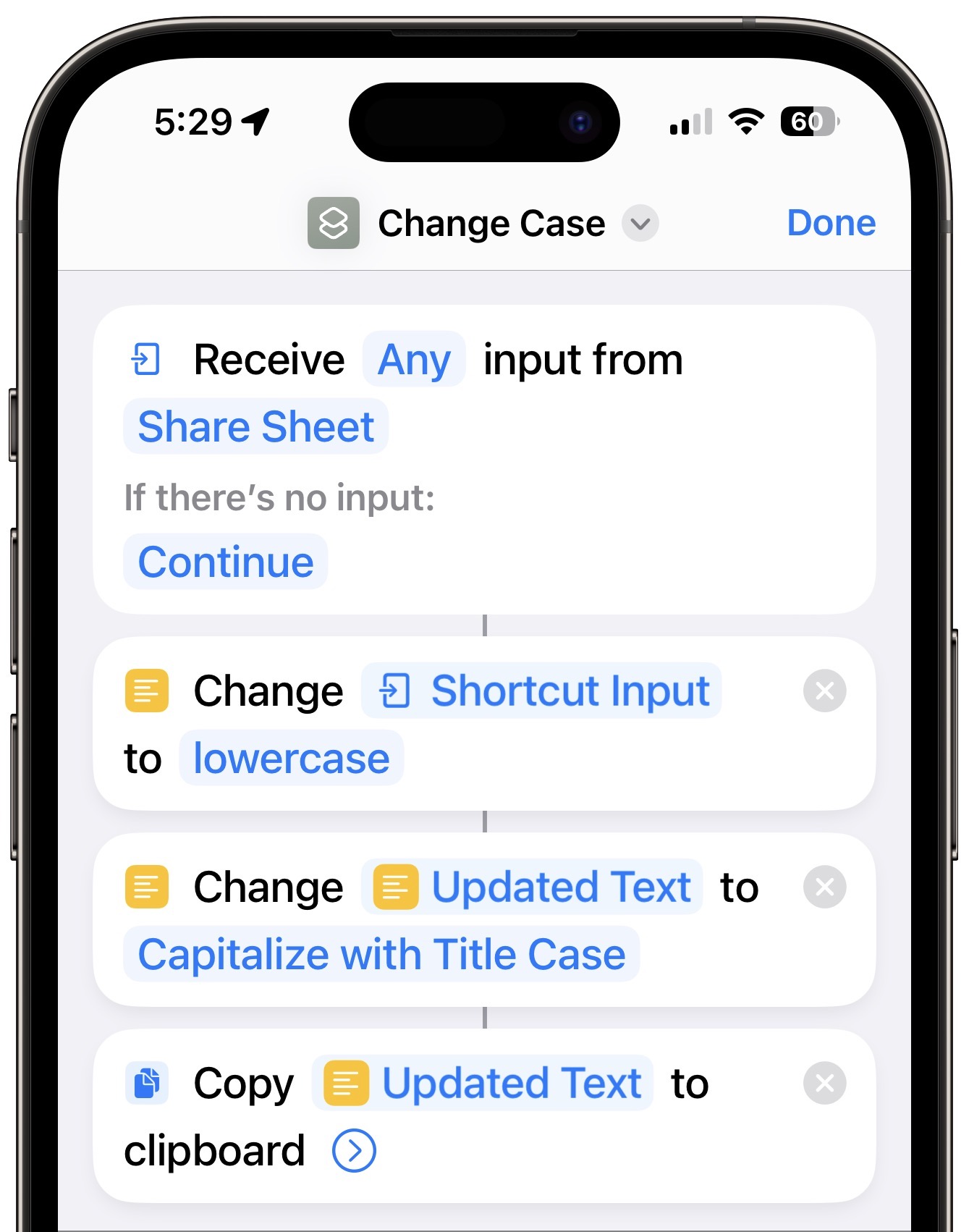
- Recipe names are often in all caps, which Live Text preserves. That bothered me, so I created a shortcut that converts any selected text to title case. Alas, it’s a bit fussy to use. To change an all-caps name after inserting it, you must tap in the Name field, tap Select All, tap the share icon, select this Change Case shortcut, close the share sheet, tap the still-selected text, and tap Paste. The $2.99 Text Case app might eliminate the need to close the share sheet, but that’s not a huge win. A tip of the hat to TidBITS Talk reader Nalarider, who pointed out that those with the Mac version of Paprika could use Keyboard Maestro or another Mac utility.
- Live Text previews the text to be inserted in the destination field, which can make you think that it has completed the task. But no, it’s not done until you tap the blue Insert button to fix the previewed text in place. I still occasionally make that mistake.
- Line breaks are tough for Live Text. Sometimes it adds unnecessary line breaks; at other times, it runs text together that should be broken across lines. It’s not terrible, but you’ll often need to do some editing to get the visual spacing you want.
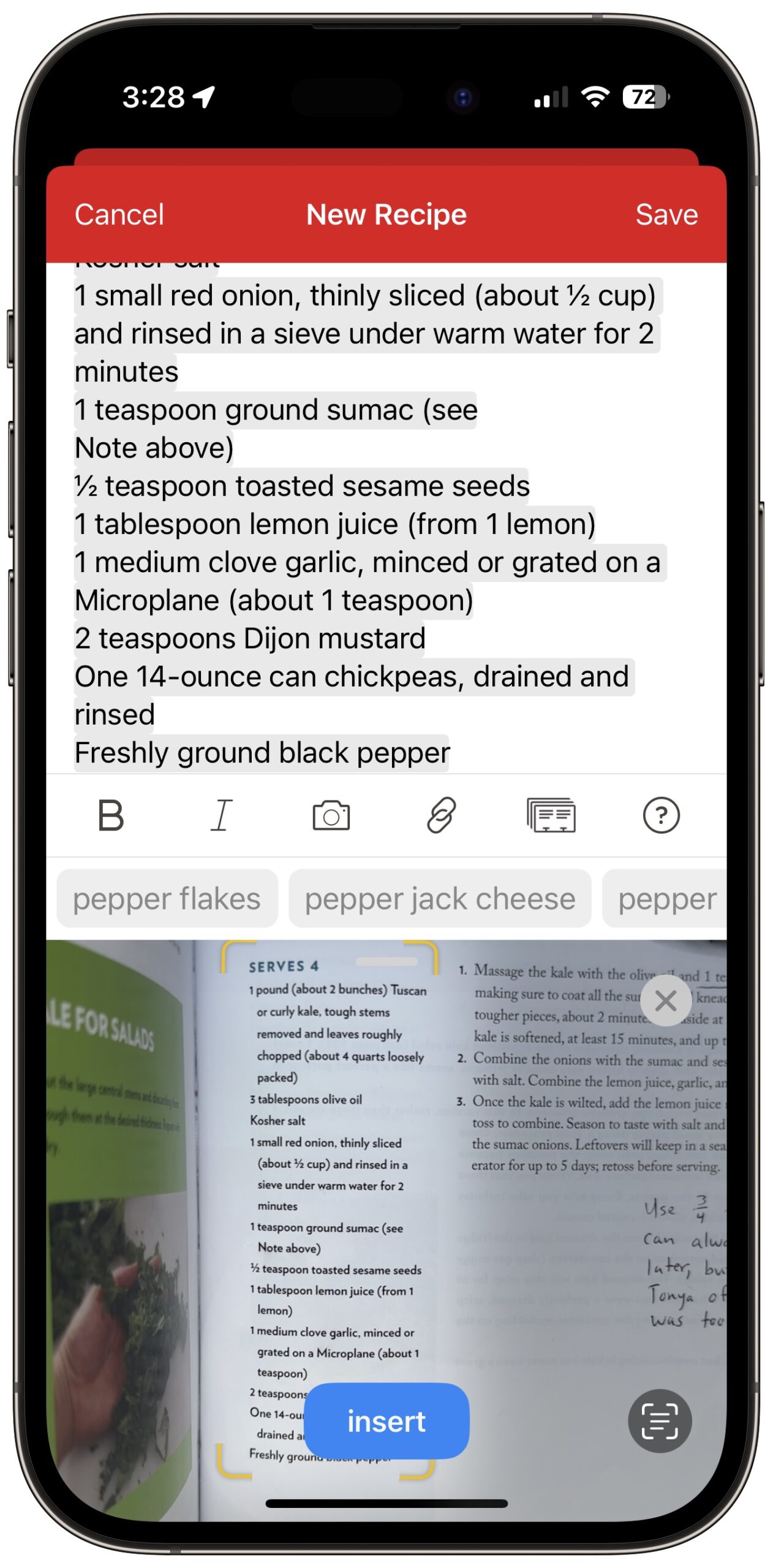
- Ingredient lists often contain proper fractions like ½, and I was impressed that Live Text captured and inserted them correctly. Paprika includes special keyboard shortcuts for inserting common fractions, but dictation only inserts regular characters, like 1/2.
- It’s not uncommon for an ingredient list to be broken across two columns. When that happens, scan the left column first and then the right. Scanning both at the same time won’t produce the results you want. After you scan the left column, tap below it in the Ingredients field, and you’ll notice that the Scan Text button has shrunk to just an icon. It works the same, though.
- Although Live Text has more trouble with handwriting than printed text, it still does well enough that it’s usually worth accepting the scanned text and editing it later.
- Read through the entire recipe after scanning to make sure Live Text didn’t make any errors that will cause serious consternation, like interpreting a scrawled “¼ teaspoon salt” as “4 teaspoon salt.” Confusing “t” and “T” would also be bad. I haven’t noticed any errors along these lines in the recipes I’ve imported, but some are inevitable, particularly with handwritten notes.
Obviously, all that’s special about scanning recipe text is that many people have large collections of recipes on paper. Live Text will work its magic on any analog text you wish to digitize, whether into a dedicated app like Paprika or any app that accepts text input.
How have you leveraged Live Text for scanning text?
LastPass Shares Details of Security Breach
LastPass CEO Karim Toubba has announced that the password management company suffered a security breach last month, with attackers making off with unencrypted customer account data and customer vaults containing encrypted usernames and passwords.
This could be a nightmare situation for LastPass, but most users shouldn’t be at significant risk because the company’s Zero Knowledge security architecture prevents it from having access to or knowledge of a user’s master password—the stolen data doesn’t contain any master passwords. This safeguard should prevent the attackers from decrypting the stolen usernames and passwords.
LastPass has been fairly transparent about the breach, posting when it happened and following up this week with additional details. Although LastPass’s on-premises production environment was not breached, the attacker was able to leverage information captured in an earlier breach of a developer’s account in August 2022 to target another employee’s account in order to steal data from cloud-based storage that LastPass used for backup. (Arguably, these events are all part of a single breach.)
This incident highlights weaknesses in LastPass’s approach to security. The stolen data included unencrypted customer account information (names, addresses, and phone numbers, but not credit card details) and encrypted customer vault data. LastPass secures usernames, passwords, secure notes, and form-filled data using 256-bit AES encryption, and they can be decrypted only with a unique encryption key derived from each user’s master password. Within user vaults, however, website URLs associated with password entries weren’t encrypted. That’s problematic.
More seriously, LastPass relies entirely on that user-selected master password to secure encrypted data. Even though the company has hardened minimum requirements for setting passwords, users can set master passwords weak enough to be susceptible to cracking attempts. Apple’s iCloud Keychain, 1Password’s cloud-based storage, and some other solutions mix device-based keys with master passwords or account logins for far greater resistance—an attacker has to obtain and unlock a device in addition to compromising a vault or account password.
What Actions Should LastPass Users Take?
As long as you used your LastPass master password only at LastPass and retained the company’s default settings, LastPass does not recommend any actions at this time. (The defaults require a minimum of 12-character master passwords and specify a high number of iterations—100,100—in the PBKDF2 password-strengthening algorithm.)
A brute-force decryption might be successful against your master password if you reused it on another site that had been compromised, set one that’s fewer than 12 characters (never do that!), or lowered the default password-strengthening settings. (Some long-time users found that they had much lower settings of 500 or 5000 for the PBKDF2 algorithm—here’s how to check.) If any of those are true, change your master password immediately and turn on multifactor authentication. (Use the LastPass Authenticator app: for instructions, click Features & Tools and then Multifactor Authentication in the LastPass support portal.)
Because the vaults were stolen, nothing you do can protect the integrity of that data, which is already in the hands of the thieves. LastPass suggests people at risk of having their master password cracked consider changing passwords on stored websites. Start with the crucial accounts that could be used to impersonate you, like email, cell phone, and social media, plus those that contain financial data. If you’re worried, change passwords more broadly. (Typically, you never need to change unique, strong passwords, but here your core secrets were stolen, even if they remain encrypted.)
Those with weak master passwords should also change them and enable multifactor authentication for their LastPass accounts. Even though the horse is out of the barn, you can get a new horse and secure the door behind it: possible future breaches are less likely to affect you if you have updated the passwords stored in your vault and have secured them with a new strong, unique password.
Regardless of the strength of their master passwords, LastPass users must now be especially alert for targeted phishing attacks. Since LastPass vault backups did not encrypt website URLs, phishers can combine them with an email address associated with your unencrypted account information.
If you are at all uncertain that an email or text message that links to a login page isn’t legitimate, navigate to the website directly in your browser and log in using links on the site. Don’t trust URL previews—it’s too easy to fake domain names in ways that are nearly impossible to identify. Particularly watch out for credit-card warnings and package-tracking alerts—both are ready paths for phishers in the best of times and even more likely to fool users during the holiday season.
Questions and Concerns
Obviously, LastPass made mistakes here, but at least the company is being transparent about what happened. It doesn’t seem as though LastPass was cavalier about security—this sounds like a sophisticated, multi-prong attack that took months to carry out. It’s a worthwhile lesson for all organizations to realize that targeted attacks on one employee and then another ultimately allowed the breach of massive amounts of data. Nonetheless, the outcome raises questions and concerns.
Should LastPass users consider switching to another password management solution?
Yes, for two reasons. First, it’s troubling that LastPass isn’t using a secret key entangled with the master password to protect against thefts like this. Second, the attackers might be able to exploit the stolen information to compromise LastPass’s systems again. LastPass hardened its systems in response to the August breach of one developer’s account, but that wasn’t sufficient to stymie the November attack on the second employee.
Conversely, as far as we know, LastPass’s Zero Knowledge architecture remains secure, so if you’re comfortable with the strength of your master password and you trust LastPass’s overall architecture, you should be able to continue using it with no additional worry.
As someone who has used LastPass for many years as my primary solution—Tonya uses 1Password, and we share a family vault with Tristan—I’m not planning to switch based on this breach alone. However, I have been suffering from other irritations with LastPass—its multifactor authentication failing on the Apple Watch, its inability to remember that I want generated passwords to include symbols and be 20 characters long, and its Chrome extension frequently becoming corrupted (see “Chrome Extensions Disappearing? Click Repair,” 24 August 2021)—so I’ve decided to switch to 1Password when I find the time.
Is this breach an indictment of the entire concept of cloud-based password management services?
While some would undoubtedly say yes, arguing that locally managed passwords are not susceptible to attacks on a company, the issue has more to do with how cloud-based data is secured. While LastPass doesn’t hold the encryption keys to your data, its encryption method isn’t as strong as it could be because all the encryption power is locked in a single master password that can be entered anywhere, rather than requiring multiple components, some or all of which are held separately.
Swearing off cloud-based storage in favor of locally managed passwords also presumes you wouldn’t fall prey to phishing or other attacks that target you randomly instead of specifically. The LastPass breach required direct attacks on specific employees, but scattershot attacks can be automated or distributed broadly via malware—the attackers don’t know or care who their victims are.
Plus, cloud-based systems provide two compelling features: syncing among multiple devices and platforms and sharing particular passwords with other users of the same system. Syncing is fairly easy to replicate using iCloud, Dropbox, or the like, but sharing passwords with other people requires a shared account.
Are other password managers vulnerable to similar attacks?
I wouldn’t think so. The LastPass breach relied on previously stolen information that provided access to secondary backup storage thanks to credentials and information stolen in attacks targeting individual employees. It was a custom attack and couldn’t be used against other firms. And LastPass’s reliance on a single master password also puts its users’ data at unique risk.
That said, I have to assume that all password management services are under near-constant attack because, to paraphrase bank robber Willie Sutton, that’s where the passwords are. These companies may consider such attacks business as usual, or they may be using LastPass’s incident as an excuse to reexamine their security practices to make sure they haven’t missed anything. LastPass presumably didn’t think it had missed anything before August 2022.
When will passkeys eliminate problems like this?
I don’t know for sure, but the transition can’t happen soon enough. See “Why Passkeys Will Be Simpler and More Secure Than Passwords” (27 June 2022).